SPECTRAL-GSM: A Web-Based GSM Interception Platform Built on OsmocomBB
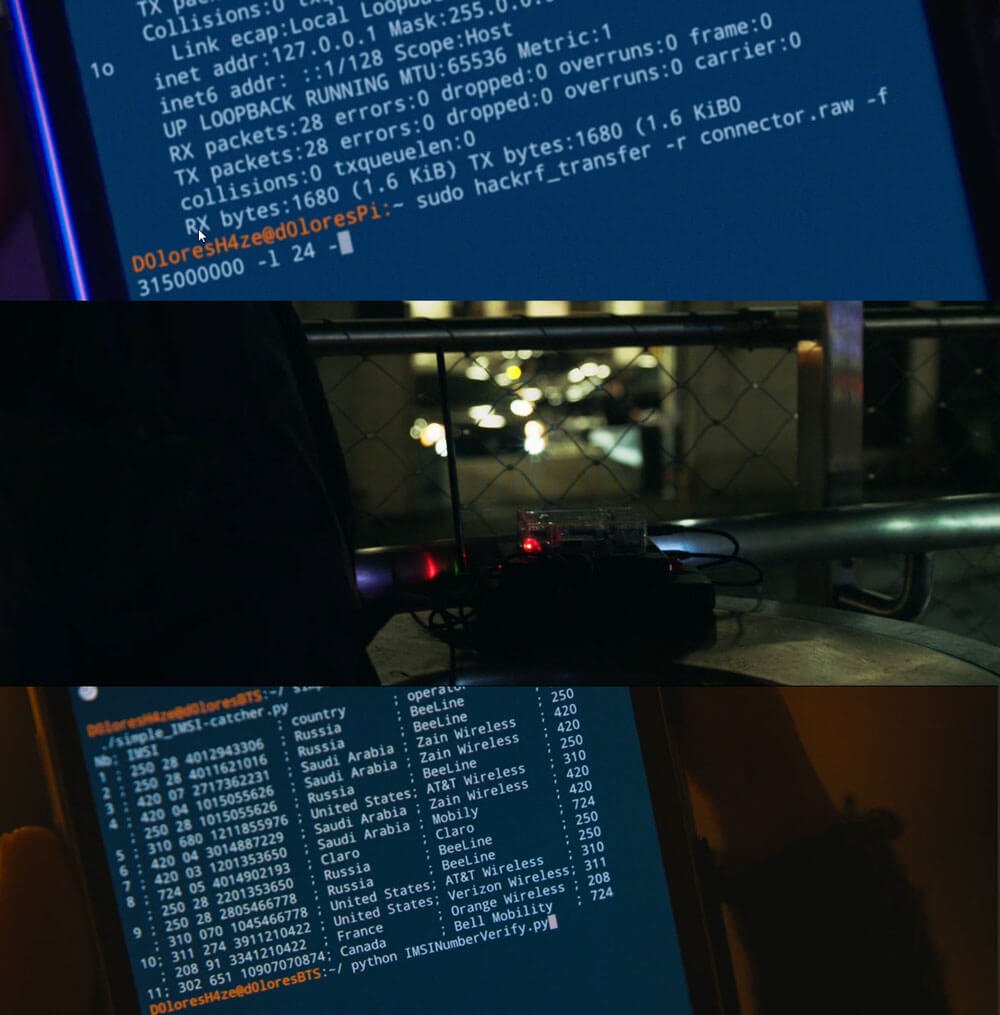
OsmocomBB is an open-source project that replaces the stock baseband firmware on old Motorola phones (C118, C139, etc.) that use the Texas Instruments Calypso chipset. By flashing custom "layer23" firmware over serial, these cheap legacy handsets become capable of accessing raw GSM radio data at the baseband level, enabling cell scanning, burst capture, and passive subscriber identity harvesting.
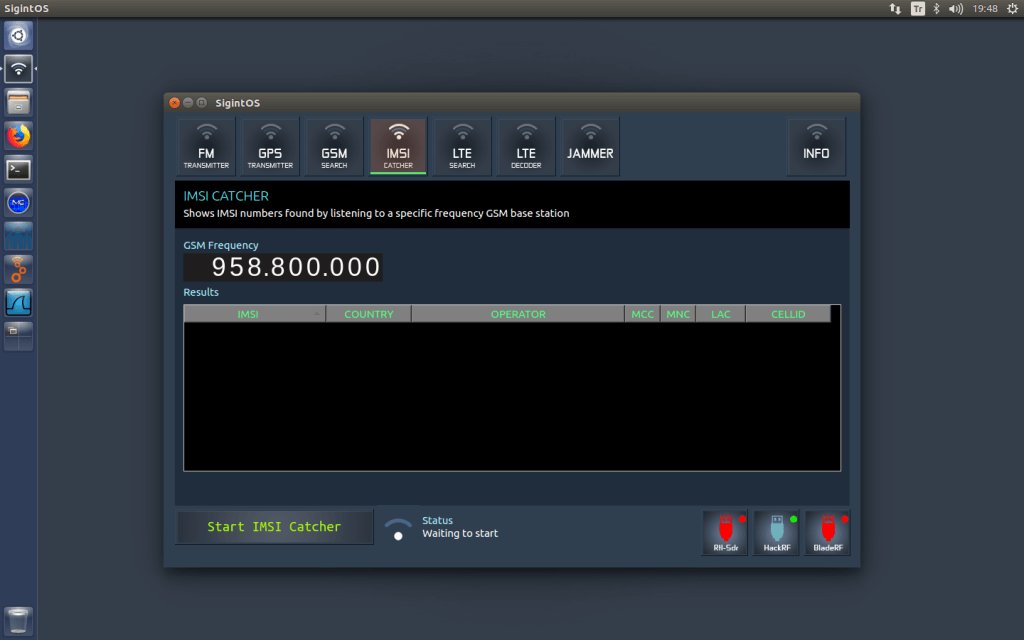
SPECTRAL-GSM builds on this by wrapping OsmocomBB into a full GSM intelligence suite controlled from a single browser tab. The system supports up to five phones simultaneously and provides a structured pipeline: scan local GSM cells, capture raw bursts on a target channel, crack the A5/1 encryption using rainbow tables on a 2 TB SSD, and then use the recovered session key for real-time voice and SMS decryption. Additional modules handle passive IMSI catching, targeted single-IMSI surveillance, silent SMS location probing via a USB modem, and OpenCellID cell tower mapping.
The developer notes that the platform is intended for authorized research, law enforcement, and educational use. At the moment, Mini0com has not provided a link or website to the software, only providing a PDF file, and video demonstrations of the system on their YouTube channel. Contact details for Mini0com can be found in the description on the YouTube videos below.