Receiving ADS-B With a Semtech LR2021 LoRa Chip
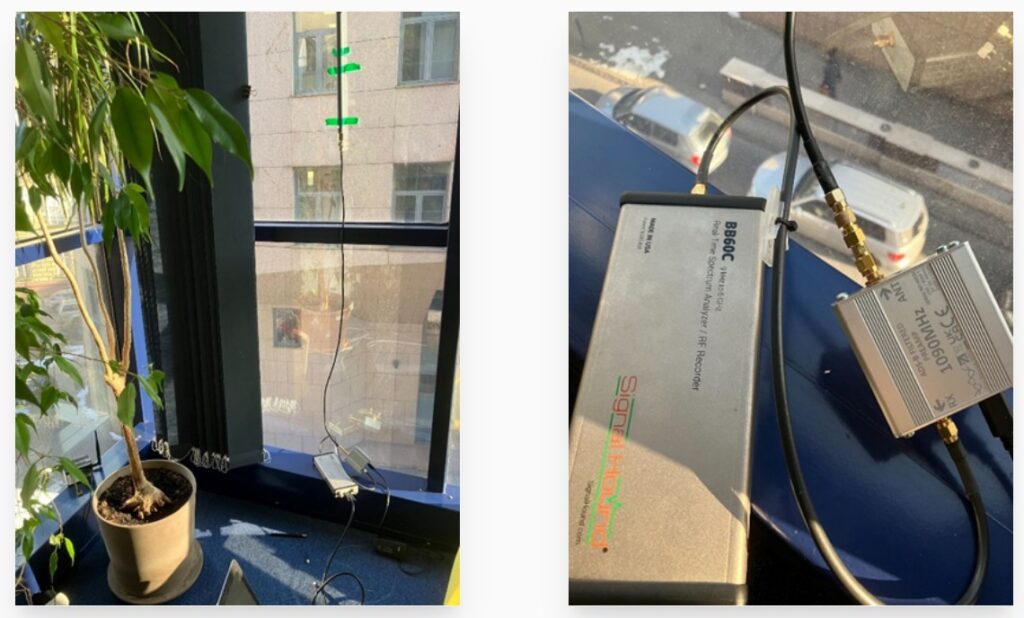
Over on his blog, Zoltán Papp and team have created an interesting write-up investigating whether Semtech's LR2021, one of the latest LoRa transceiver chips, which draws only 10.4 mA at 3.3V, can be used as a single-chip ADS-B receiver at 1090 MHz. The LR2021 natively supports OOK modulation, and the datasheet even hints at ADS-B reception. Building on prior work, the team captured live ADS-B signals with an SDR and replayed them into the LR2021 eval board for repeatable bench testing.
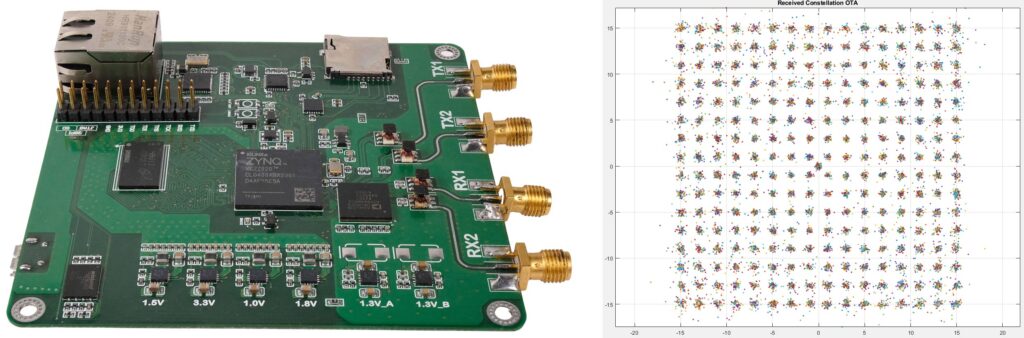
The initial 3 MHz Rx bandwidth configuration had only a 50% packet success rate with no reception above -50 dBm, because the AGC could not settle within the short 8 us preamble. Extending the sync pattern into the Mode S 'df' field enabled reception across the full dynamic range, but at the trade-off of broadcast message reception only. Manchester decoding and CRC also had to be moved to the host, since, for an unknown reason, Manchester decoding with inverse polarity would not work on the chip.
Measured sensitivity came in about 5 dB shy of the theoretical -89 dBm, with most of the gap blamed on the eval board's front end being matched for 868 MHz rather than 1090 MHz. The team notes that with a modified front end, the theoretical sensitivity should be possible.
With the rise in Raspberry Pi costs due to the consumer memory chip crisis, cheaper ADS-B receiver hardware is welcome. Some existing microcontroller-based ADS-B decoders that we've seen recently include ADSBee and PicoADSB.