Detecting Hidden GPS Trackers via Electromagnetic Unintentional Emissions with a HackRF
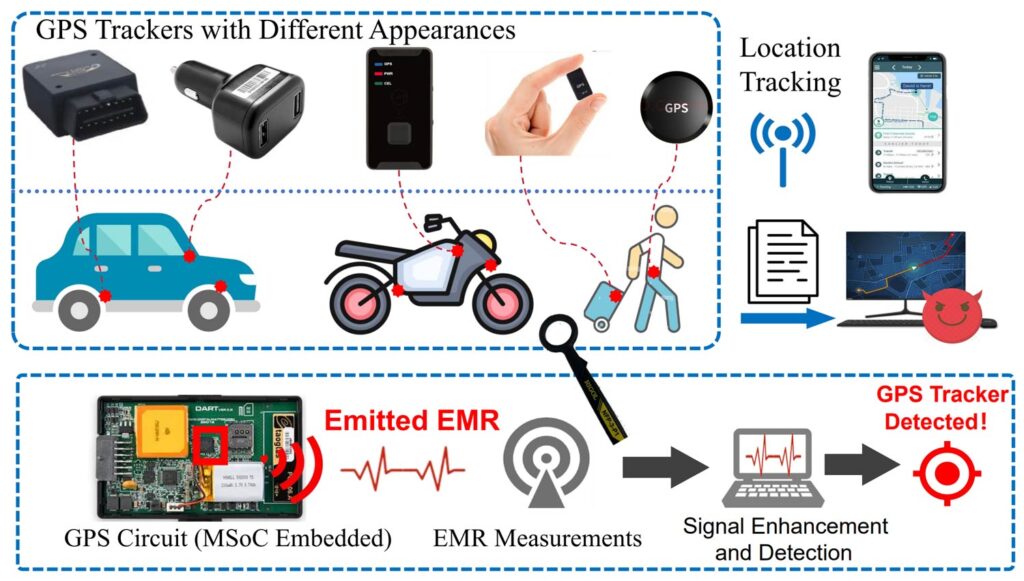
Researchers from Hunan University, Boise State, and UT Arlington have published a paper called "GPSBuster" (PDF link), demonstrating how a HackRF One can sniff out covert GPS trackers by their unintended electromagnetic radiation. Hidden trackers are hard to find since they only receive satellite signals and may store coordinates locally rather than transmit. Instead of looking for transmissions, GPSBuster targets side-channel leakage from the tracker's mixed-signal SoC, specifically the coupling between the quartz oscillator, local oscillator, and mixer used to downconvert the 1575.42 MHz L1 signal.
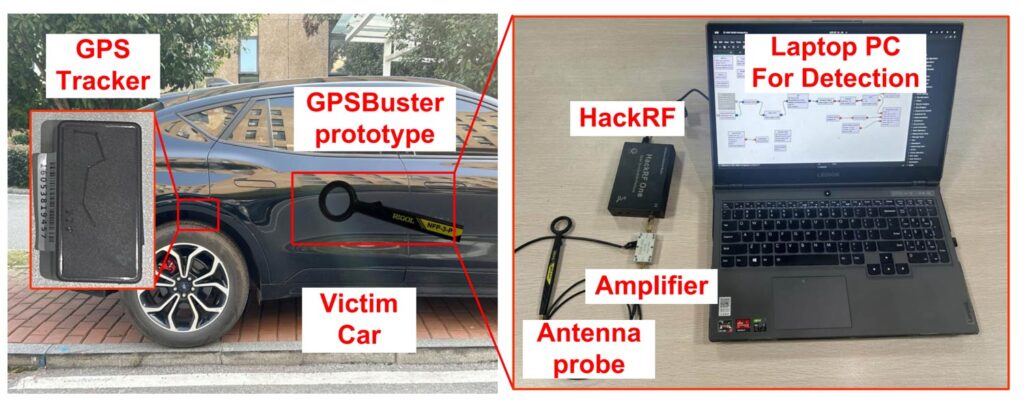
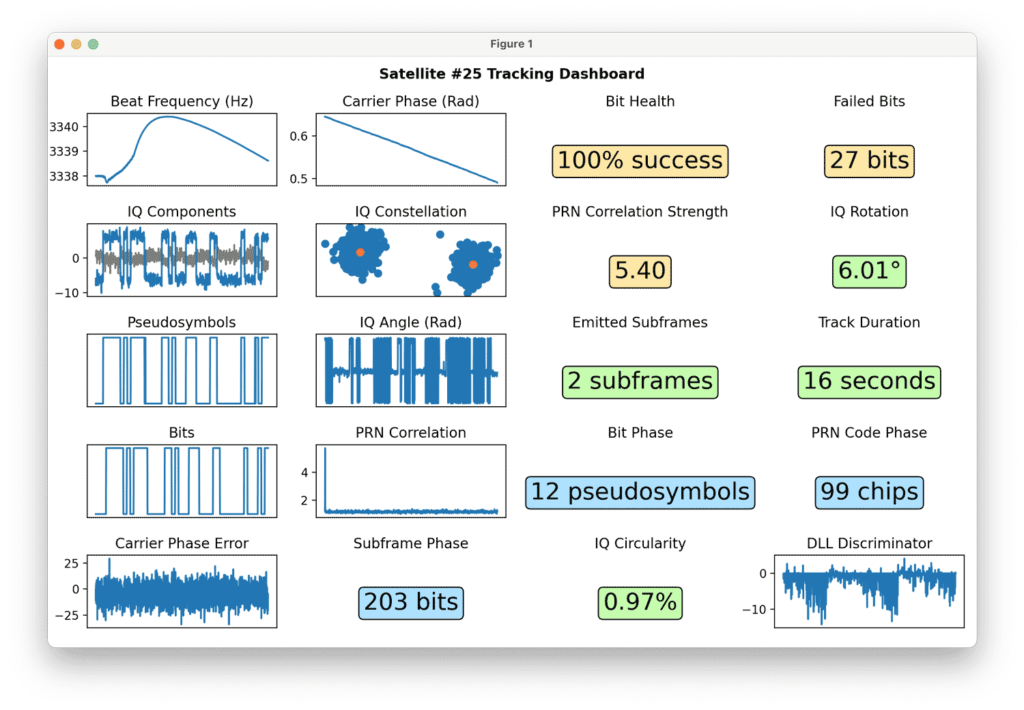
The team found that an active tracker leaks two characteristic spectra: a low band around 26 to 104 MHz and a high band around 1545 to 1625 MHz, each with a strong peak and evenly spaced harmonics. The low band reflects coupling between the quartz oscillator (typically 26 MHz) and the IF, while the high band contains LO plus IF spacing that always sums to 1575.42 MHz, giving a database-free detection rule. The setup consists of a HackRF, an NFP-3 near-field probe, and a 35 dB LNA. The use of the near-field probe means that sweeping the probe over an area to find the tracker is necessary, and the maximum detection range was 0.61 m.
Tested against the top 10 trackers available on a popular online marketplace, GPSBuster hit a 98.4% detection rate, working through plastic, cotton, canvas, and leather, and alongside phones, laptops, and speakers. It also extended to L1+L5 modules like the Quectel LC29H series, and even metal-shielded chips still leaked enough via PCB traces to be picked up.