Using RTL_433 to Decode SimpliSafe Home Security Systems
SimpliSafe is an American DIY home security system company that claims over 2 million customers. Their system relies on 433/315 MHz ISM band wireless radio communications between its various sensors, control panels and remote controls. Back in 2016 we already posted about research from Dr. Andrew Zonenberg and Micheal Ossmann who showed that the SimpliSafe wireless communications are unencrypted, and can easily be intercepted, decoded, and spoofed. SimpliSafe responded to those concerns by downplaying them and mentioning that sophisticated hardware was required.
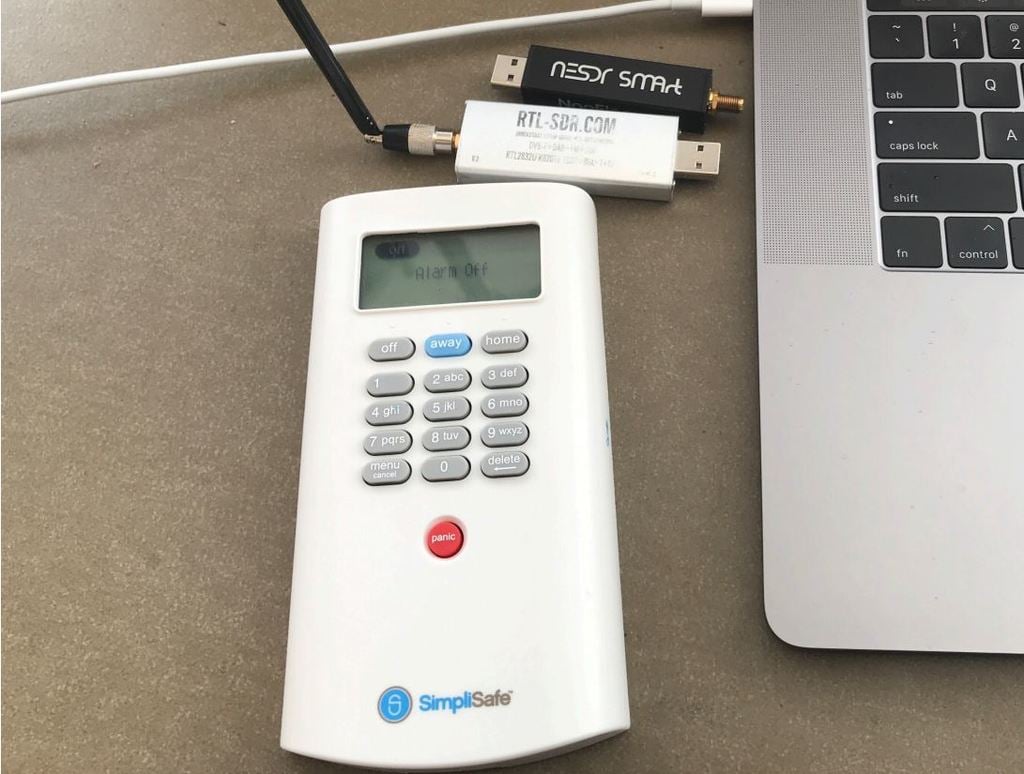
However, now Adam of simpleorsecure.net has recently disclosed a security advisory and a blog post discussing how easy it is to decode SimpliSafe wireless communications with an RTL-SDR and the rtl_433 software. He also also released slides from a recent talk that he did that go over his entire process and findings.
Adam began with some initial manual RF analysis with an RTL-SDR, and then later worked with rtl_433 dev Christian Zuckschwerd to add PiWM demodulation capability, which is the modulation used by SimpliSafe systems. Now Adam is able to easily decode the serial number, pin codes, and status codes transmitted by SimpliSafe sensors and key pads in real time with just an RTL-SDR.
This is very concerning as not only could a burglar easily learn the alarm disarm pincode, but they could also profile your behavior to find an optimal time to break in. For example if you arm your alarm before bed, and disarm in the morning your sleep schedule is being broadcast. It is also possible to determine if a particular door or window has been left open. With a tuned Yagi antenna Adam was able to receive signals from 200+ feet (60m) in free space, and 115 feet (35m) through walls.
In addition to the lack of encryption, Adam also discovered that the SimpliSafe system was susceptible to jamming attacks, and that the tamper detection system can be easily compromised. Adam has disclosed all concerns and findings to SimpliSafe who are aware of the problems. They assure him that next generation systems will not suffer from these flaws. But unfortunately for current generation owners, the hardware will need to be eventually replaced as there is no over the air update capability.
You can easily record and play back unencrypted 433MHz control signals easily. To receive, use a generic receiver module connected to your sound input (an attenuator may be required). To play back, feed audio output to a ‘data slicer’ (a simple op-amp circuit) and then into the input of a generic transmitter module. You can use the Audacity sound editing software for that. With a little effort you can decode by hand from the waveform or export the audio as mono raw data for use in a program you need to write yourself. I was doing this 30+ years ago with an 8 bit home computer with a modified door bell as receiver and a modified key fob to transmit,..
Also a cheap option to broadcast at 433 MHz became available recently.
I bought one of these 6$ FL2000 based VGA dongles, compiled fl2k_file (from osmo-fl2k library) to a windows executable and was able to generate a signal accepted by a 433 MHz system.
You just have to play around a bit to create a file with a suitable signal representation (combination of fl2k sample rate and frequency of carrier wave) to hit the target frequency. But that was quite easy in the end…