Exposing Hospital Pager Privacy Breaches
It has been a known open secret that for years many hospitals have been transmitting sensitive patient data over the air completely unencrypted via their pager network. With a simple ultra cheap radio such as an RTL-SDR, or any other cheap radio scanner such as a Baofeng, it is possible to eavesdrop on this sensitive data with very little technical knowledge required. Hospitals appear to be reluctant to upgrade their systems despite clearly being in violation of HIPAA privacy regulations in the USA.
Recently, @WatcherData has been trying to bring attention to this ongoing security breach in his home state of Kansas, and last month was able to get a news article about the problem published in the Kansas City Star newspaper. Over on Twitter he's also been actively documenting breaches that he's found by using an RTL-SDR to receive the pager messages.
Congrats to this new mom at @FreemanCares4U! Do you think she knows her personal info was sent out to people hundreds of miles away so that her hospital could use old pagers? #HIPAA #patients #breach #PII pic.twitter.com/YVyVWMvzFu
— Data Watcher (@WatcherData) May 28, 2018
Interestingly, publicity generated by @WatcherData's newspaper article has brought forward a hostile response from the hospital in question. Over on Reddit /r/legaladvice, a forum where anyone can ask legal advice questions, @watcherdata posted the following:
I discovered some time ago that hospitals throughout my region of the US are sending messages to physician pagers that include the name, age, sex, diagnosis, room number, and attending physician. These can be seen by anyone with a simple RTL SDR device, and a couple of free programs.
This seems like a massive HIPAA violation. So I contacted the main hospital sending out most of the information, and they were extremely grateful. I got a call within a day from a high level chairman, he explained their steps to remediate, that their auditors and penetration testers missed it, and that they would have it fixed within a week. Sure enough, they started using a patient number and no identifiable information in the pages. A couple of other hospitals have fixed their systems too, after I started contacting them via Twitter.
Early on in this process, I contacted my local newspaper. They reached out to the hospital in question, and were met with a "very hostile" response. They immediately deflected from any HIPAA violations and explained that I (the source) am in violation of the Electronic Communications Privacy Act of 1986.
This was enough to scare me off completely. I've nuked all log files from my systems and stopped collecting data. The reporters want to know how I would like to proceed. Originally, I was going to get full credit for the find in their article. But now, I at least need to be anonymous, and am thinking about asking them not to run the story at all.
Among the replies there doesn't seem to be consensus on whether simply receiving pager messages in the USA is legal or not.
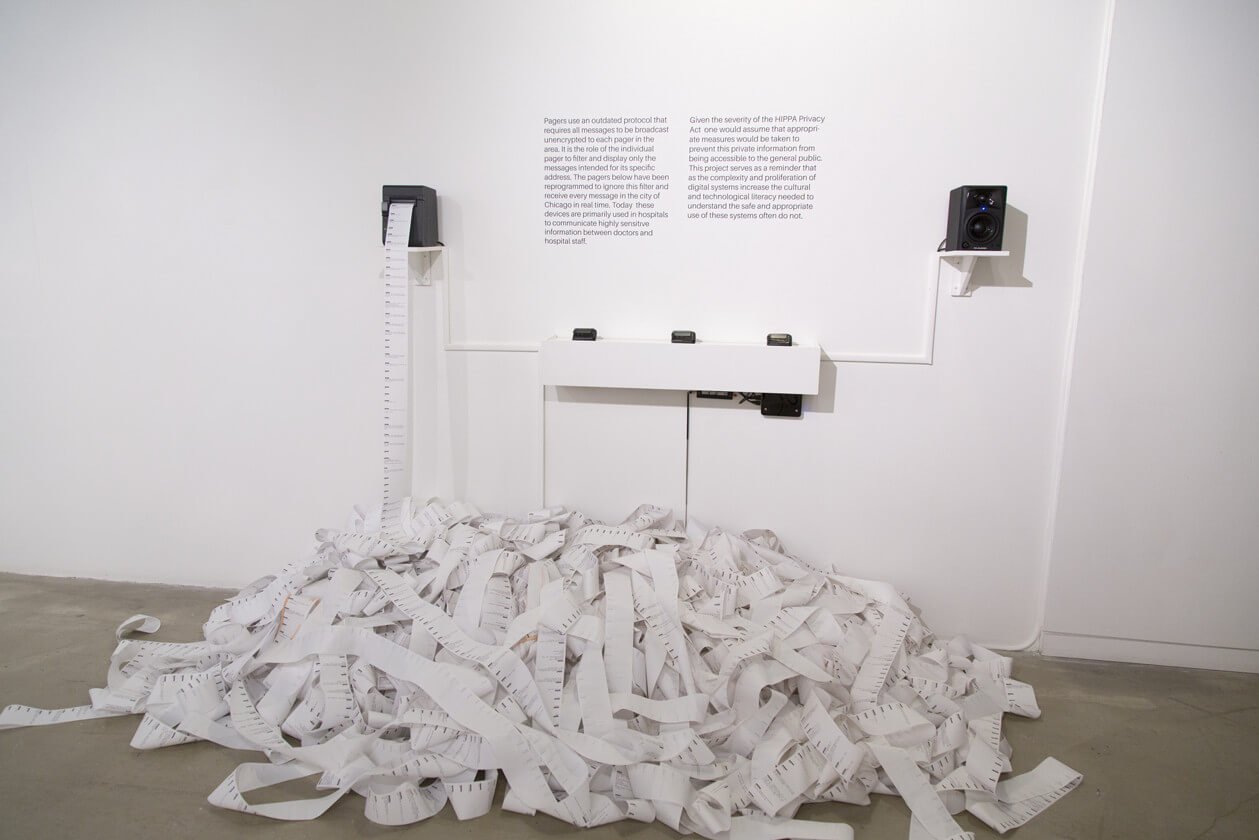
In the past we've seen similar attempts to bring attention to these privacy breaches, such as an art installation in New York called Holypager, which simply continuously printed out all pager messages that were received with a HackRF for gallery patrons to read.
