Reverse Engineering a Wirelessly Controlled Adjustable Bed with a HackRF and Logic Analyzer
Over on his blog Chris Laplante has written up a post showing how he was able to reverse engineer his wirelessly controlled adjustable "TEMPUR-Contour Elite Breeze" bed. Originally the bed did have an Android App for smartphone control, however it was never updated since 2014 and so it no longer works on his modern Google Pixel device. So in order to have it controllable by his home automation system Chris decided to reverse engineer the wireless signal used by the bed's remote control.
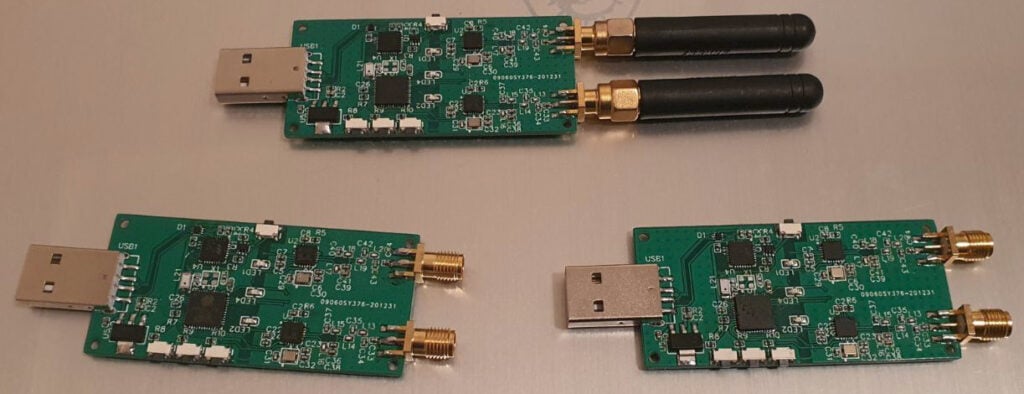
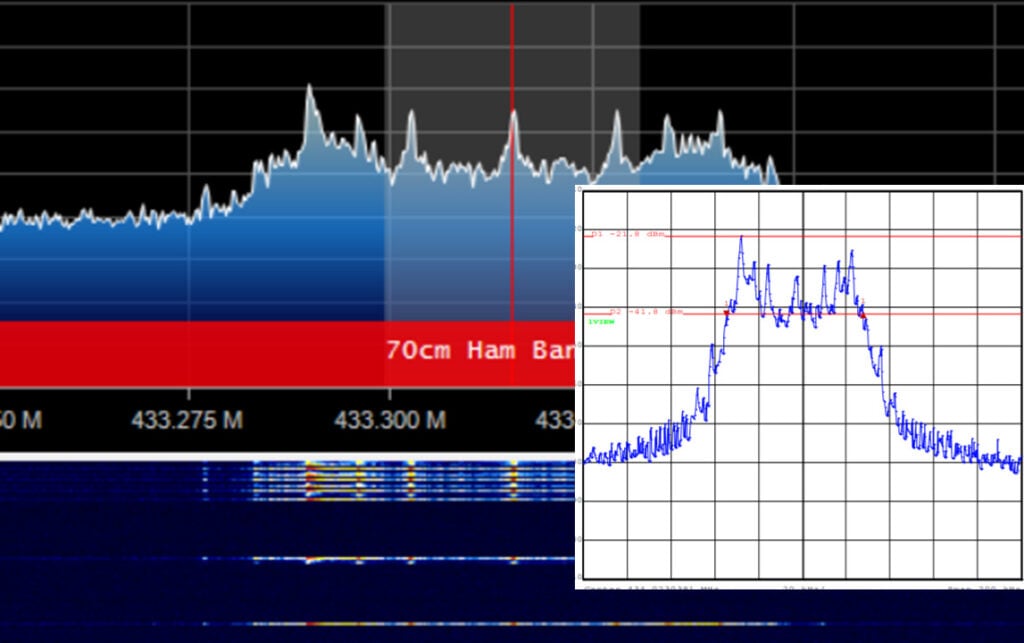
He first searched the FCC filing, finding that it transmitted in the ISM band at 433.050 to 434.790 MHz. Then using his HackRF he was able to capture the signal and determine that it used Gaussian frequency shift keying (GFSK) modulation.
