Student Arrested in Taiwan for using SDR and Handheld Radios to Halt Four High Speed Trains with TETRA Hack
The Taipei Times has reported that a 23-year-old university student in Taiwan has been arrested after using a software-defined radio and hand held radio to hack into Taiwan High Speed Rail Corporation's (THSRC) internal radio communications and halt four trains mid-service.
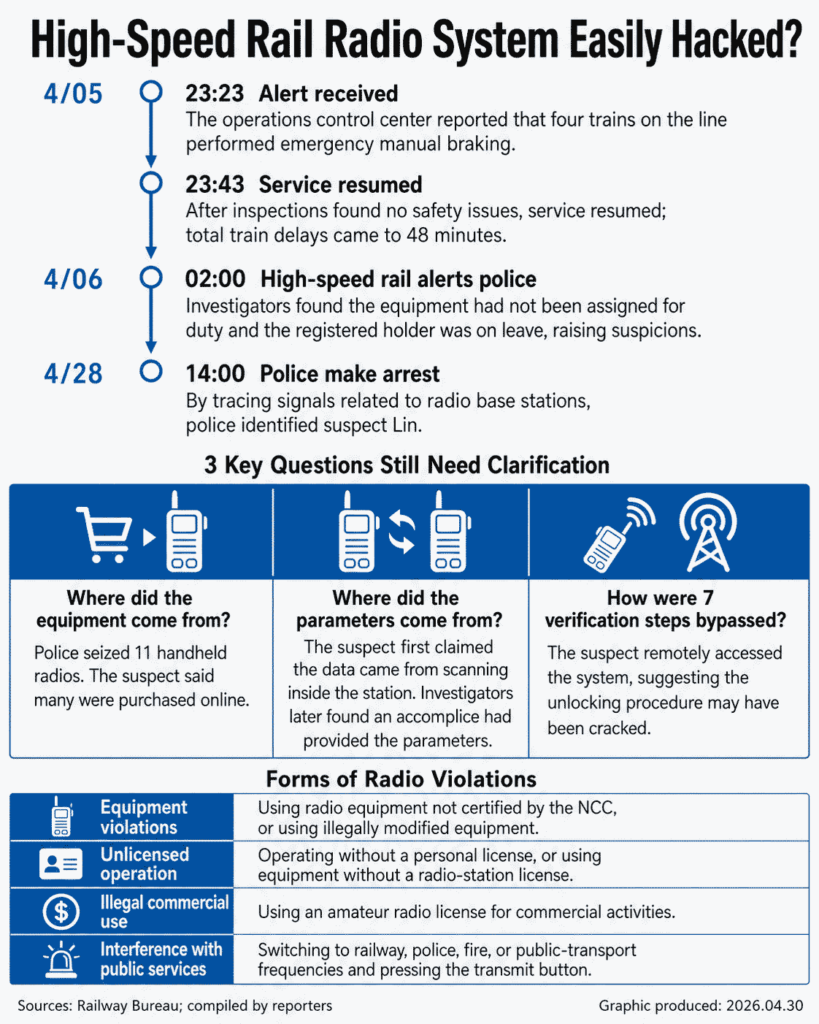
Chinese-language coverage from UDN and Newtalk fills in some details omitted in the English Taipei Times article. The system the student compromised is TETRA, and at 23:23 on April 5, 2026, the student transmitted a "General Alarm" (GA) signal, the highest-priority TETRA alert, which automatically instructs trains in the area to switch to manual emergency braking. Four trains were stopped for 48 minutes. THSRC's radio system has reportedly been in service for 19 years with seven verification layers, but parameters were apparently never meaningfully rotated over that period.
