Iridium-Sniffer: A Standalone Iridium Satellite Burst Detector and Demodulator
Thank you to Aaron, who is most well known for creating the DragonOS distribution, for writing in and sharing with us a new open-source program he's recently released over on GitHub.
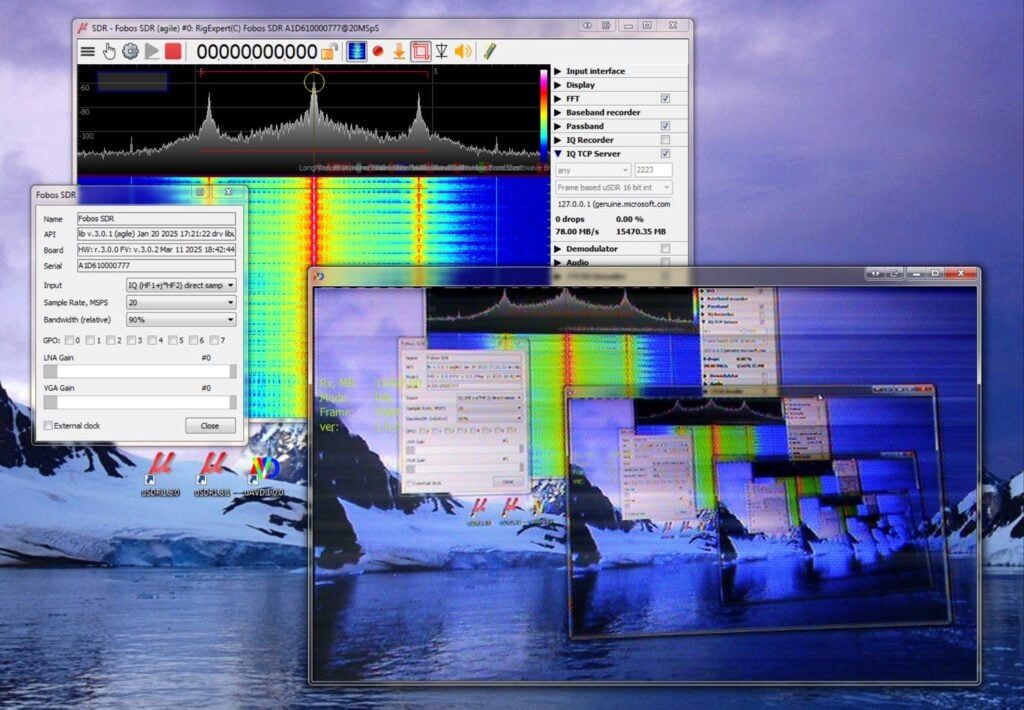
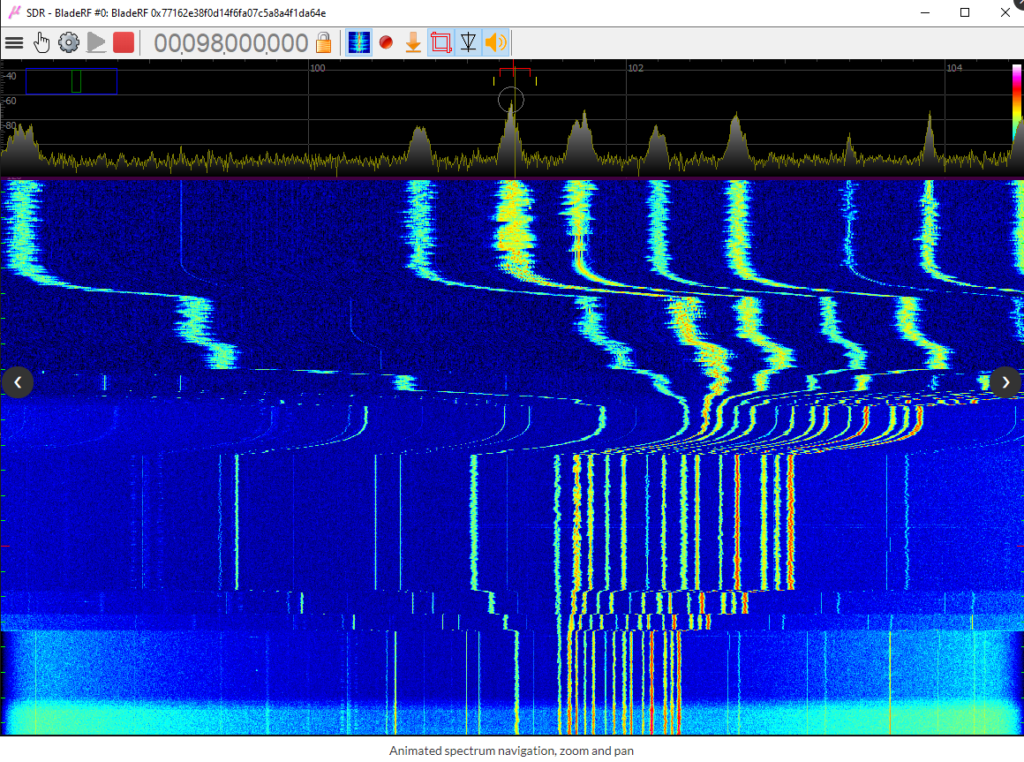
The program is called 'Iridium-Sniffer', and it is a standalone Iridium satellite burst detector and demodulator written in C. Typically, gr-iridium has been used for Iridium demodulation in the past, but it can be clunky and slow on lower-power embedded systems like the Raspberry Pi, as it requires the large GNU Radio dependency.