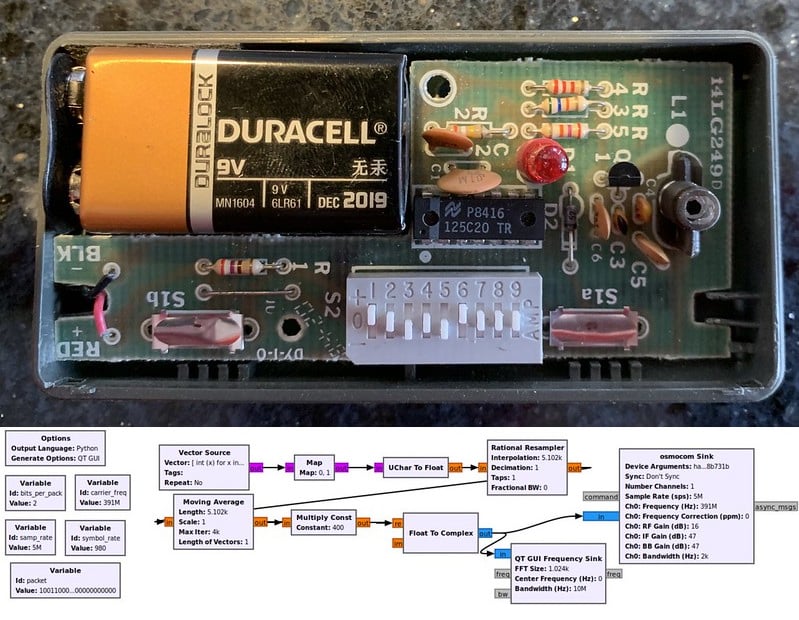
While the HackRF got him this far, he decided to follow a new line of investigation next, instead now using a logic analyzer to probe the SPI bus which talks to an Si4431 RF transceiver on the remote control. From this he was able to determine the important properties of the signal such as the frequency, data rate, frequency deviation, channel mapping and packet structure.
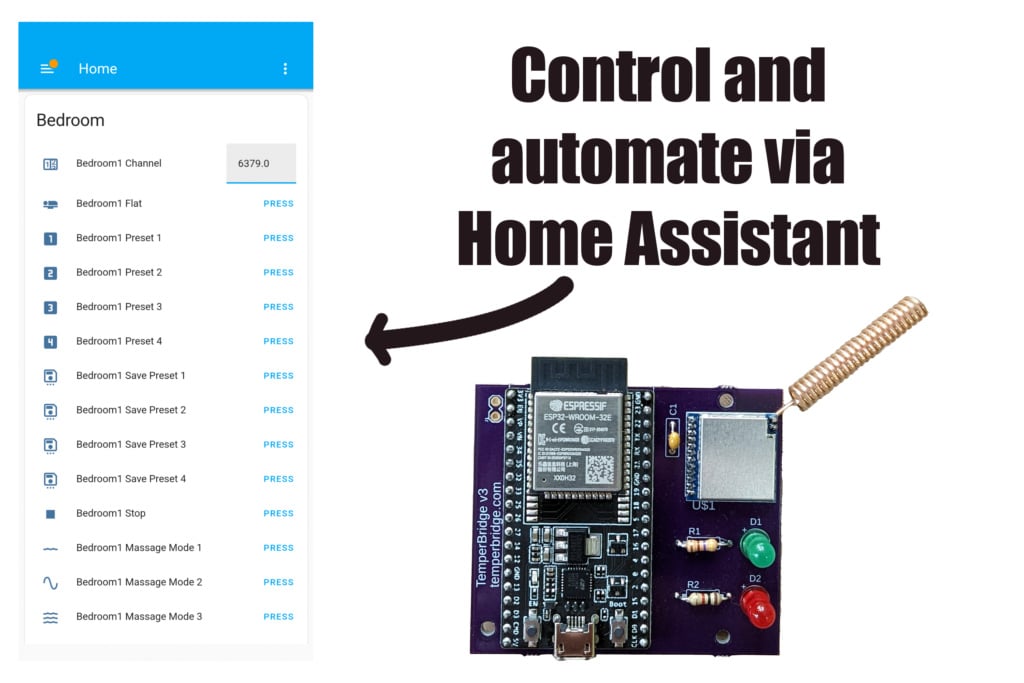
With all this information Chris was in the end able to create a product called "Tempur Bridge" that he is now selling on Tindie. It consists of an ESP32 WiFi connected microcontroller and a Si4463 RF transceiver chip. With his product Chris is now able to control his bed through a WiFi connection in Home Assistant.