Recently some videos from this years (mostly virtual) DEFCON 29 conference have been uploaded to YouTube. Defcon is a major yearly conference all about information security, and some of the talks deal with wireless and SDR topics. Some interesting talks that we've found from the main Defcon and Villages are posted below.
You can view all the talks directly as well as the many others via the main stage DEFCON YouTube channel, the ICS Village Channel, RF Village Channel and the Aerospace Village. There are also several talks from the Ham Radio Village recorded on Twitch. Did we miss any interesting talks? Please let us know in the comments.
Smart Meters: I'm Hacking Infrastructure and So Should You (Hash Salehi)
Why Smart Meters? This is a question Hash is often asked. There's no bitcoin or credit card numbers hiding inside, so he must want to steal power, right? Openly analyzing the technology running our critical infrastructure and publishing the findings is something Hash is passionate about. In the wake of the great Texas freeze of 2021, we can no longer "hope" those in power will make decisions that are in the people's best interest. This talk will present research on the Landis+Gyr GridStream series of smart meters used by Oncor, the largest energy provider in Texas.
Cyber attacks on Industrial Control Systems (ICS) differ in scope and impact based on a number of factors, including the adversary's intent, sophistication and capabilities, and familiarity with ICS and automated indutrial processes. In order to understand, identify and address the specific points that can prevent or stop an attack, a systematic model known as "Cyber Kill Chain" is detailed, a term that comes from the military environment and registered by the Lockheed Martin company. While most are familiar with terms and theoretical diagrams of how security should be implemented, in this talk we want to present live how an attack chain occurs from scratch to compromise industrial devices, the full kill chain, based in our experiences. The goal is to land these threats into the real world without the need to carry out these attacks with a nation-state budget.
DEF CON 29 - Paz Hameiri - TEMPEST Radio Station
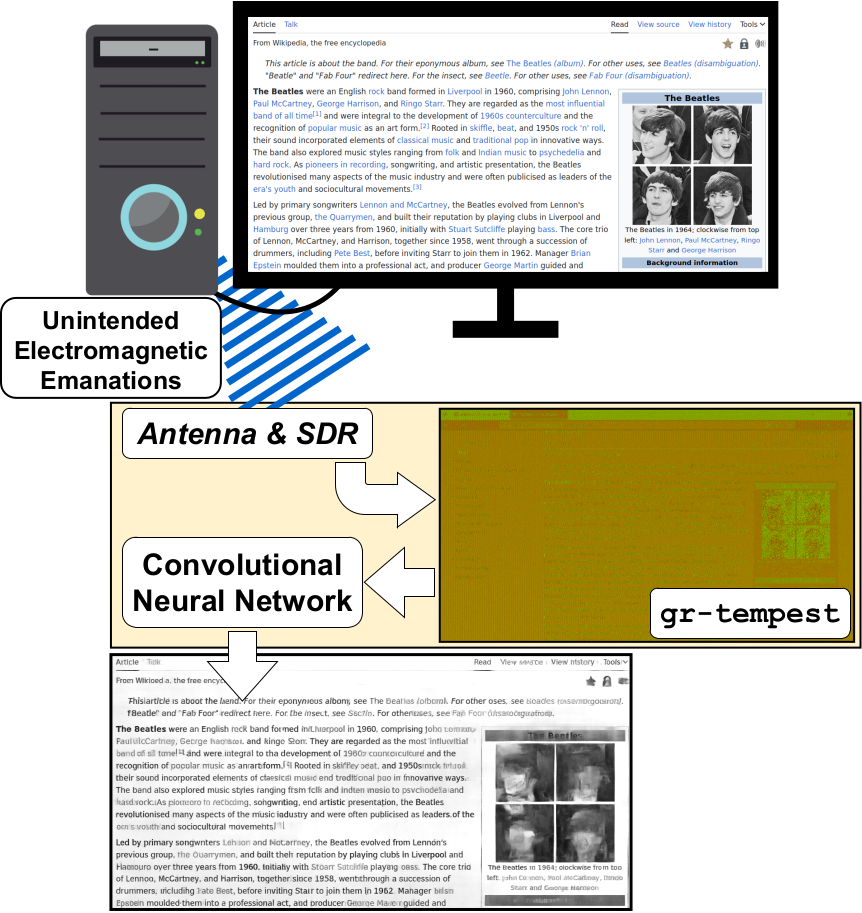
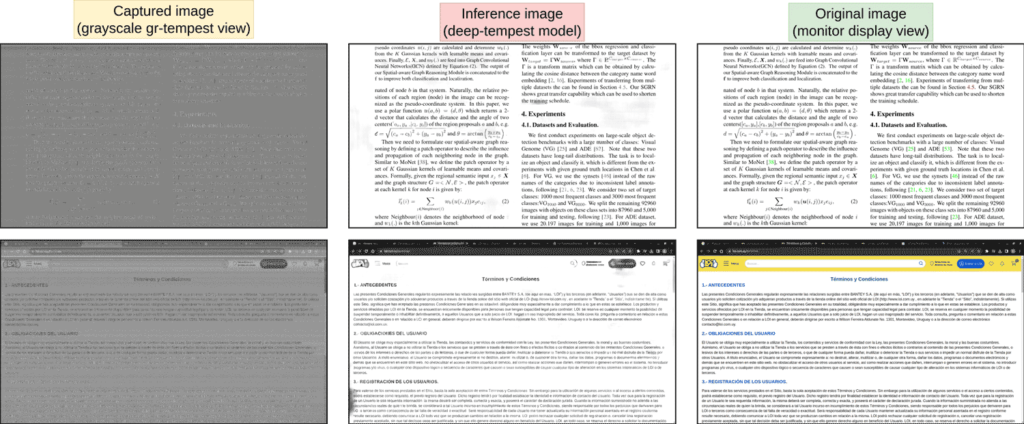
