The KiwiSDR Backdoor Situation
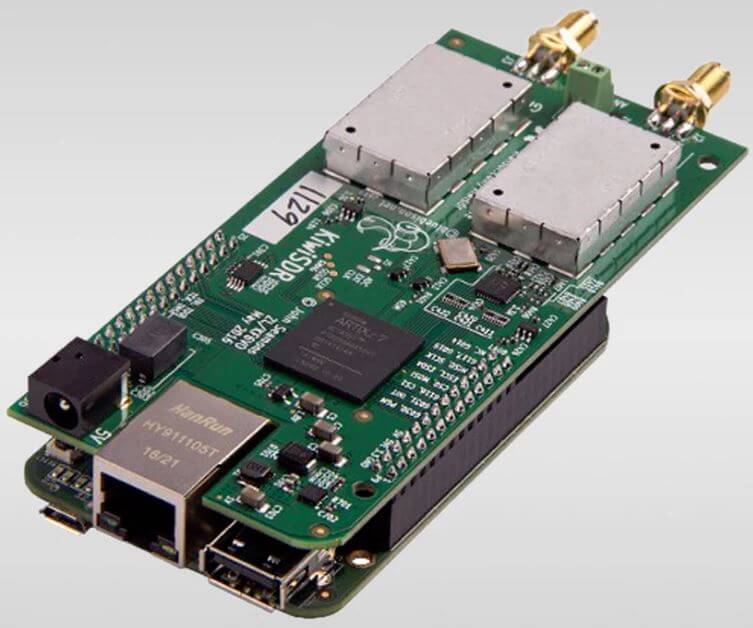
Since it's announcement in early 2016 we've posted many times about the KiwiSDR, a 14-bit wideband RX only HF software defined radio created by John Seamons (ZL/KF6VO). The KiwiSDR has up to 32 MHz of bandwidth, so it can receive the entire 10 kHz - 30 MHz VLF/LF/MW/HF spectrum all at once.
Compared to most other SDRs the KiwiSDR is a little different as it is designed to be used as a public web based SDR, meaning that KiwiSDR owners can optionally share their KiwiSDR online with anyone who wants to connect to it. The public functionality allows for some interesting distributed applications, such as TDoA direction finding, which allows users to pinpoint the location of unknown HF transmissions such as numbers stations.
In order to implement this online capability, the KiwiSDR runs custom open source software on a Beaglebone single board computer which connects to your home network. Recently there has been vocal concern about a security flaw in the software which could allow hackers to access the KiwiSDR. The flaw stems from the fact that the KiwiSDR has 'backdoor' remote admin access that allows the KiwiSDR creator to log in to the device and troubleshoot or make configuration changes if required. This backdoor has been public knowledge in the KiwiSDR forums since 2017, although not advertised and explicit consent to have it active and used was not required.
Interesting post on the KiwiSDR forums. Seems to imply the KiwiSDR author has remote access to all KiwiSDRs? Post has since been modified to remove the last paragraph and the thread locked :-/ https://t.co/cAi5dS7J49 pic.twitter.com/elqSsaUJ65
— Mark Jessop (@vk5qi) July 14, 2021
The intent of the backdoor is of course not malicious, instead rather intended as an easy way to help the creator help customers with configuration problems. However, as KiwiSDR owner Mark Jessop notes, the KiwiSDR operates in HTTP only, sending the admin master password in the clear. And as KiwiSDR owner and security researcher @xssfox demonstrates, the admin page gives full root console access to the Beaglebone. These flaws could allow a malicious party to take over the Beaglebone, install any software and perhaps work their way onto other networked devices. Another tweet from xssfox implies that the password hashes are crackable, allowing the main admin password to be easily revealed.
Quick video showing how the backdoor on the kiwisdr works.
— xssfox (@xssfox) July 15, 2021
I've also tested that touch /root/kiwi.config/opt.no_console mitigates the issue
Thanks @the6p4c for helping me test :) pic.twitter.com/0xKD1NfvwL
Creator John Seamons has already released a patch to disable the admin access, and as of the time of this article 540 out of 600 public KiwiSDRs have already been auto-updated. Owners of KiwiSDR clones should seek out updates from the cloner.
It is clear that the KiwiSDR is a passion project from John who has dedicated much of his time and energy to consistently improving the technical RF engineering side of the device and software. However we live in an age where malicious hacking of devices is becoming more common, so anyone releasing products and software that network with the internet should be reminded that they have a responsibility to also dedicate time to ensuring security.
