Art Installation Eavesdrops on Hospital Pagers with a HackRF
For a long time now it has been known that pager data is sent in the clear and in plain text over a strong and easily received RF signal. The signal can easily be intercepted with a standard scanner radio or more recently with an SDR such as the RTL-SDR. Software such as PDW can then be used to decode the signal into plain text. We have a tutorial on this available here.
In these more modern days of cell phones and secure text messaging very few people still use pagers. But one heavy user of pagers is the medical community who still prefer them as they are already widely implemented in hospitals and are very reliable. The lower frequencies and high transmission powers used by pager systems allows for better reception especially in areas prone to poor cellphone reception such as in big buildings like hospitals with many walls underground areas. They are also very reliable as they receive messages instantly, whereas text messages can be delayed in times of high network traffic which is obviously a problem when a doctor is needed urgently. Finally, another advantage is that most pagers only receive, so there are no local transmissions that could interfere with sensitive medical machines. A major downside however is that pager use means that a lot of very private patient data can be easily intercepted by anyone anywhere in the same city as the hospital.
Back in October artist and programmer Brannon Dorsey displayed an art installation at the Radical Networks conference in Brooklyn which he calls Holypager. The idea is to bring attention to the breach of privacy. The installation simply prints out the pager messages as they are sent in real time, accumulating patient data that any visitor can pick up and read. He doesn't mention it on his page, but in one of the photos we see a HackRF One, antenna and Raspberry Pi hiding underneath the installation which is how the pager messages are received. A simple RTL-SDR could also be used as the receiver. Brannon writes:
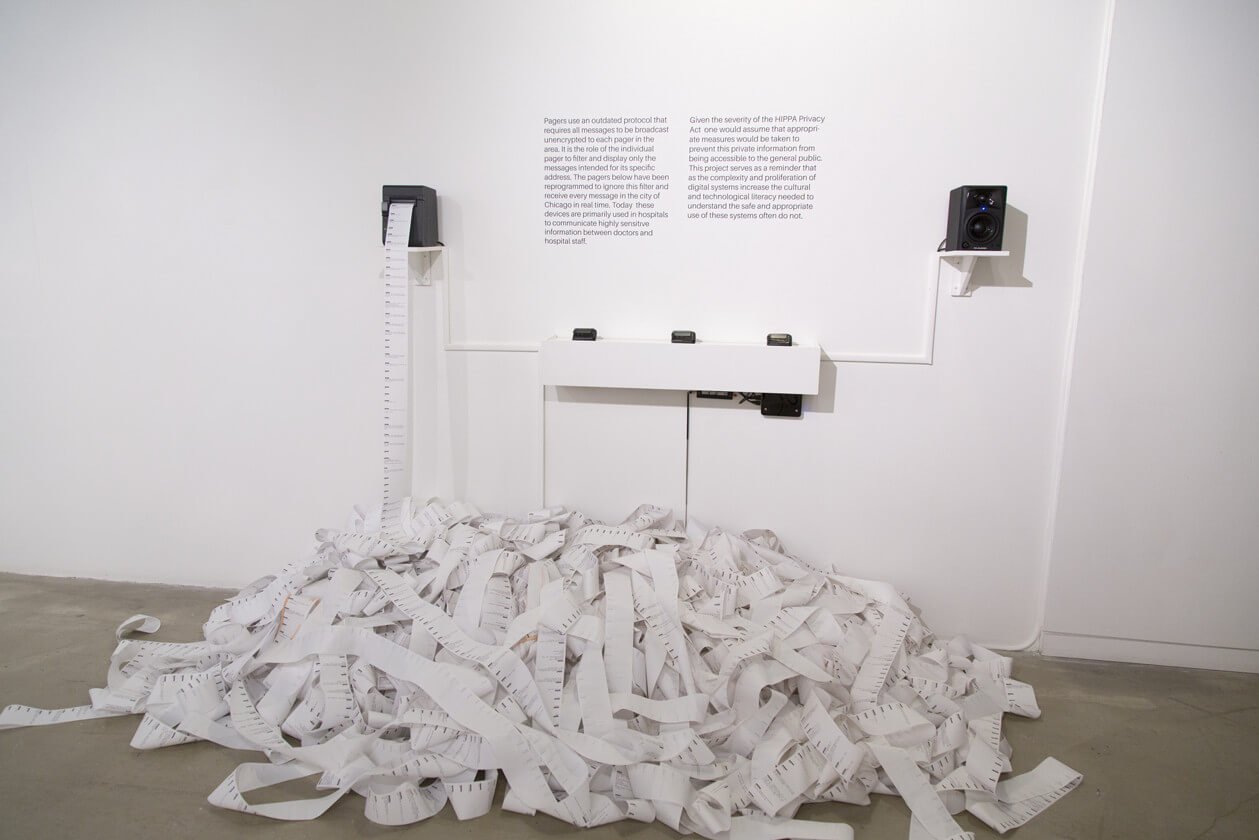
Holypager is an art installation that intercepts all POCSAG pager messages in the city it resides and forwards them to one (holy) pager. The installation anonymizes all messages and forwards them randomly to one of three pagers on display. Each message is also printed on a contiguous role of receipt paper amassing a large pile of captured pages for gallery goers to peruse.
Pagers use an outdated protocol that requires all messages to be broadcast unencrypted to each pager in the area. It is the role of the individual pager to filter and display only the messages intended for its specific address. The pagers below have been reprogrammed to ignore this filter and receive every message in the city in real time. Today, these devices are primarily used in hospitals to communicate highly sensitive information between doctors and hospital staff.