The program is compatible with iridium-toolkit, which performs the actual decoding and analysis of the Iridium packets demodulated by iridium-sniffer.
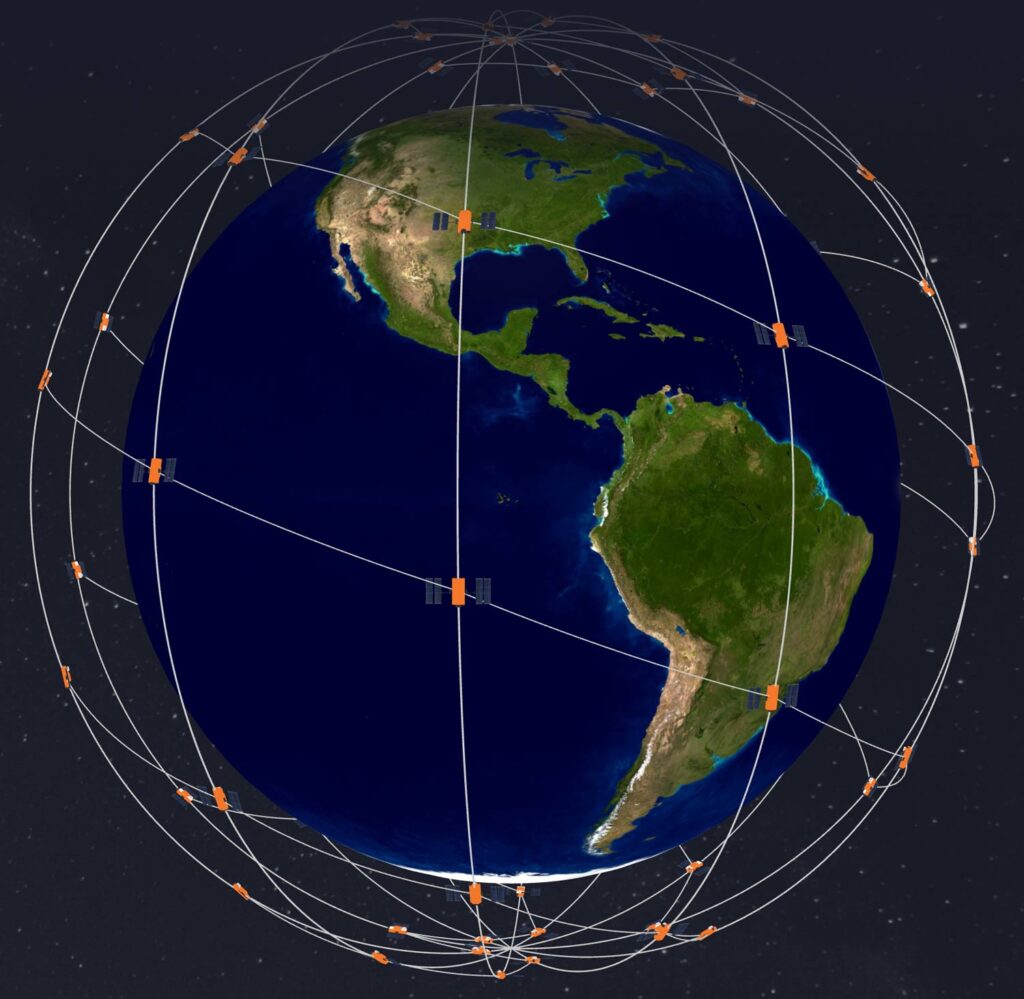
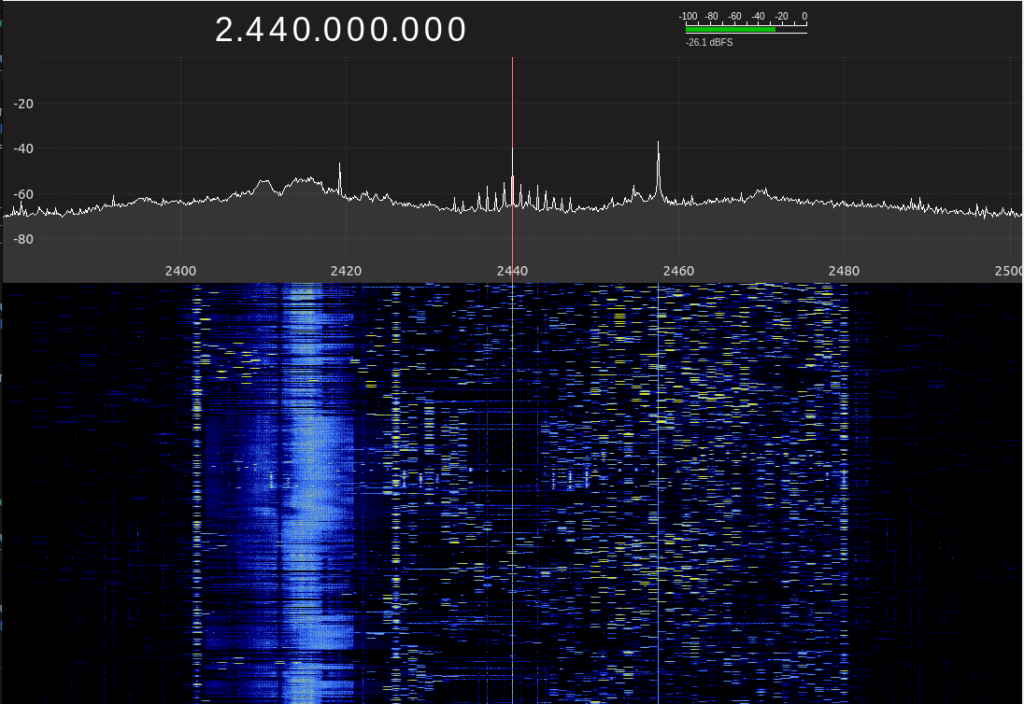
If you're not familiar with it, Iridium is a large global communications satellite constellation that provides services such as voice, messaging, and data. An antenna like our RTL-SDR Blog Active Patch antenna, combined with an