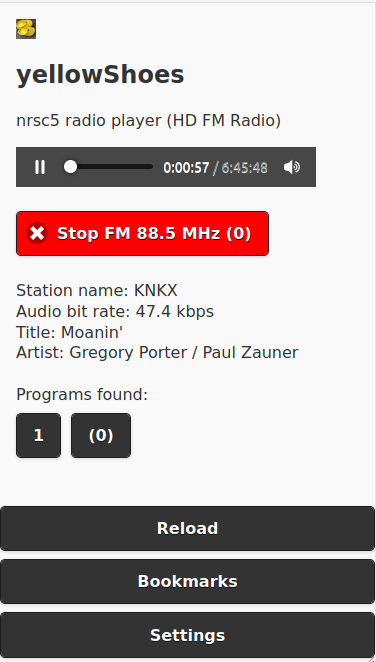
yellowShoes: A Browser Based HD Radio / NRSC-5 User Interface
Thank you to Evuraan for writing in and sharing his new browser based HD Radio / NRSC-5 interface for the nrsc5 decoder which he has called yellowShoes.
NOTE: We have been informed by some users that yellowShoes may contain a Trojan virus. This is likely to be a false positive which is a very common problem with antivirus software falsely detecting viruses on newly released niche software via heuristics. We have removed the above link out of an abundance of caution, however if you wish to continue the yellowShoes Github is here. If you want the software, but are concerned you can check the code compile it yourself.
NOTE UPDATE: The author of the software has contacted us regarding the virus concerns and written "I wanted to write in clarify that it is indeed a false positive, please see https://groups.google.com/g/golang-nuts/c/Au1FbtTZzbk and also https://golang.org/doc/faq#virus - this false positive occurs when you cross compile go binaries - This is a common occurrence, especially on Windows machines. Commercial virus scanning programs are often confused by the structure of Go binaries, which they don't see as often as those compiled from other languages."
HD Radio is a digital broadcast protocol replacement for analogue broadcast FM. It is only used in North America and is easily recognized as the two rectangular blocks on either side of a broadcast FM station signal on a spectrum analyzer/waterfall display. Together with an RTL-SDR and theori's command line nrsc5 decoder, the HD Radio signal can be decoded and listened to. Evuraan writes:
I wrote yellowShoes - an nrsc5 player which you can control from your browser. (Should work on Windows, Linux etc. Player F/E also works on Android Phones.)
Its sole dependency is that the nrsc5 binary must be available in the path.
A discussion thread on Reddit has also been created.
The HD Radio/NRSC-5 user interface is a revolutionary tool for radio enthusiasts, offering a convenient way to access high-quality radio features through a browser. The interface is intuitive, responsive, and offers an immersive experience for listening to high-quality radio broadcasts directly through the browser. It is praised for its user-friendly nature, offering an immersive experience for radio enthusiasts. This innovative innovation in radio technology brings advanced features to users with ease, enhancing their listening experience and bringing cutting-edge technology to the forefront. <a href=”https://srislaw.com/new-york-divorce-maintenance-calculator/“>New York Divorce Maintenance Calculator</a>
Hello,
Author of yellowShoes here; wanted to nip the FUD and wish to assert that there are no intentionally malicious shenanigans going on here.
This happens when you cross compile go programs, commercial AV programs are often confused by the structure of Go binaries, which they don’t see as often as those compiled from other languages. Please also see:
https://golang.org/doc/faq#virus
https://groups.google.com/g/golang-nuts/c/Au1FbtTZzbk
Also, (1) I’ve added https://github.com/evuraan/yellowShoes#optional-build so you can build this yourself. (2) Added a release https://github.com/evuraan/yellowShoes/releases/tag/1.08f-ui-1.3d
Thanks!
Trojan:Win32/Sabsik.FT.A!ml Detected which is NOT a false positive! This is a severe risk! Do not download!
I downloaded the git repository and uploaded it to virustotal (search for “91ca61ff922b36a97210d3aa6b3c8ba452e 553c53dbbbfff4d23c6efc9fc7a53”), one of the files (yellowShoes-main/bin/yellowShoes-win-386.exe) looks like it might be a false positive (mostly detected by heuristics or neural network pattern matching), or maybe it is a virus.
You could always download the go source code and “go build” it yourself. It is odd that they included all the compiled binary files mixed with the source code instead of the standard git-hub way by publishing a release.