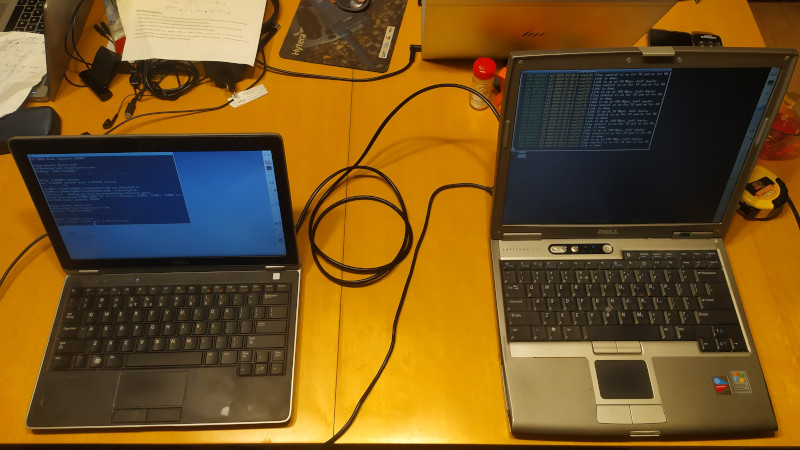
TEMPEST is a cyber security term that refers to the use of electromagnetic energy emissions generated by electronic devices to leak data out of a target device. The attacks may be passive (where the attacker receives the emissions and recovers the data) or active (where the attacker uses dedicated malware to target and emit specific data).
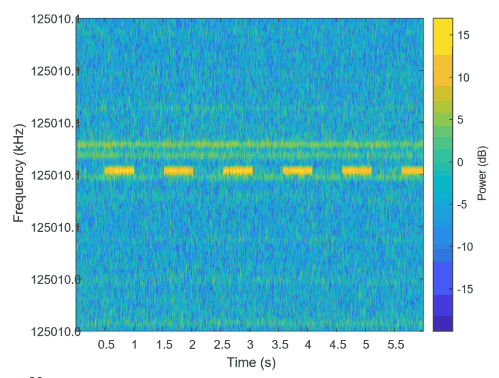
In this talk I present a new side channel attack that uses GPU memory transfers to emit electromagnetic waves which are then received and processed by the attacker. Software developed for this work encodes audio on one computer and transmits it to the reception equipment positioned fifty feet away. The signals are received and processed and the audio is decoded and played. The maximum bit rate achieved was 33kbit/s and more than 99% of the packets were received.
Frequency selection not only enables maximization of signal quality over distance, but also enables the attacker to receive signals from a specific computer when several computers in the area are active. The software developed demonstrates audio packets transfers, but other types of digital data may be transmitted using the same technique.
[Slides Link] [Whitepaper]
DEF CON 29 RF Village - cemaxecuter - RF Propagation and Visualization with DragonOS
"Today's presentation will start with a brief history of DragonOS, where it started and where it's at today. After a short introduction, I'll dive into the subject of visualizing RF propagation with DragonOS. I'll be showing a fresh OS install and the necessary steps to generate a rough estimate of a transmitter based on SRTM-3 elevation data, as well as a new feature enabling visualization/calculations of the path between transmitter and receiver .
Topics and hands on (pre-recorded) demonstrations will include the following,
- SPLAT! is an RF Signal Propagation, Loss, And Terrain analysis tool for the electromagnetic spectrum between 20 MHz and 20 GHz.
- Signal Server Multi-threaded RF coverage calculator
- Dr. Bill Walker's role
- Signal Server and DragonOS integration
- DF-Aggregator Developer / Modifications for visualization
I’ll conclude talking about future improvements to RF propagation and visualization tools."
Continue reading →