A Technical Overview of the Watch Duty Wildfire Monitoring Project Powered by RTL-SDRs
Previously in 2022 we posted about Watch Duty, a nonprofit organization aiming to improve access to live public safety information regarding wildfires in California. Several populated regions of California are extremely prone to wildfires, and it's important that residents get timely notifications about nearby wildfires so they can evacuate early and/or prepare their defensible spaces.
The system works by using RTL-SDRs to monitor public safety radio channels, and ADS-B aircraft positions of firefighting aircraft in order to gather information in real time about how wildfires are moving. Volunteers monitor this information and distribute anything of importance via a smart phone app to the public. Often the information is significantly more timely compared to official channels.
Recently Nick Russel, the VP of Operations at Watch Duty sent us a link to a technical overview blog post explaining how their 'Echo' remote monitoring devices work. The post describes how Echo devices consist of a Raspberry Pi and multiple RTL-SDR Blog dongles, with all the electronics being powered via Power over Ethernet (PoE). For the antenna a wideband Discone is used.
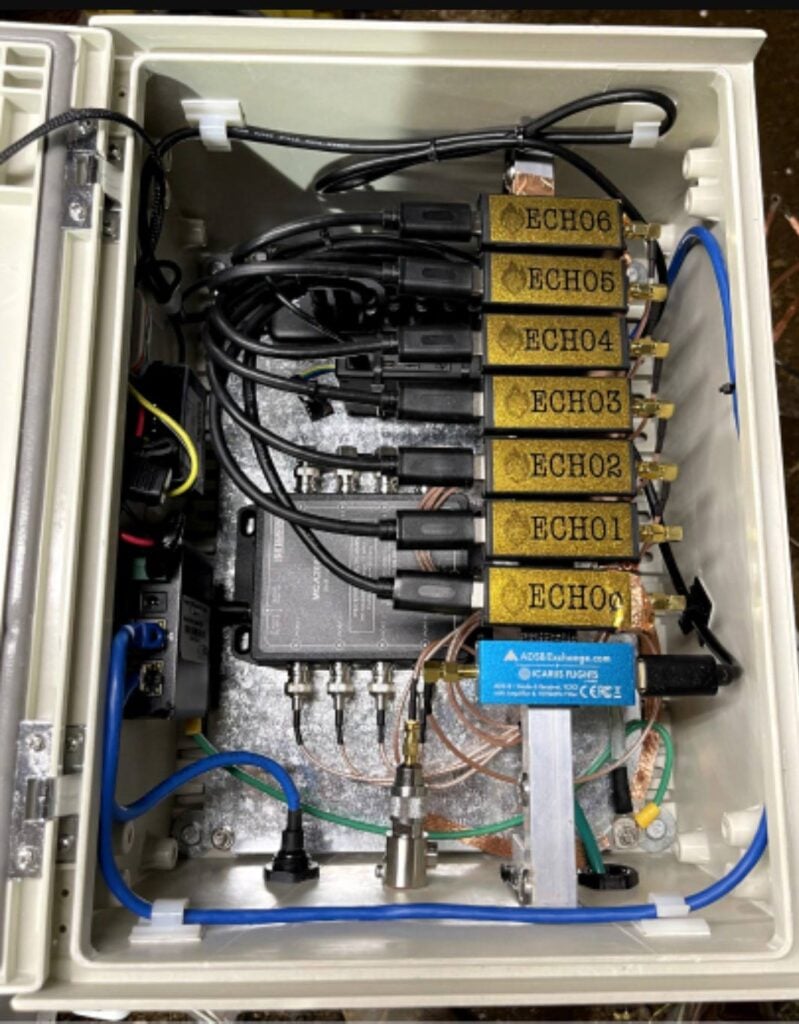
The rest of the post explains how their voice monitoring system works, how "tone out detection" works, which are orders for engines, strike teams, and other heavy equipment, how they make use of ADS-B data and how they are able to remotely maintain and update the system.
Importantly, Watch Duty note that they rely on volunteers and donations from the community, so please consider donating via the Watch Duty app.