Given the severity of the HIPPA Privacy Act, one would assume that appropriate measures would be taken to prevent this information from being publicly accessible to the general public. This project serves as a reminder that as the complexity and proliferation of digital systems increase the cultural and technological literacy needed to understand the safe and appropriate use of these systems often do not.
I just stumbled on this. It’s 2023 and hospitals and other healthcare facilities are still sending POCSAG pages in the clear that include PHI.
I recently started dabbling with PDW myself and people saying in the comments ALL hospitals and patient data is encrypted now are WRONG. At least not my (lousy) local hospital… I saw names of people having babies, lab work orders and last names, last name of someone who needed a gyn exam, names and ages of people checked in, room numbers and names, even a home address… My jaw hit the floor….
In a reply to this article, Bendail Vam stated “I know in the US ALL hospitals are using encrypted pagers for they staff”. [Vam] can not know this without auditing all of the pager communications in all of the hospitals in the US. Conversely, I know for a fact that as recently as a few months ago, the air in Colorado was full of UNencrypted plain text hospital pager traffic that could easily be received and displayed miles from any hospital building. This traffic included full names, dates of birth and instructions that indicated medical conditions. For example, (using fictitious info here): “Patient Jones, Gladys DOB 6/17/1923 in room 204 needs transportation to dialysis”. I believe that this would constitute PII under HIPAA.
Feel free to post video of live capture? Like I say for 2 years now ALL hospitals typeII and above encrypt there HIPAA accountability pager/email and comms…this is a huge liabillity FACT in the USA. And I doubt that any staff would xfer DOB/NAME etc in pager comms as #1 its not needed, #2 if your recieving that type of message its not from/to a hospital but a transportation subcontractor, who woudld have there own HIPAA agreement with the patient/insurance company and #3 HIPAA is a dissemination declaration by the provider to the patient
and reading rlwsdr’s comment – he hits it pretty much on the nose. I was going to post similar with a congrats on the paper, and hey btw, welcome to cellblock 5a of pick your fav federal pokey…but hey he said it better.
I know what I saw, and I know what context it was in (internal transportation from one floor to another via gurney, not an outside contracted ambulance service. And this was lots of messages involving different facilities, not just a one off. But yes, it appeared to be going over commercial pager services, not a dedicated in house system.
Your last sentence is exactly why I will not be posting any screen shots or live captures. And the micro SD card the software was running on in a Raspberry Pi accidentally fell out of my pocket last time I was walking on a bridge across the Poudre river. Oops!
Anyone here that is in the US is free to read some tutorials, fire up an RTL, and see what is actually being sent as opposed to what someone says is or isn’t.
I second this. I’ve seen scores of medical paging information here in Colorado. A few months back, I tried to research the situation. From what I gathered, one or more of the hospitals in CO out-sourced their paging services to a 3rd party and promised HIPAA compliance. I concluded that the 3rd party provider does has means of providing HIPAA compliance to customers, but at least one hospital in CO isn’t properly implementing their services.
IMHO, the video is simplistic and makes incorrect statements/assumptions.
1) It’s HIPAA (Health Insurance Portability and Accountability Act) not HIPPA.
2) The POCSAG protocol is not the issue. It’s just a means of transmitting data. Kind of like oh, I don’t know, TCP/IP or UDP, the basis for the Internet.
3) HIPAA compliance means both encrypting PHI (Personal Health Information) sent in the clear and providing user authentication. So it’s really up to the sender not to put PHI in a page. Sort of like not sending your social security number in an email or entering it on an unencrypted webpage. BTW many hospitals have put into place policies which prevent the sending of PHI using pagers.
4) Pagers with encryption using the existing POCSAG protocol already exist.
5) There are applications which allow the sending of encrypted message to email addresses which, if setup correctly, will forward as a page.
6) By *publishing* the contents of transmissions he was not authorized to receive for others to see, Holypager’s “art project” is in violation of the Communications Act of 1934 (see 47 U.S. Code § 605 – Unauthorized publication or use of communications). To Holypager, feel free to be a test case and challenge this section of federal code on First Amendment grounds. Then plan to spend months if not years and hundreds of thousands of dollars on lawyers fees.
if hospitals are indeed following HIPAA wrt PHI in pager messages, then there is no problem here. right?
prosecution would only be 100% proof that the hospital is in massive violation.
hmm I wonder what Hospital this was done at? I know in the US ALL hospitals are using encrypted pagers for they staff, we have done many install and applied to many, many RFQ’s and the number one requirement is encryption, seconded only by coverage area served. All our systems use triple redundancy whreby the page is and sent to phones and also email account. I could imagine these messages on the floor are just general messages with no actual HIPPa information contained, as many staff levels recieve different status messages. Interesting.
probably seattle. i know for a fact a large hospital here transmits PHI in POCSAG all the time. possibly all of them do.
We actually sell and service private in house POSAG paging systems to protect Canadian Hospitals from a breach of sensitive patient information.
However unlike the USA Canada does not yet have a mandatory HIPPA law but be assured sooner or later sensitive information will be harvested from unprotected WAN (unprotected wide area networks)
We are providing many Canadian hospitals with personal pocket pagers from our in house paging devices.
Keeping our RF signal originating and remaining inside the hospitals we serve ensures a more private network for all.
Submitted by Tom of Quest Systems contact [email protected]