Australian Teenager Exposes COVID-19 Patient Data via POCSAG Pager Network
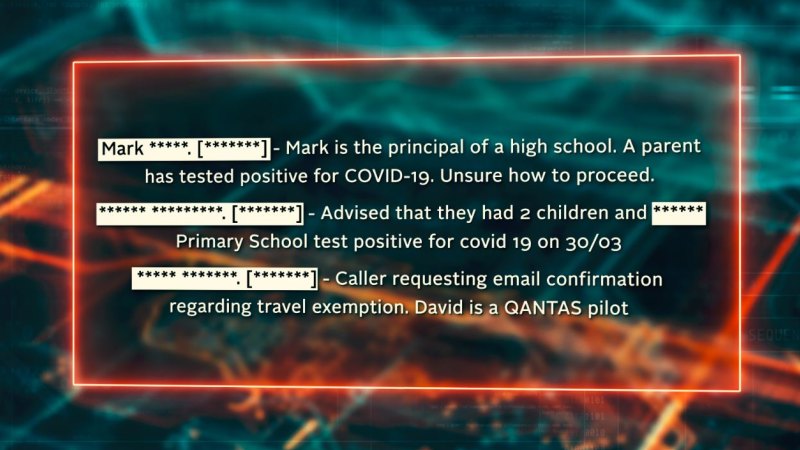
A 15 year old Australian teenager has been accused of leaking sensitive COVID-19 patient data such as the phone numbers and addresses of people in quarantine, and conversations between health officials and doctors about COVID-19 patients. The leak occurred via a public web page that he had set up to share decoded POCSAG pager data that he received from his home.
Pagers are still typically used in many parts of the world by hospitals. It is a tried, tested and very reliable system for messaging, however most systems in the world send data out in unencrypted plain text for all to see. Anyone with a cheap scanner radio or $20 SDR and freely available software can decode every single message sent via paging from almost anywhere in a city as the signals are often extremely strong. Pagers are intended to be reserved for urgent infallible messaging, as paging is more reliable compared to mobile SMS since SMS messages do not always get through, or can be delayed by several minutes. Alternative secure communication channels such as SMS should be used for private information, however this protocol is not always followed due to the additional hassle.
The teen appears to have used either a Baofeng or RTL-SDR to receive the POCSAG pager signal available in his hometown in Western Australia. The pager signal was decoded with multimon-ng, and displayed via the PagerMon software. PagerMon creates a web page that displays pager messages in an easily readable format, and the page can be made accessible to the internet if desired. It seems that the teen is a scanner enthusiast, and did not intend to purposely leak patient data, however others found his PagerMon page and brought it to the attention of the media. His site has now been shut down, and officials have decided to shut down the pager system in favour of a double SMS system.
This is a story that repeats often all around the world. In the past we've seen whistleblowers report on patient data breaches in Vancouver, Kansas, and via an art installation in New York that continuously printed out pager messages.
You don’t need to be a rocket scientist to work out that information of this network is sensitive and private. This system is in use as it is a tried and tested method of communication. Most emergency departments can rely on it as it has not changed. In simple terms 1 message can reach thousands of users in a group without delay. learn how to see it on a spectrum waterfall and know that one day this info could save your life.
The security community has discussed this topic to death. The only “idiot” is the person who created a procedure that transmits sensitive information over an insecure channel.
The owner of the system, and more specifically, the person responsible for the data, needs to ensure that sensitive data in their care is properly handled.
When data can be protected by technical means, the data custodian is responsible for doing so. If the data cannot be protected, it is the custodian’s responsibility to not send it over insecure media.
Hoping people won’t read unprotected data is not a valid security strategy.
I’ve looked at pager messages before in Australia and it was a bit disturbing. It was 95% of hospital patient details (anonymous’ish, no names but all sorts of details) and emergency medical services (with addresses and COVID details). I was shocked that they were still using unencrypted pager messages for hospitals.
I’m not sure of legalities, I know the UK has some weird “it’s illegal to listen to some unencrypted messages” but I don’t think it’s the same here.
Scanner enthusiast? More like complete idiot. I’ve monitored pagers in the past and some messages can be so heart breaking when you see what others are going through. I would never divulge any content, besides, it has always been illegal to do so. This kid knew what he was doing and his age is no defence…