Hacking Alarm Systems with an RTL-SDR and RFcat
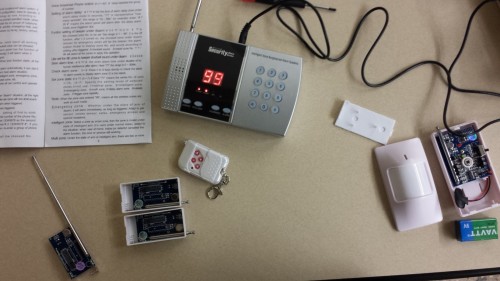
Back in 2014 the author of boredhackerblog.blogspot.com did a final year project for his wireless security class on hacking home alarm systems. His presentation was titled “How we broke into your house”. In his research the author used both an RTL-SDR and a simple RFcat wireless transmitter and performs a simple replay attack on a cheap $50 alarm system. His process for reverse engineering the alarm was essentially:
- Look up the device frequency and listen to it with an RTL-SDR and SDR#.
- Record the signal and visually study the waveform in Audacity.
- Look up system part info and determine encoding type (e.g. ASK/OOK)
- Determine the bit string and baud rate.
- Program the RFcat to send the same disarm binary string.
Once again research like this shows that cheap home alarm systems have literally zero protections against wireless attacks. In a previous post we also showed how the popular Simplisafe wireless alarm system could be disarmed in a somewhat similar way.