Using a Software Defined Radio to Send Fake Presidential Alerts over LTE
Modern cell phones in the USA are all required to support the Wireless Emergency Alert (WEA) program, which allows citizens to receive urgent messages like AMBER (child abduction) alerts, severe weather warnings and Presidential Alerts.
In January 2018 an incoming missile alert was accidentally issued to residents in Hawaii, resulting in panic and disruption. More recently an unblockable Presidential Alert test message was sent to all US phones. These events have prompted researchers at the University of Colorado Boulder to investigate concerns over how this alert system could be hacked, potentially allowing bad actors to cause mass panic on demand (SciHub Paper).
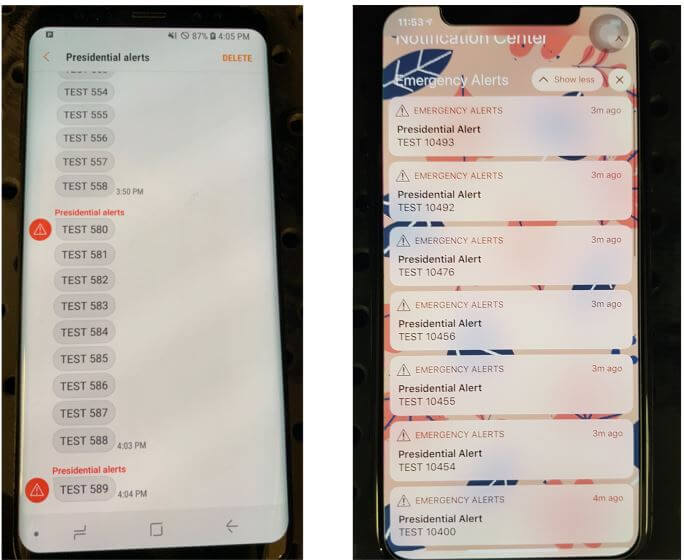
Their research showed that four low cost USRP or bladeRF TX capable software defined radios (SDR) with 1 watt output power each, combined with open source LTE base station software could be used to send a fake Presidential Alert to a stadium of 50,000 people (note that this was only simulated - real world tests were performed responsibly in a controlled environment). The attack works by creating a fake and malicious LTE cell tower on the SDR that nearby cell phones connect to. Once connected an alert can easily be crafted and sent to all connected phones. There is no way to verify that an alert is legitimate.
Responsible testing leads to slow adoption (fixes); irresponsible testing leads to mass-media dizsemination and ensuing fast adoption. Do the responsible thing – test irresponsibly.
wait you only need 1 transmitter and a cell tower in close promixity to you (so you don’t need that much power for TX) and then all cell towers wlil connect to your station? or will only the cell tower you target connect to you and only phones in its proximity will recieve your messages?
As a licensed op I see this as a biased hole in security. HOW remains the question. Thwse little arf rigs existed ling before this post. So how do you define it? Funnily enough most sdr setups cant xmit. So….. 1 watt over a few xmitters compared to a few kw from towers? Unlikely. Phones don’t single out, but if given only one option they’ll listen(faraday cage). I think the op should learn more about radiological before jumping. Phones work in the gigahertz range. They all go through stringent packet correction and validation. To set up a system like this is pointless. Realistically the time should be spent hacking a tower to infect. A few baby 1 watt xmitters isnt even gonna pass the authentication protocols on most modern phones. ? its just a transceiver. Not a god. Its only easy to scare idiots with media. Maybe try another venue. ? cuz you sure don’t know this one.
If you bothered to read the linked paper, the whole point is how you can bypass the “authentication protocols on most modern phones”.
Wow, straight up rejecting something, because you are “a licenced OP”. Come on, the poster did their research and done the tests, you did nothing. And your radio knowledge doesn’t bring anything to that. And besides, you’re just wrong. LTE doesn’t just work in the gigahertz range, it also works on a few hundred megahertz. The problem here are the station switching mechanisms. You don’t have to jam the signal, it’s more like WiFi deauth attacks.
This is why we can’t have nice things.
You should write test instead as fake. That might get the great thing that sdr-s are banned or carry restricted. Not sold to the public . Confiscated at the borders if ordered from China:(
Except the ones that you can order on Amazon