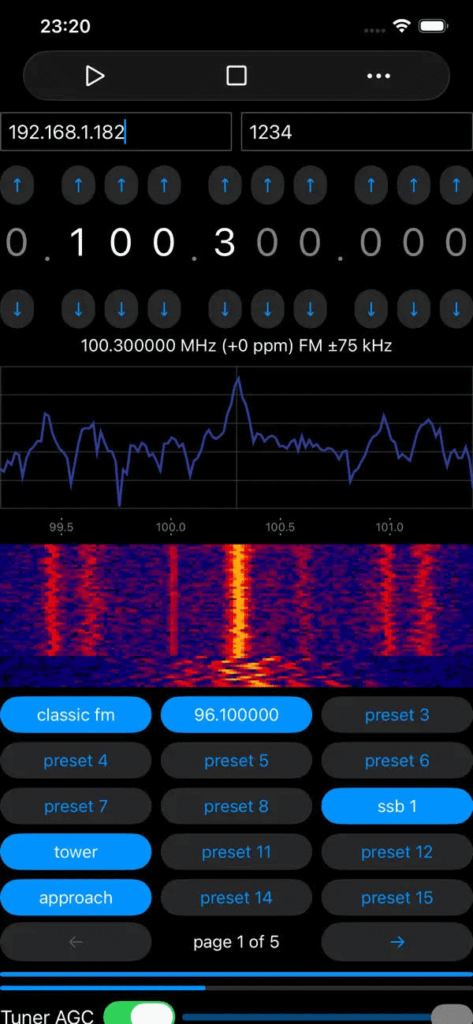
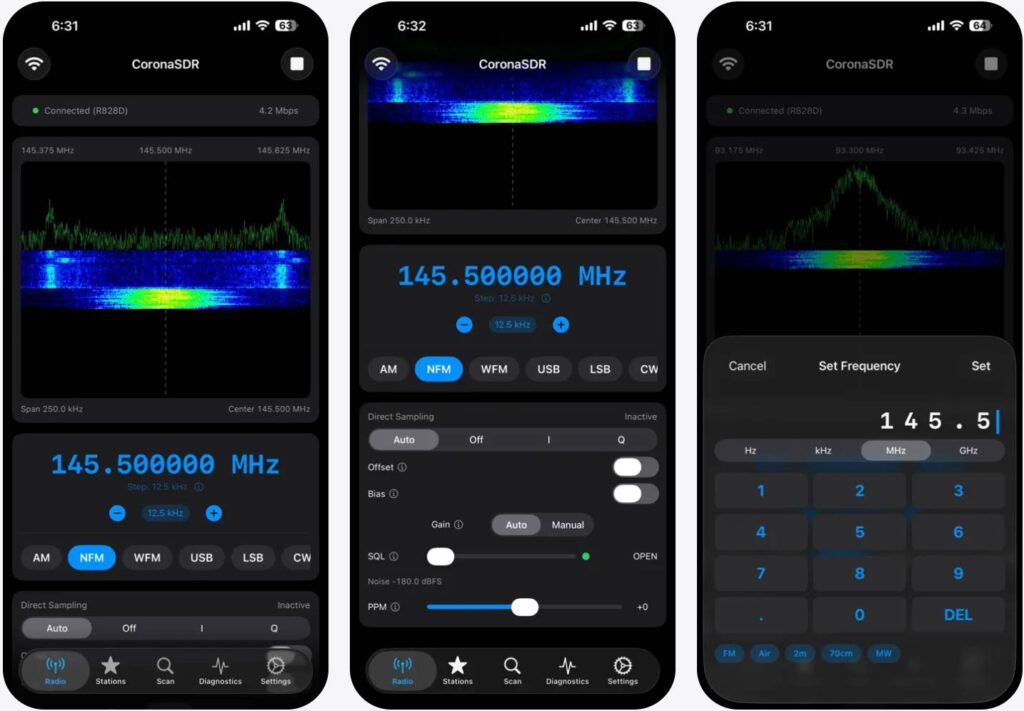
Spectrum SDR Android App Ported to iOS
Thank you to James Mainwaring of Knowle Consultants for submitting news about the release of an iOS port of his previously Android-only "Spectrum SDR" app for RTL-SDR. Knowle Consultants have previously released a range of RTL-SDR Android apps for FM, Airband, Ham FM and ADS-B reception. James writes:
As most people will be aware, it is not currently possible to connect an RTL-SDR dongle directly to an Apple mobile device. So the app is designed to be used with an instance of rtl_tcp running on a Mac, PC or maybe a raspberry pi.
It is also possible to install the app directly on an Apple Silicon Mac, so that is one with an M1, M2, ... etc. In that situation obviously rtl_tcp can be hosted on the same Mac too if needed.
Anyone needing help with this app or any of our existing Android SDR apps should contact [email protected]For comparison, the Android version is available here: