OpenWXSDR: A Streamlined Automated Multi-Sonde Decoder for Raspberry Pi with RTL-SDR or Airspy
Thank you to Mike (DL2MF) for writing in about the release of OpenWXSDR, a new open-source Python framework that turns one or more RTL-SDR dongles or Airspy SDRs into a fully automated radiosonde ground station running on a Raspberry Pi 4/5 or Linux x86 machine.
If you are unaware, a radiosonde is a lightweight instrument package typically carried by a weather balloon to collect atmospheric data, including temperature, humidity, pressure, and GPS position. It transmits this data back to the ground via radio signals. Using an RTL-SDR or another software-defined radio (SDR) along with appropriate decoding software, hobbyists or researchers can receive, decode, and visualize these signals. Radiosondes are typically launched by local meteorological agencies in many cities worldwide at least twice per day.
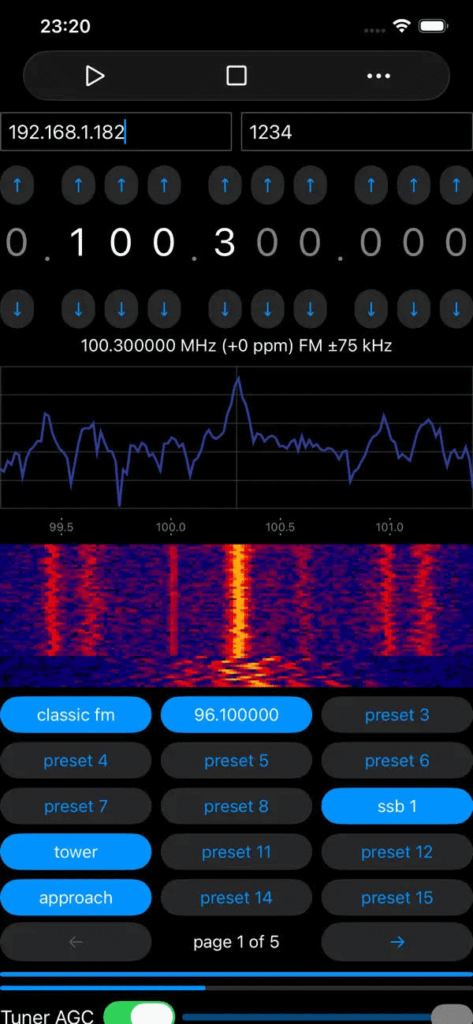
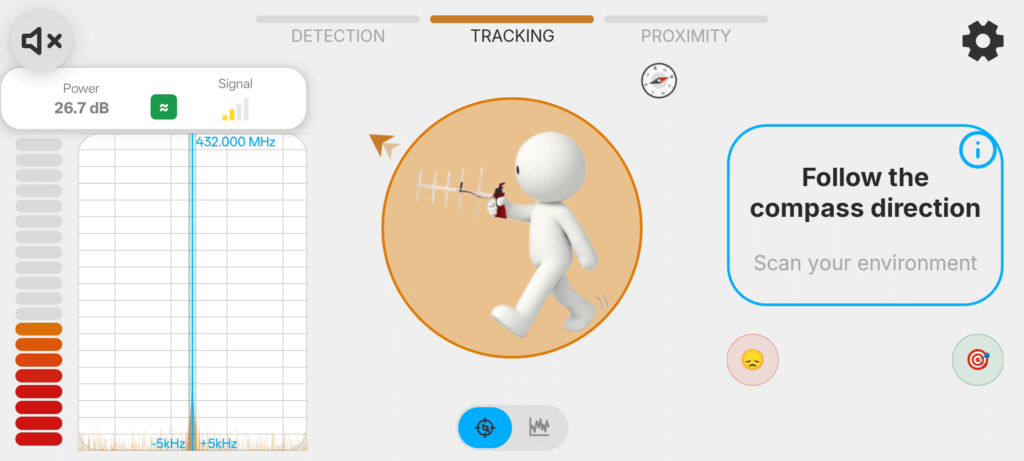
OpenWXSDR continuously scans the 400-406 MHz meteorological band, automatically identifies balloon transmissions using DFT correlation analysis, and spawns dedicated rs1729 decoder subprocesses. Supported sonde types include RS41, RS92, DFM06/09/17, M10, M20, iMet-54, LMS6, and MRZ.
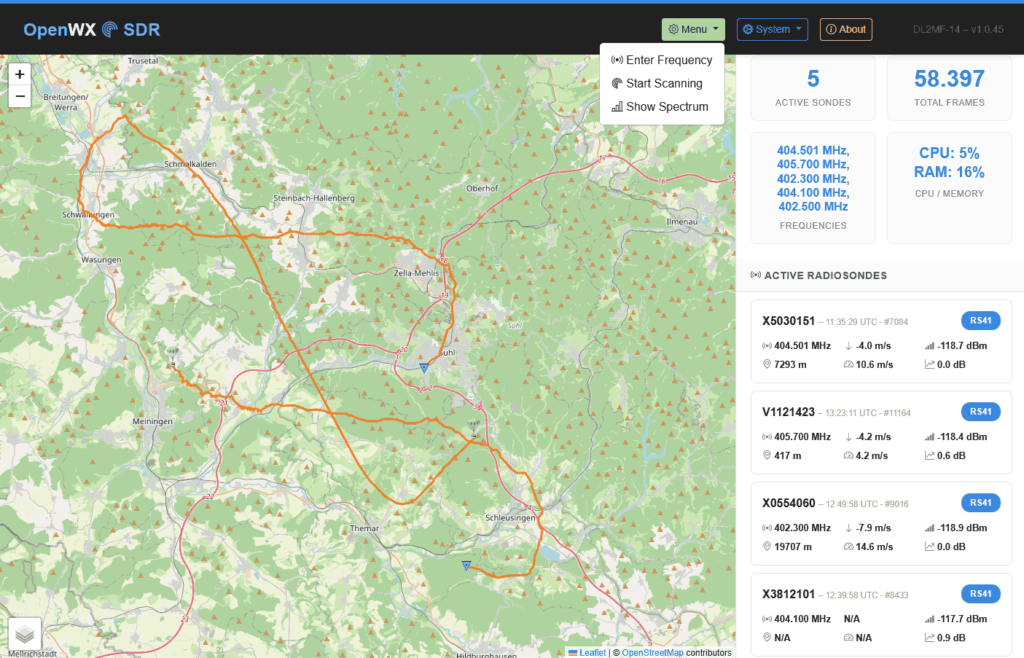
The software also supports multi-sonde and multi-SDR. While one dongle scans for new signals, others simultaneously handle active decoding sessions. Decoded telemetry can be submitted in parallel to SondeHub v2 and to OpenWX.de via MQTT (with optional TLS), and as Horus-compatible UDP JSON datagrams for local tools like SondeMonitor. A built-in Flask and Leaflet web interface shows live positions, flight tracks up to 20,000 points, PTU sensor readings, and signal metrics, with most settings editable from the WebUI during operation.