SDR, can be used to receive these signals. Some data on Iridium is encrypted, but there is some unencrypted data that can be decoded when combining tools like iridium-sniffer and iridium-toolkit.
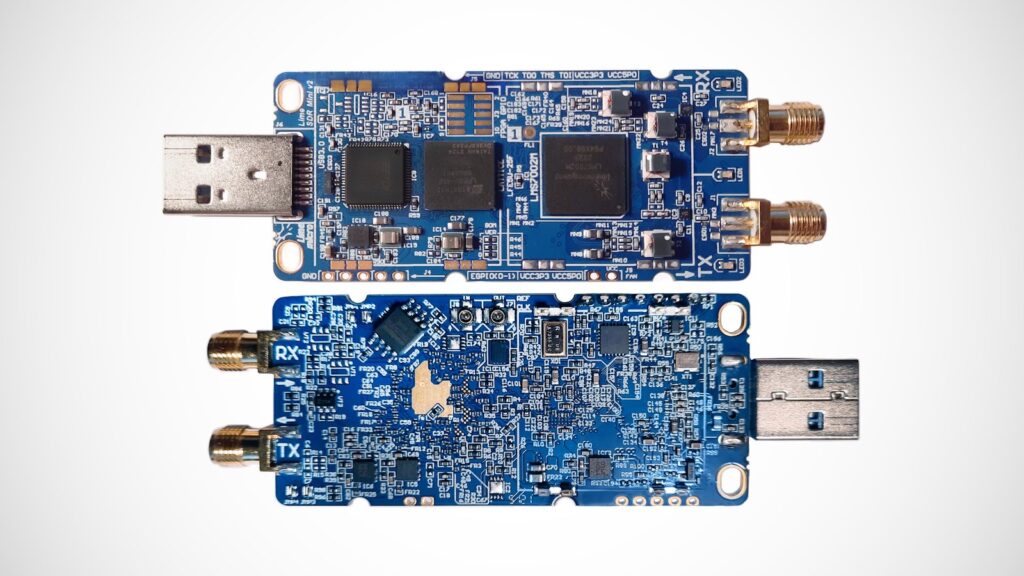
Iridium-sniffer is compatible with the HackRF, BladeRF, USRP (UHD), and SoapySDR (which includes RTL-SDR). Note that higher-bandwidth SDRs can receive much more of the ~30 MHz Iridium band, and therefore decode more data at once.