DragonOS: Installing Crocodile Hunter For Detecting Fake 4G Cell Sites
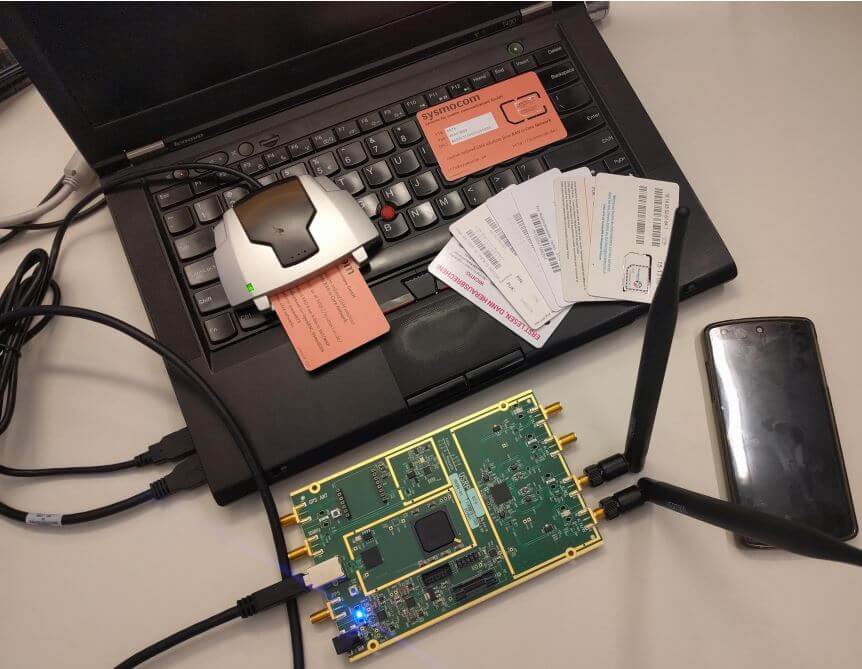
A few days ago we posted about two SDR related DEFCON talks which were recently released. One of the talks was about detecting fake 4G base stations with a bladeRF SDR and a tool they created called "Crocodile Hunter". It is currently compatible with the bladeRF x40 and USRP B200. The talk summary is posted below as it nicely summarizes what fake 4G base stations are and what Crocodile Hunter can do.
4G based IMSI catchers such as the Hailstorm are becoming more popular with governments and law enforcement around the world, as well as spies, and even criminals. Until now IMSI catcher detection has focused on 2G IMSI catchers such as the Stingray which are quickly falling out of favor.
In this talk we will tell you how 4G IMSI Catchers might work to the best of our knowledge, and what they can and can't do. We demonstrate a brand new software project to detect fake 4G base stations, with open source software and relatively cheap hardware. And finally we will present a comprehensive plan to dramatically limit the capabilities of IMSI catchers (with the long term goal of making them useless once and for all).
The Crocodile Hunter software is apparently a little difficult to install and get running, so Aaron who runs DragonOS YouTube tutorial channel has uploaded a video documenting how to install and configure the software. The tutorial assumes that you are the running the latest DragonOS image which already includes a lot of the prerequisite software, and in his example he uses a USRP B205mini-i SDR.