RSGB Talk: How To Check and Report VDSL RFI with an SDR in the UK
Back in April we posted a video from Tech Minds where he showed us how to use special software combined with an SDRplay RSPdx to detect and report VDSL interference on the HF bands. VDSL or Very High Speed Digital Subscriber Line is an internet connection technology that runs over old copper phone wires allowing for a fast broadband connection. The frequencies used by VDSL are between 25 kHz to 12 MHz, and for VDSL2 up to 30 MHz. Unfortunately the frequencies used can result in high amounts of radio interference from RFI radiating from the copper phone lines which is a major problem for HF amateurs and short wave listeners.
Recently John Rogers (M0JAV) presented a talk via the UK amateur radio organization RSGB. In the talk he explains how VDSL works, why it causes RFI and how to check for VDSL RFI using an SDR and the Lelantos software. He also shows how he drove around with a magnetic loop antenna looking for VDSL RFI sources in his neighbourhood. He then goes on to call out for more volunteers in the UK to submit RFI reports to Ofcom as they responded that they won't do anything about the interference unless there are more complaints.
The RSGB EMC Committee (EMCC) has been investigating VDSL interference since 2014. As the number of installations has risen to over 30M the interference level at amateur radio stations has also increased. The majority of radio amateurs are now impacted by this problem.
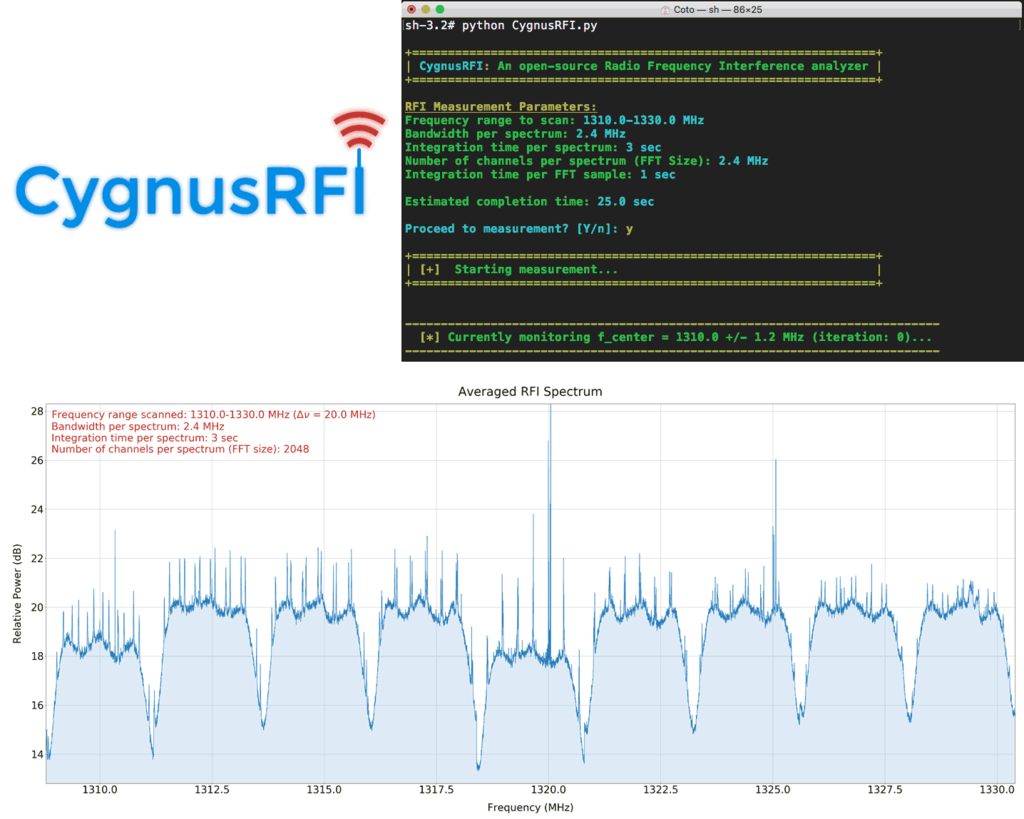
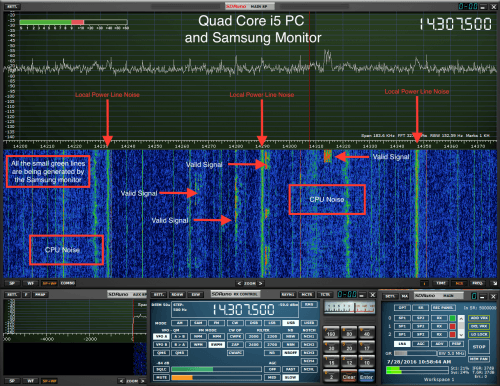
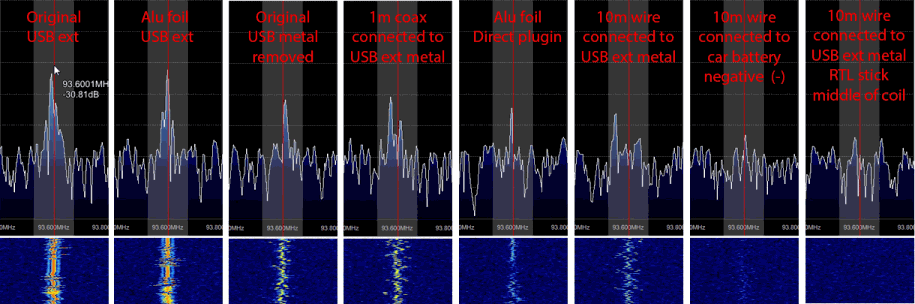
In the May 2020 RadCom we outlined how to detect and estimate the level of interference. This can be done by inspection of an SDR spectrum display or by taking a recording and then using a SW package—developed by Martin Sach of the EMCC—which identifies the VDSL signature in the recording and shows how many different VDSL lines are causing the problem and what their relative strengths are.
This talk demonstrates what to look for and how to use the tools to find out if you have a problem yourselves. We hope this will help you respond to our call for action and complain to Ofcom about the level of RFI you are subjected to.
John Rogers, M0JAV
Chair EMCC