RTL-SDR Now Runs on iPad M-Series Devices Directly via USB Without Jailbreak
Thank you to Arved (DK5AV/M0KDS) for writing in and sharing with us some exciting news. Arved has just announced his USBDriverKit extension for RTL-SDRs over on X and released it as open-source code on GitHub.
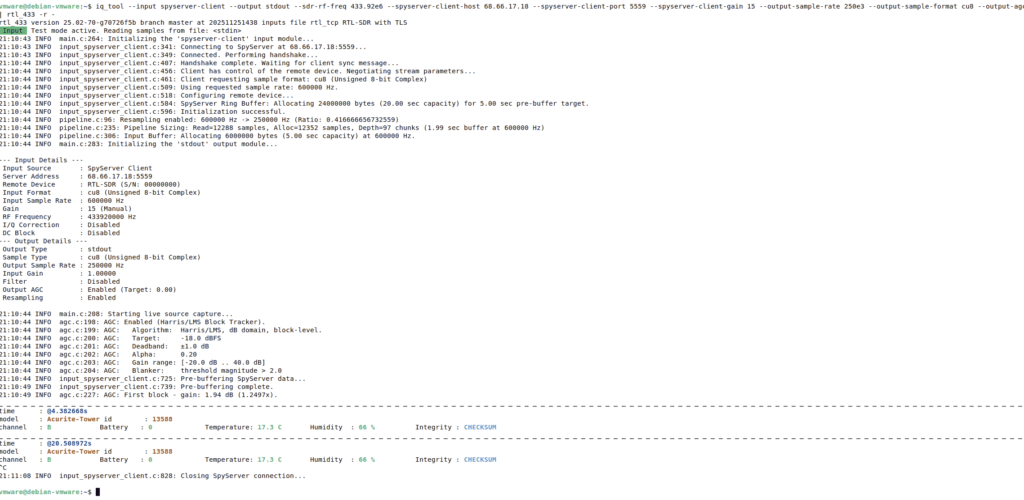
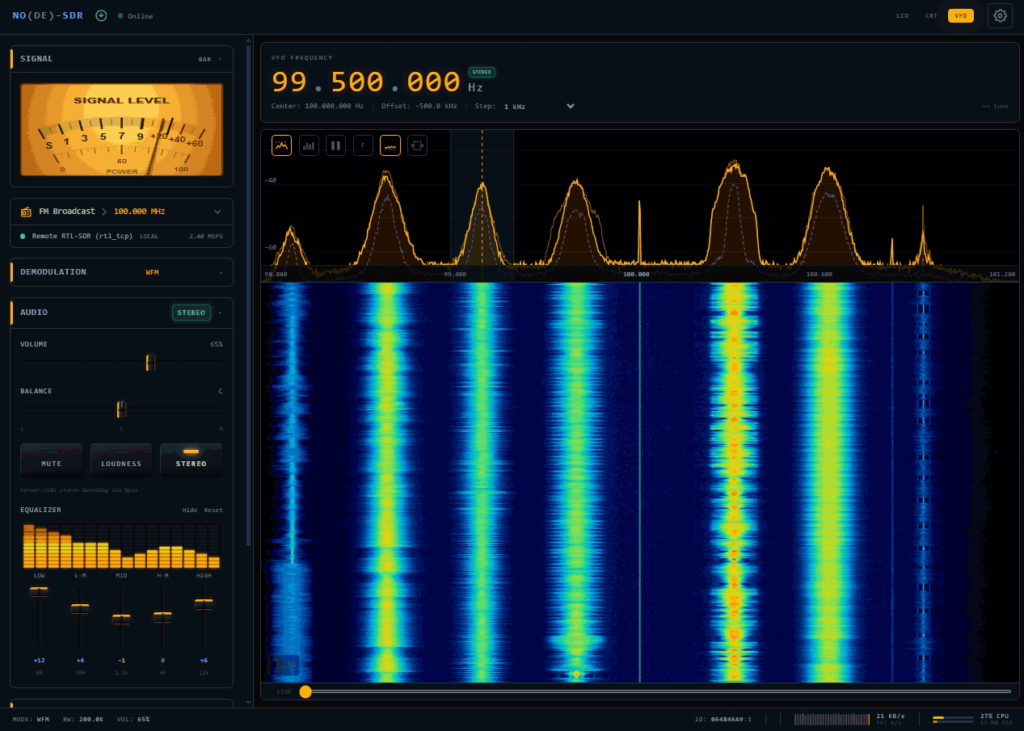
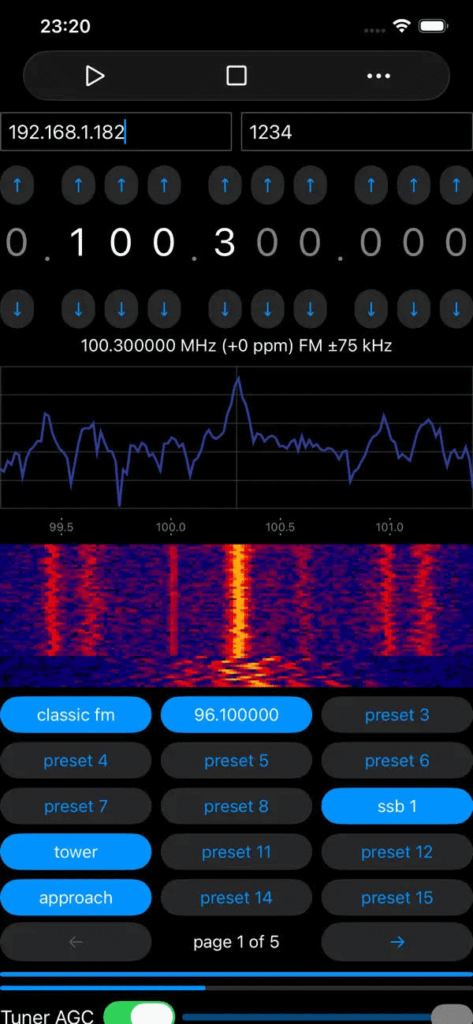
This is an unofficial port of librtlsdr, created using USBDriverKit instead of libusb, which is not available on iOS. This now allows RTL-SDRs to run directly on iPad iOS devices via USB without any jailbreak requirements. Previously, RTL-SDRs were unable to run on iOS devices directly. The only way around this was to run an RTL-SDR remotely and connect to it over a network via rtl_tcp.