imho, any what is not crypted can be received,.
if they dont want it, they need to switch to a new crypted system, hospital pagers are stone age systems.
My understanding of the laws in the U.S. is that this is a very fine line, to simply look at what is in plain sight (and for purposes of RF transmissions plain sight extends to decoding NOT decrypting) is legal. What is not legal if I am correct is recording or otherwise archiving pager transmissions, using information contained in unencrypted transmissions in any way and decrypting encrypted voice or data transmissions. While many different types of pager transmissions exist I assume we’re all talking specifically about POCSAG. Again the key difference here is encoding vs encrypting. Encoding a message in POCSAG for example merely facilitates transmission via RF and is in no way intended to act as a layer of security and does not qualify under any technical standard as encryption, whereas encryption is not a line code but a mathematical algorithm designed to secure data by changing the content of the data. There is also another method of security called Steganography, which is intended to hide the existence of a secret message inside an otherwise innocuous message, but that’s another topic. Bottom line, eavesdropping for profit and or compromising any overt mechanism of communications security is illegal. What the Hospital did by threatening that @WatcherData was in violation of the law is an underhanded tactic and blatant attempt to deflect from the legitimate issue he raised, but with some creative lawyering the hospital may have actually had a case arguing that because it is in the nature of computers to log and buffer and cache, etc… that might constitute recording or archiving regardless of the intent behind it. Moral of this story is that no good deed goes unpunished.
“They reached out to the hospital in question” Does he mean they contacted the hospital or was it an attempt to grab someone by the throat? What sort of BS language is this?
Put the following into a search engine of your choice:
“Reach out to” idiom
Idiom are part of the English language. Which is probably the most confusing part to non native speakers:
Far cry from
Hit the Hay
Cross that bridge when you come to it
Idioms, even.
Exactly what felony did he commit?
My expectation, without having read the full legalese text of the surveillance/privacy act of 1986 ( http://legislink.org/us/pl-99-508 ) would be that it should be covered by similar laws to recording telephone conversations/wiretaps ( https://en.wikipedia.org/wiki/Telephone_recording_laws#United_States ). Which depending on state, requires knowledge of the recording by one person actively involved in the conversation or all parties before it can be recorded legally, without a warrant.
So my guess would be felony wiretapping charges which could carry up to seven years in prison.
making a great case for “never telling anyone about your exploits, everrr”. some stuff ya just keep to yourself.
This is what happens when you give a computer script Kiddie access to radio equipment.
they like to run around making wild accusations that they somehow discovered something new thinking that they’re going to make a name for themselves as some leet hacker.
pager data has been like this since its Inception and it is like this on a nationwide scale, you didn’t discover anything you didn’t find anything new all you did was scream to your hometown and the rest of the world that you are committing a felony.
Talking to the hospital wasn’t a bad idea and it’s great that they actually made some changes.. however trying to boost up your ego and send this off to your local news was just plain stupid. of course they are going to contact the hospital and of course the hospital is going to be livid because now they are potentially looking at fines unfortunately for you you committed a bigger crime by even playing around with the stuff and posting it about the internet.
Agreed. 100%.
Next week’s topic will be about a Cap’n Crunch whistle, and blue boxes. Keep that dial tuned to 2600….
You did, you are and it’s 7-11 in a federal pokey and no we won’t be fedexing you any cut off saw blades in cakes. See you in (with time off for good behavior) oh, about 5 years.
Make sure you call me! I send you a battery flex and a motor saw.
….o ya, don’t wear earplugs to bed, you’ll want to hear the full breech as the SRU team blows your front door out of its frame at 0330 ~ and make sure you put your hands up really, really high.