Hackaday Tutorial: A Crash Course in RF Modulation – ASK, FSK and LoRa Explained Simply
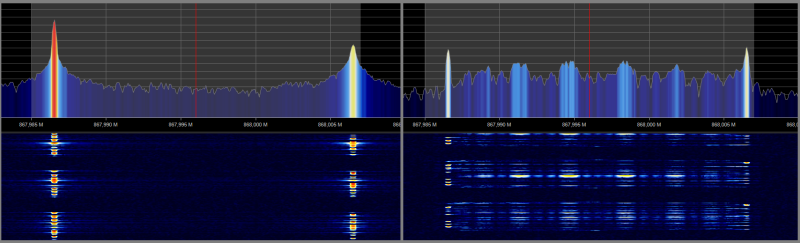
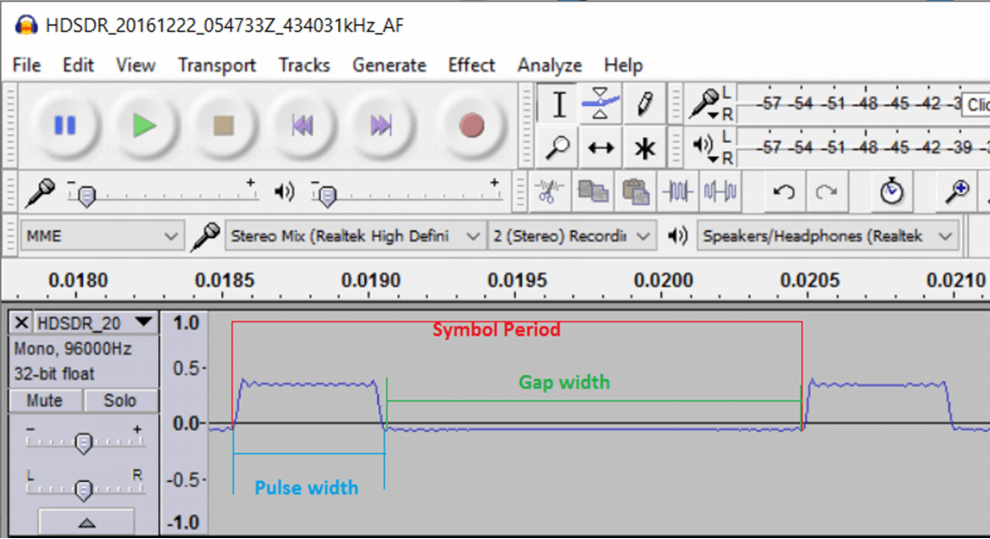
Hackaday writer Danie Conradie has recently posted a new tutorial explaining the difference between some common RF modulation choices. To do this he uses various RF hardware modules, and an RTL-SDR Blog V3 unit to view the spectrum of each modulation type. In the post he compares Amplitude Shift Keying (ASK), Frequency Shift Keying (FSK), and LoRa. He also explains the differences between ASK and OOK modulation, and FSK and GFSK modulation.
The key takeaways are that ASK modulation is simple, but prone to interference. FSK is less prone to interference, but requires more bandwidth. LoRa is good for receiver sensitivity and interference immunity, but comes at the expense of bandwidth efficiency. In addition LoRa modulation is patented, resulting in higher hardware costs.