Decrambling Split-Band Voice Inversion with the Deinvert Tool
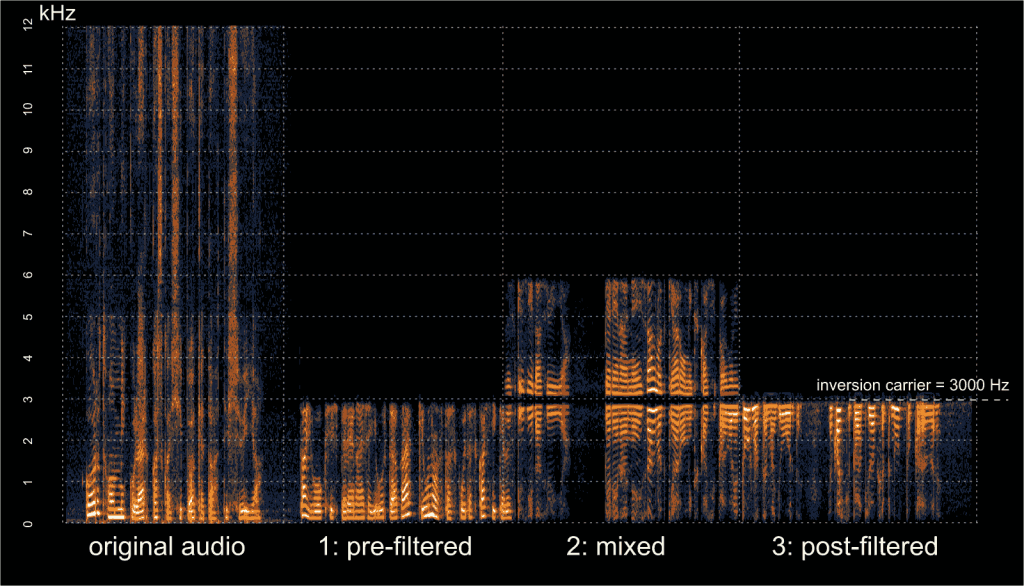
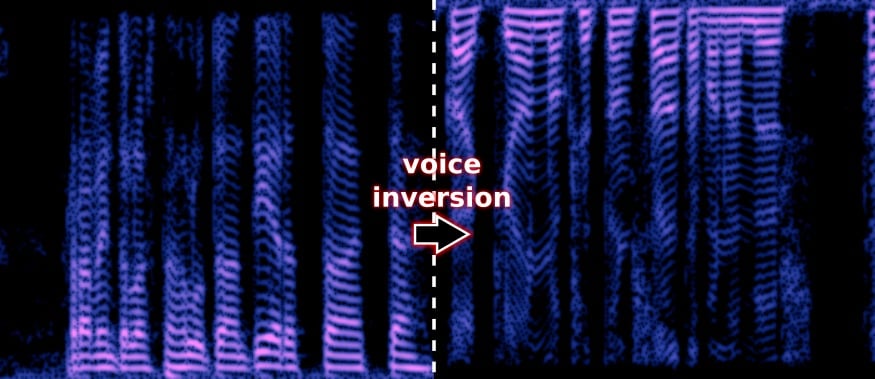
In early September we posted about Oona Räisänen’s deinvert which is a tool that can be used to unscramble voice audio that has had voice inversion scrambling applied to it. Voice inversion works by scrambling the voice frequencies so that a simple eavesdropper will have trouble listening in. A special descrambling radio is required to listen in. This provides very little real security, but may be enough to stop people with cheap scanners from listening in. Oona’s deinvert tool allows us to take a scrambled audio sample recorded with an RTL-SDR or any other radio and decramble the inversion.
In her latest blog post Oona explains how her deinvert software works and how it can also be used to decode the more difficult split-band inversion technique. She also writes that at the default quality level, the deinvert software is fast enough to run in real time on a Raspberry Pi 1.