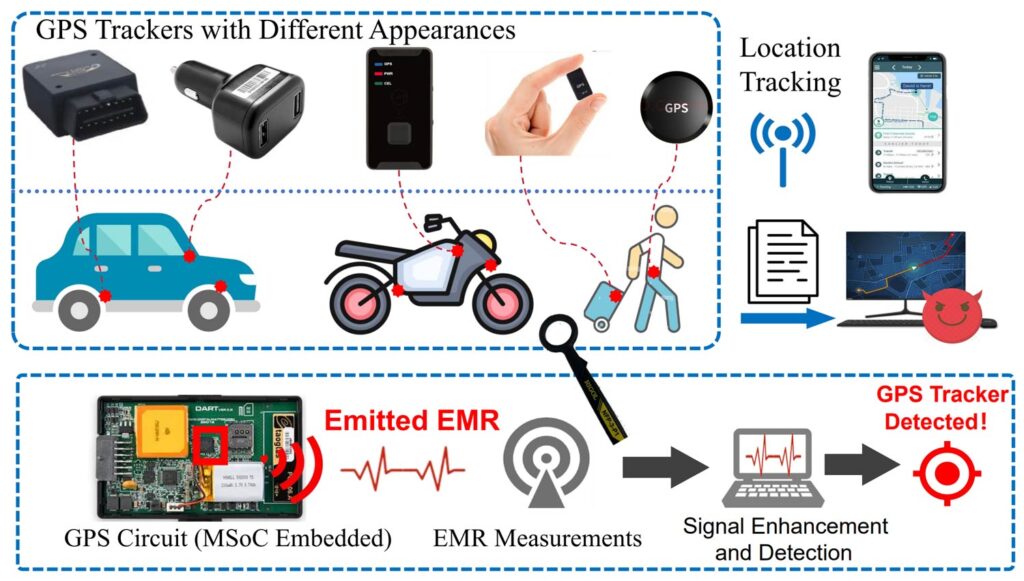
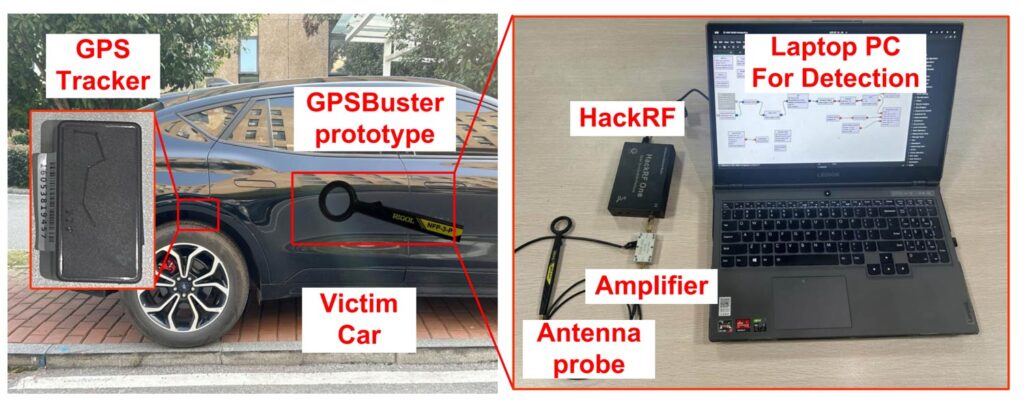
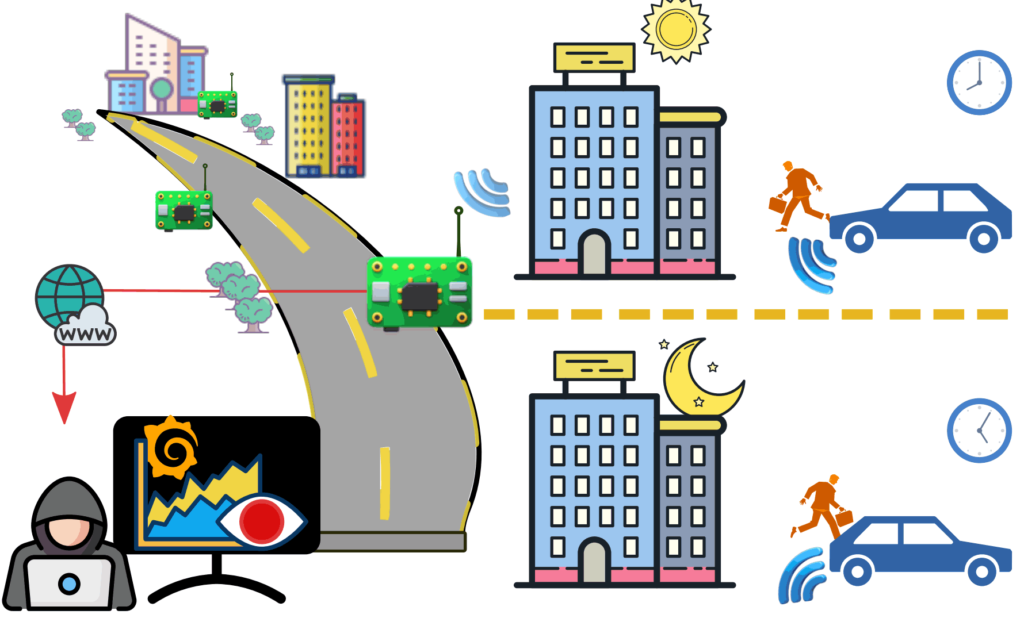
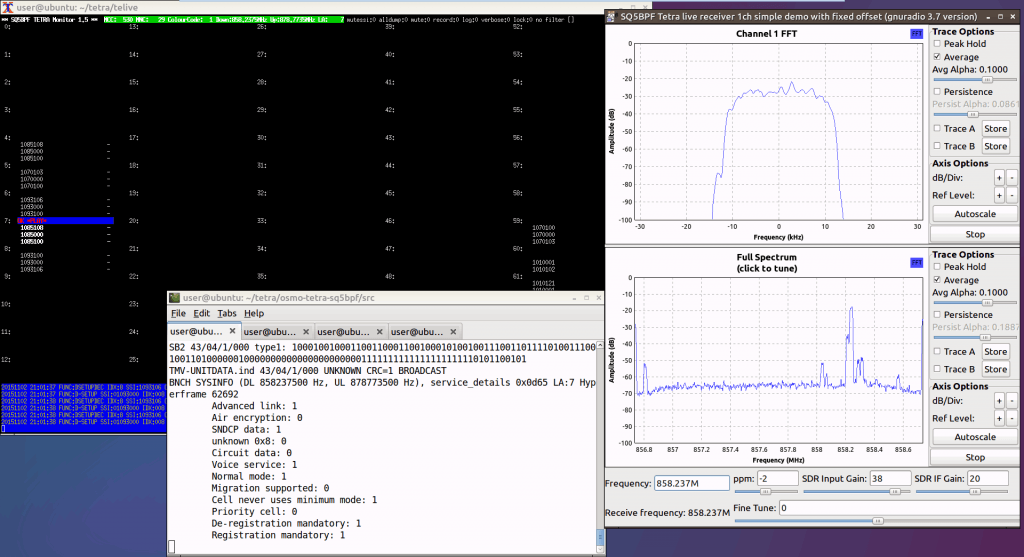
Police describe the suspect as buying an SDR online, connecting it between an antenna and a laptop, capturing THSRC traffic, and decoding the relevant parameters in software, then programming those parameters into one of his eleven handheld radios. A 21-year-old friend also allegedly supplied some critical THSRC parameters. The actual details of the 'hack' aren't entirely clear from the news articles. We suspect that the THSRC TETRA system is simply unencrypted, and that the student was able to spoof a legitimate signal. It's also possible that the THSRC TETRA system used TEA1 encryption, which is known to be broken.
Police located the student through a combination of network-side TETRA logs and CCTV. When the THSRC control center called back to verify the alarm, the person on the other end gave contradictory answers and then powered the radio off, prompting THSRC to audit their handheld fleet, confirm every issued radio was accounted for in its storage locker, and report to police that the parameters had been cloned.
Base station logs from the THSRC TETRA infrastructure (which record which sites received the uplink, with multi-site signal strength narrowing the origin) were used to localize the transmission source, and CCTV from around the coverage area was then used to identify the student and trace him to his rental unit. Search warrants on 28 April seized 11 handheld radios, a laptop, and the SDR.
He is currently out on NT$100,000 (3,200 USD) bail and faces up to ten years under Taiwan's Railway Act and Criminal Code, with an unconvincing "had it in my pocket and accidentally pressed the button" defense.
Stories like this are a reminder that experimenting with operational safety-of-life radio systems carries serious legal consequences. Back in 2016, we covered the case of Dejan Ornig, a Slovenian university student who used an RTL-SDR and the open source Osmocom TETRA decoder to discover that his country's police TETRA terminals were running unauthenticated, despite official documents stating otherwise. After seven years of court hearings, he ended up with a seven-month suspended sentence. More recently, we posted on the End of Train (EoT) vulnerability, where a security researcher demonstrated that an SDR can replicate the unauthenticated braking command on US freight trains.