Reverse Engineering a 30 Year Old Wireless Garage Door Opener with a HackRF and GNU Radio
At his childhood home Maxwell Dulin discovered that his garage door was controlled by a 30 year old system called the "Sears Craftsman 139.53708 Garage Door Remote". Being interested in SDRs Maxwell decided to see if he could reverse engineer the remote using his HackRF.
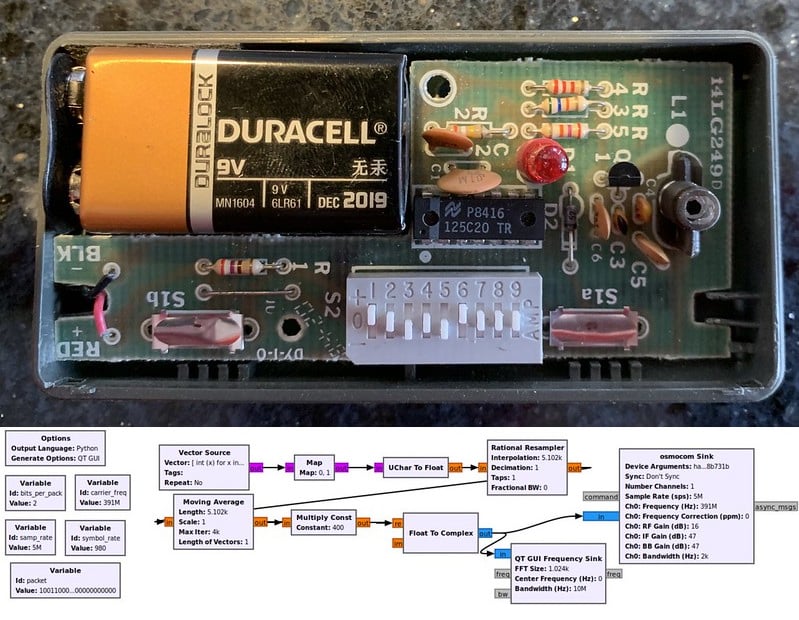
His first steps were to search for the frequency which he found active at 390 MHz. He then moved on to analyzing the signal with Inspectrum, discovering the OOK modulation, then working his way towards the binary control strings. One thing that helped with his reverse engineering was the use of the 9-bit DIP switches on the remote that configure the security code that opens up a specific door as this allowed him to control the transmitted bits, and determine which bits were used for the security code. With this and a bit of GNU Radio code he was able to recreate the signal and transmit it with his HackRF.
Finally Maxwell wanted to see how vulnerable this door is to a brute force attack that simply transmits every possible security code. Through some calculations, he discovered that brute forcing every possible security code in the 9-bit search space would only take 104 minutes to open any garage using this opener.