Integrive-100: A Standalone MIMO SDR for Real-Time Precision
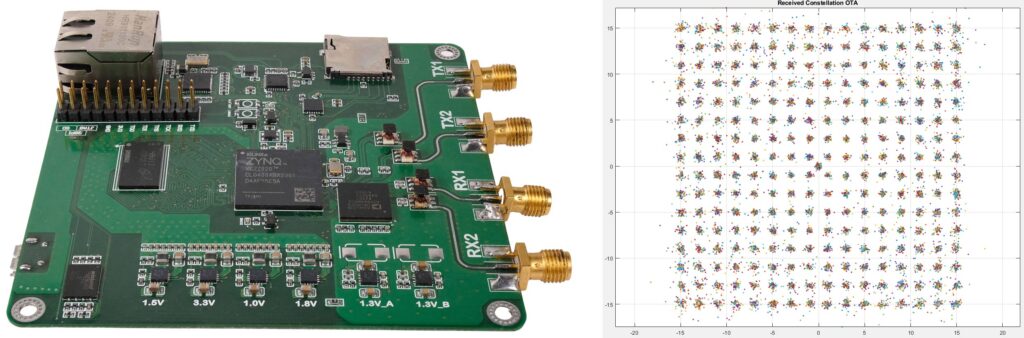
Thank you to Jayoung from HTWAVE for submitting news about the upcoming crowdfunding campaign for their "Integrive-100" software-defined radio. The Integrive-100 is an AD9361 based SDR with 70 MHz – 6 GHz tuning range, 2x2 MIMO TX/RX channels and up to 56 MHz bandwidth per channel.
They note a defining feature is a pre-built and validated FPGA-based PHY baseline with API access, allowing researchers to skip the basic infrastructure development steps and move straight to developing onboard DSP algorithms on the AMD Zynq-7020 FPGA/ARM CPU.
They write:
SDRs have long served as flexible testbeds for wireless communication research. Their ability to define functions through software makes them ideal for rapid prototyping. However, many SDRs struggle with non-deterministic latency caused by relying on a host PC for real-time signal processing where samples must traverse a communication interface and be handled by a non-real-time OS. This makes it difficult to accurately measure real-time performance, a fundamental requirement for 5G/6G research. This challenge is exactly why we decided to build our own SDR from the ground up.
By leveraging FPGA acceleration, we offloaded real-time signal processing entirely to the board, eliminating host PC dependency. While PC connectivity remains an option for monitoring and logging, the critical signal processing is handled on-board, ensuring that jitter is minimized and allowing you to test your algorithms in the most precise environment possible. Furthermore, by integrating an ARM processor and Embedded Linux, we’ve enabled high-level resource management and seamless compatibility with existing SDR software stacks.
In MIMO environments or scenarios involving high mobility, phase noise and phase synchronization are significant hurdles. Since our goal was industrial-grade deployment, we focused intensely on phase coherence. Unlike low-quality oscillators that degrade RF signal quality, we utilized high-performance components to achieve ultra-low phase noise and synchronized dual oscillators to ensure inter-channel phase consistency.
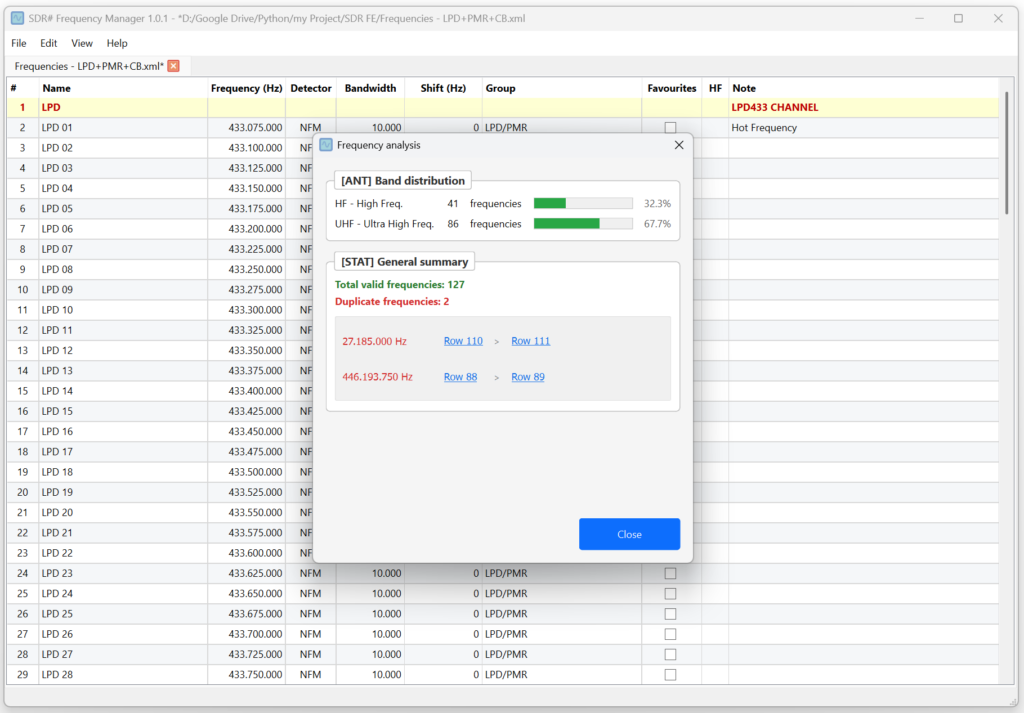
The best indicator of this stability is our OFDM 256-QAM constellation, which demonstrates the superior phase stability and synchronization our platform can achieve. Furthermore, our real-time video streaming demo, successfully transmitting high-throughput data with zero errors, stands as a testament to the integrity of our synchronization and phase noise control.
Finally, we provide robust API access (C, C++, Python), allowing users to control the system through simple function calls without needing deep FPGA expertise. By supporting standard software frameworks, researchers can easily port their existing projects to our hardware. Our goal is to eliminate the days or weeks spent on infrastructure setup. We want you to achieve productivity from Day 1.