The one caveat at this stage is that this currently only supports iPads with an M-Series SoC. At this time, only iPads use M-series chips, whereas iPhones currently use A-series chips. It also appears that the Blog V4 is not yet compatible with this driver due to the required EEPROM strings not being read by the drivers yet.
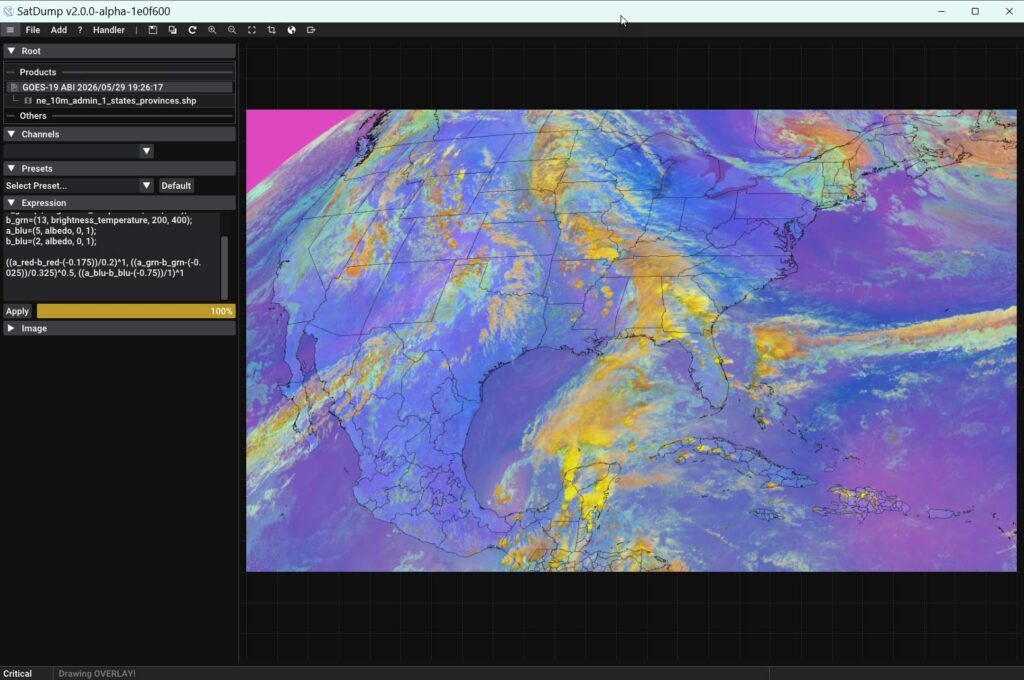
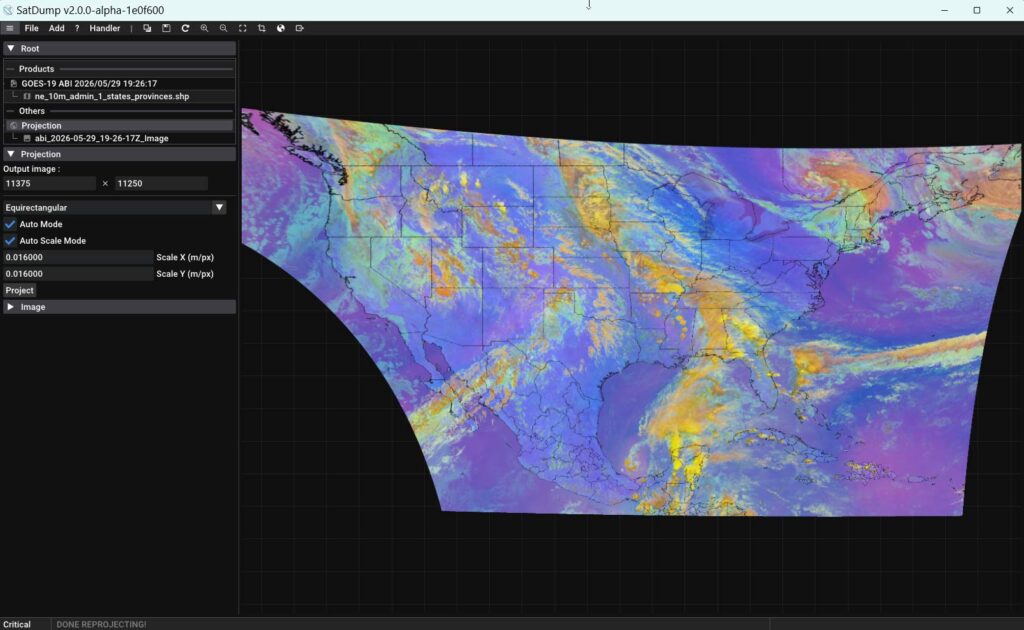
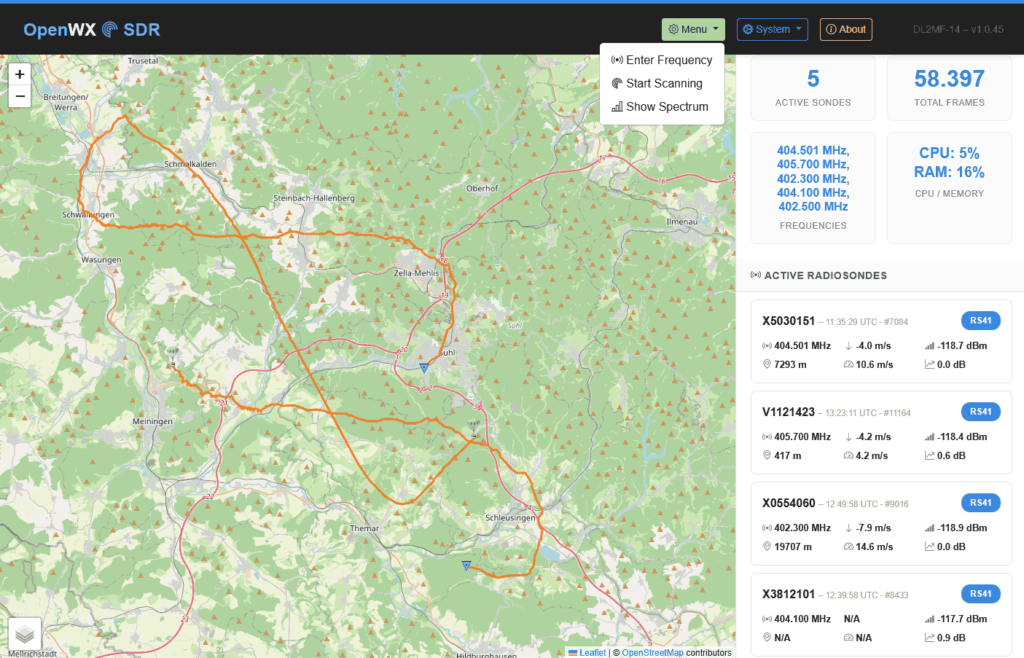
