Turning an Elecrow Pi Terminal into a Standalone SDR Radio with an RTL-SDR Blog V4
Over on YouTube Mirko Pavleski has uploaded a video showing how he took a US$199 "Pi Terminal-7” 1024*600 All-In-One Module Raspberry Pi" from Elecrow, and combined it with an RTL-SDR Blog V4 to create a portable standalone SDR radio platform.
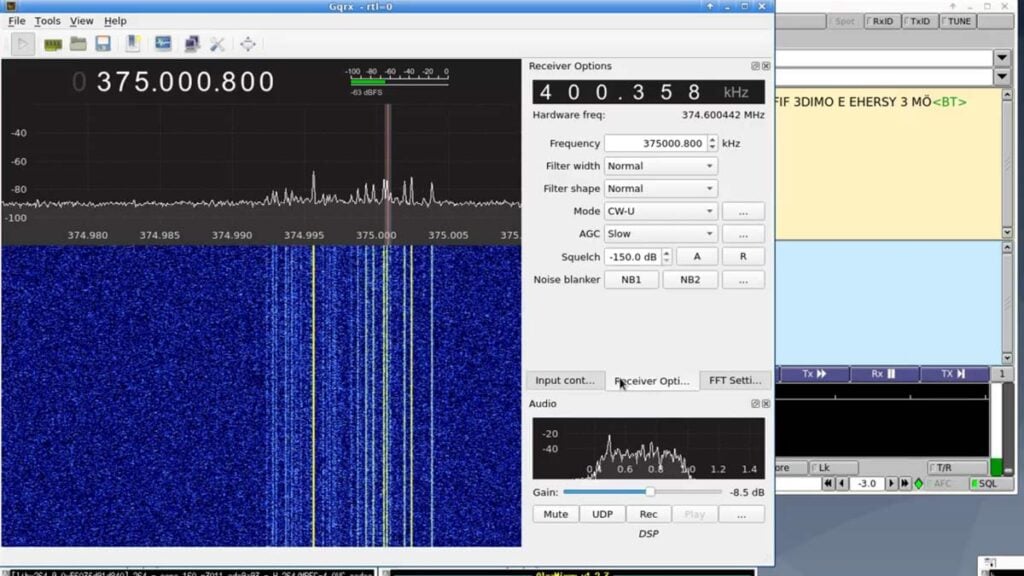
The build includes a cooling fan, external WiFi antenna, speaker, power switch and physical tuning knob. The built-in Raspberry Pi 4 compute module runs the HamPi image which includes multiple free SDR programs. In the video, Mirko shows the system in action with it running SDR++ and GQRX.
Mirko has also provided a text guide that explains how to replicate his setup.