Performing a Replay Attack on a Wireless Doorbell with a USRP SDR
A replay attack consists of recording a signal, and then simply replaying it back at the same frequency at a later time. To do this a receive and transmit capable software defined radio like a USRP/HackRF/bladeRF can be used.
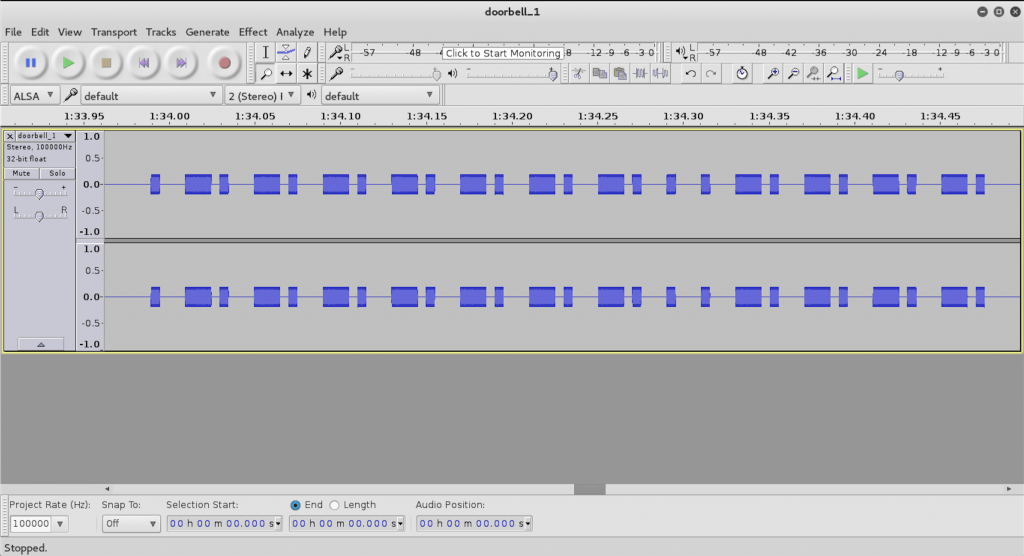
Over on his blog, the admin of the dxwxr group has posted a tutorial showing how he performs a replay attack on a simple wireless doorbell using a USRP, GNURadio and the audio editor Audacity. This is a very simple process and is a great tutorial for those looking to get started in reverse engineering signals. First he determines the frequency of the doorbell which turned out be be around 315 MHz. Then using GNURadio he records the signal emitted by the doorbell remote and opens up the audio file in Audacity. He then isolates a section of the signal and saves it as a raw aiff file. Finally, he uses GNURadio to transmit the isolated signal via the USRP.
Replay attacks on wireless devices such as a doorbell, https://www.youtube.com/watch?v=AcH6VGdqCio
Can i just record audio and retransmit using a ultrachep transmitter like this http://www.ebay.com/itm/272317008510 with a usb TTL interface?
This simple replay attack is what is shown on https://www.youtube.com/watch?v=UwgJiUhloho :Record I/Q with RTL_SDR dongle and replay with Raspberry (rpitx). USRP and GnuRadio is a bit overkill for that attack but the article is fun for learning.