John has reached out to us in advance and noted that he currently cannot yet comment publicly on this topic due to legal advice.
I’m frankly amazed at the comments that normalize this kind of backdoor. First of all, it doesn’t matter if it has been abused or not. If you buy a car from a retailer, and then later find out that for years, that retailer kept a copy of all keys of all cars sold “just in case” he needed to get into your car without you knowing about this, you’d be furious. And rightly so.
Furthermore, this is the second time this happened, with the author having been asked if there are any more backdoors, to which he did not respond – and now we know why. If he wanted a way to have people give him access to the system, why not ASK first? Why not make it obvious to the users that this backdoor existed, and make it a choice in the first place?
It does not matter if he had any ill intent or not. You don’t do that without asking the owner of the device. It is wrong. It is unethical. It is dangerous. He’s lucky nothing bad happened, nothing more. His resistance to face this reality is shocking, as are the comments normalizing this egregious behavior. HTTPS is “too hard”? Give me a break.
I had a kiwisdr on backorder back when this news broke, and I am glad I canceled it in time.
There’s an awful lot of “could” and “might” in this flame-fanning post. Having had a kiwi on the web for years, the reality is “didn’t”
Everyone downloaded it for free… patch it and get on with your lives. Far worse happening under your noses
Ain’t that the truth!
Like all of us, I sure do hope that this unique KiwiSDR project will continue. I agree with Martin that all this noise and negative publicity could have been avoided by contacting the developer first pointing out the security flaw.
I guess we will have to wait until the dust settles around this security issue and John has found updated legal advise to make a public statement about it.
In the meantime admins could check their log files. Another forum suggested to have a look at the results of the command zgrep — “PWD admin” /var/log/messages* for suspicious access to your kiwi server. You could use SSH, Putty or in case you are using the BBAI Cloud9 to navigate to the var directory. Doing so for my Kiwi with logs going back a couple of months I did not find any unusual activity.
“…all this noise and negative publicity could have been avoided by contacting the developer first pointing out the security flaw.”
This is really the tragedy of this situation. It’s a situation where the “cure” was worse than the malady. Of course then folks wouldn’t have gotten their names in writeups in ARS etc….
I sincerely hope the KiwiSDR project continues, while I don’t publicly share my KiwiSDR I do understand the security concerns. But I have to ask were there any breeches before the patch was released?
Like all of us, I sure do hope that this unique KiwiSDR project will continue. I agree with Martin that all this noise and negative publicity could have been avoided by contacting the developer first pointing out the security flaw.
I guess we will have to wait until the dust settles around this security issue and John has found updated legal advise to make a public statement about it.
In the meantime admins could check their log files. Another forum suggested to have a look at the results of the command zgrep — “PWD admin” /var/log/messages* for suspicious access to your kiwi server. You could use SSH, Putty or in case you are using the BBAI Cloud9 to navigate to the var directory. Doing so for my Kiwi with logs going back a couple of months I did not find any unusual activity.
I can’t really be angry about the backdoor, I understand the motivation behind it and I’m happy to forgive the lack of security awareness. I also appreciate the fast and comprehensive effort to spread the update which closes the backdoor.
However, what I don’t understand, is the complete – and unexplained! – removal of both the communication platform (forum.kiwisdr.com) and the normal website (kiwisdr.com) which are essential for kiwisdr users in the long run, considering there is no other kind of “manual”. I would have liked more transparency in that regard.
A link to the on-line manual is still provided on the KiWi home page.
http://kiwisdr.com/quickstart/
At best the KiWi forum will probably return when the current level of unwanted attention goes away, at worst the damage will have been done, it will not return and the KiWi project will end, probably due to legal issues that have been thrown up.
All for a few minutes of on-line ‘fame’, what a waste……………………..
A link to the on-line manual is still provided on the KiWi home page.
Not “still” – it’s new since today (as a response to my posting, I guess). Thanks BTW!
All for a few minutes of on-line ‘fame’, what a waste……………………..
Hm. I don’t see any misconduct due to need for recognition. Maybe I missed something, but as far as I can tell, someone had a problem with his kiwi, and John tried to help remotely, while his answer indirectly indicated something like the use of a backdoor. This led to surprise on the part of the questioner and a corresponding further inquiry, which I think is completely legitimate. This is how the matter got rolling (AFAIK). I don’t know what happened afterwards, but so far I can’t see any dubious motives.