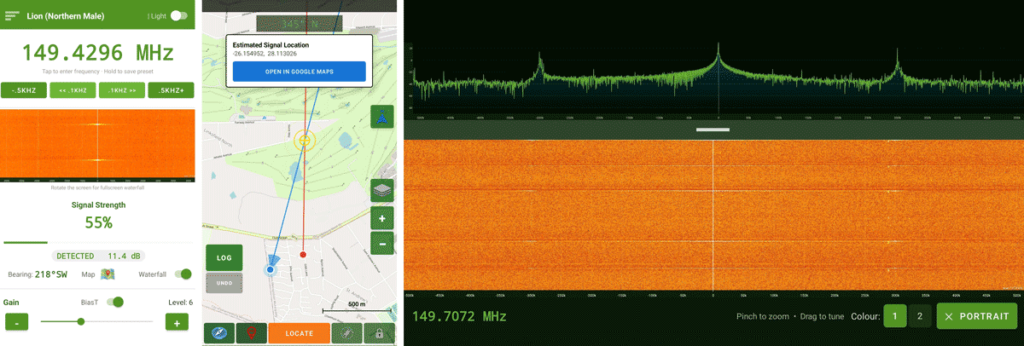
In the video embedded below Arved shows an RTL-SDR running on his M1 iPad, and demonstrates CoronaSDR, welle.io, SatDump and rtl_tcp running.
Arved has also released a video (embedded below), demonstrating SatDump connecting to an RTL-SDR and receiving a signal from a Meteor M2 LRPT weather satellite. He first records the IQ data with SatDump, then uses SatDump to decode the recorded data into an image.