Performing a Side Channel TEMPEST Attack on a PC
TEMPEST refers to a technique that is used to eavesdrop on electronic equipment via their unintentional radio emissions (as well as via sounds and vibrations). All electronics emit some sort of unintentional RF signals, and by capturing and processing those signals some data can be recovered. For example the unintentional signals from a computer screen could be captured, and converted back into a live image of what the screen is displaying. We have tutorials on how to do this with a program called TempestSDR available on a previous post of ours.
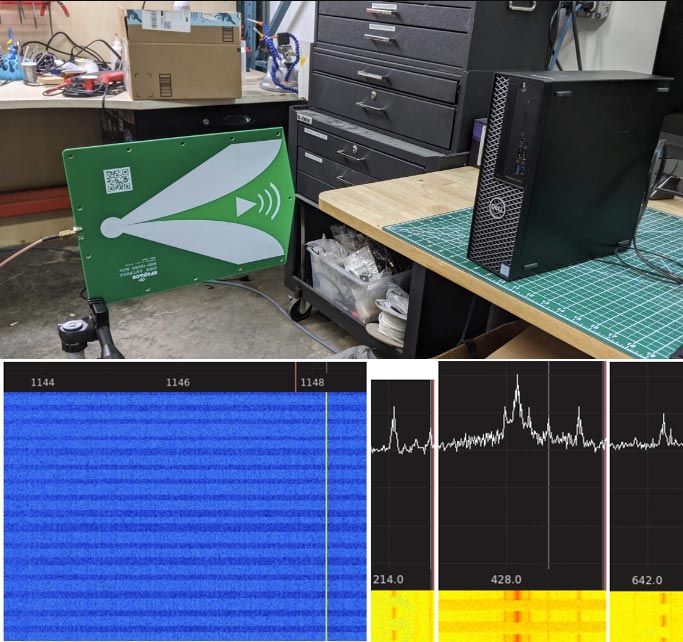
Recently Mikhail Davidov and Baron Oldenburg from duo.com have uploaded a write up about their TEMPEST experiments. The write up introduces the science behind TEMPEST eavesdropping first, then moves on to topics like software defined radios and antennas.
At the end of their post they perform some experiments like constantly writing data to memory on a PC, and putting the PCs GPU under varying load states. These experiments result in clear RFI bursts and pulsing carriers being visible in the spectrum, indicating that the PC is indeed unintentionally transmitting RF. They note that machine learning could be used to gather some information from these signals.
Their write up reminds us of previous TEMPEST related posts that we've uploaded in the past. One example is where an RTL-SDR was used to successfully attack AES encryption wirelessly via the unintentional RF emitted by an FPGA performing an encryption algorithm. Another interesting post was where we saw how a HackRF was used to obtain the PIN of a cyprocurrency hardware wallet via TEMPEST. Search TEMPEST on our blog for more posts like that.