Of course, the best practice to report a discovered security hole to the responsible author would be to do it “silenty” behind the scenes. But as far as I know, there was no such clear sequence of discovery and reaction here. The backdoor was in principle known before, but attracted new attention and perhaps new fears now – a dynamic of its own seems to have developed. That was certainly unfortunate, but I wouldn’t accuse anyone of having dishonest motives. Never should the bearer of bad news be held liable for its cause.
Please correct me if I shout have interpreted something wrong.
You can always travel back in time with the waybackmachine!
e.g. https://web.archive.org/web/20210623171935/http://kiwisdr.com/
Dealt with something similar in my past. His lawyers would have instructed him to take down any forums owned by his company and to cease all communications with the community until the legal situation is resolved.
What’s strange is that people spend time attacking the messenger, who is directly responsible for the security fix. I don’t particularly blame the developer for the original lapse of judgment, because it’s something that not everyone thinks a lot about, and in the original context it may have made more sense. But the right thing to do is acknowledge the problem and fix it, and thank the person that highlighted the problem.
The ‘Backdoor’ has been mentioned on the KiWi forum on several occasions over the past few years, so it’s not exactly the ‘major revelation’ that some folks are stating for purposes of self promotion.
These days I think you would have to be really naive to connect something to your network, without first considering the security implications.
It’s also strange that the folks who shout the loudest about various ‘security breaches’ are usually quite happy to embrace technologies that are extremely intrusive, be it smart phones, smart speakers, CCTV or participating in social media, basically anything that is web based is a potential security issue, and many people are happy to broadcast personal information to all and sundry without even being asked.
In this case it’s a pity that someone’s desire for 15 minutes of fame could derail the KiWi project, which is a wonderful free resource used by thousands of radio enthusiasts worldwide.
No, Martin. This is a big deal, and a massive breach of trust. There’s a reason the developer has sought legal advice.
A misjudgement on the part of the developer maybe, but as the ‘backdoor’ has been an open secret for at least the past four years, I don’t think it can be described as a ‘massive’ breach of trust. Especially as it would seem that it had not been implemented with malicious intent, or had previously been exploited by others.
However, I do question the intent of the people (messengers) who publicised their ‘discovery’, apparently without giving the developer an opportunity to resolve the issue before they brought it to the attention of the wider community.
I’m not in favour of security though obscurity, but public disclosure before a suitable fix could be implemented was actually when the main security issue arose, as it advertised a vulnerability, making it apparent to a much wider pool of wannabe script kiddies and other assorted malcontent’s, who would probably otherwise not been aware of the flaw.
The developer is not blameless, but I would also question the motive behind the disclosure, and the way in which it was made.
Similar to the above it is concerning how the item was raised. Essentially Mark Jessop went nuclear about something everyone already knew about. If I was the creator of KiwiSDR I would pull the plug and let the ungrateful amoung us have at it.
I don’t think “everybody already knew” that the backdoor was poorly secured and allowed root access to the kiwi-owners private network from anyone with little effort.
That is the problem, and not that the developer had access. Latter was indeed known.
Well said Martin. I agree entirely.
It used to be an SSH key and after complaints it was replaced by this kludge.
SSH with good key length would have ben quite secure and superior to the later unsalted SHA256 kludge.
This is something that you always need be aware of with any device made quickly with internet access. I doubt the creator had any ill-intent, just has a lot more knowledge about electronics and radio than he does computer security. This is also a major problem with a WIDE range of IOT devices with creators just adding wifi as a feature without properly understanding the security risks or how to mitigate them.
I hope this will not be the end of kiwisdr development from the original author. I really like the approach and own several of the devices (which have never been made publicly available for security concerns).
The same password on every single device sent as a unencrypted http* request, really easy to capture (*self censored*). And then that same password could, before it was removed 2 days ago, be used to login via a web API to approximately 600+ machines around the world with full root access.
I can picture how this got started innocently, and I can also see a serious lapse of judgement.
*Encrypted is not much of a higher security fence “if” you have full access to either endpoint (e.g. SSLKEYLOGFILE ) or if own a Certificate Authority. All CA’s can issue a 100% valid certificate for any domain, this is by design to allow “lawful interception”.
Encryption may not be needed, but a universal login should be certificate/key based cryptographic challenge.
That way, logged data from a login will NOT give access to other nodes, or even give any access to the current one at a later time.
Still, the not ideal to have a login like that e.t.c. apply!