Leif Compares various SDRs including the RSP1, Airspy with SpyVerter, Airspy HF+, FDM-S1, IC706, Perseus
Over on YouTube Leif 'sm5bsz' has uploaded a video that does a lab comparison of various SDRs on the market now including the new Airspy HF+. Leif is known for providing excellent lab based technical reviews of various SDR products on his YouTube channel.
The first video compares the Airspy HF+ with the Perseus SDR. The Airspy HF+ is a new high performance yet low cost ($199 USD) HF/VHF specialty SDR. The Perseus is an older high performance direct sampling HF only SDR, although it comes at the high price of about $1000 USD.
In his tests Leif tests both units at 14 MHz and finds that the HF+ has about 15 dB better sensitivity compared to the Perseus (NF = 7dB vs 22dB). On the other hand the Perseus has about 23 dB better dynamic range compared to the HF+ (Dynamic Range = 127 dBc/Hz vs 150 dBc/Hz), although he notes that a blocking transmitter needs to have a very clean signal to be able to notice this difference which would be unlikely from Amateur transmitters.
In the next two videos Leif compares multiple SDRs including the SDRplay RSP1, FUNcube Pro+, Airspy with Spyverter, Airspy HF+, Afedri SDR-Net, ELAD FDM-S1, ICOM IC-706MKIIG and Microtelecom Perseus at 7 MHz.
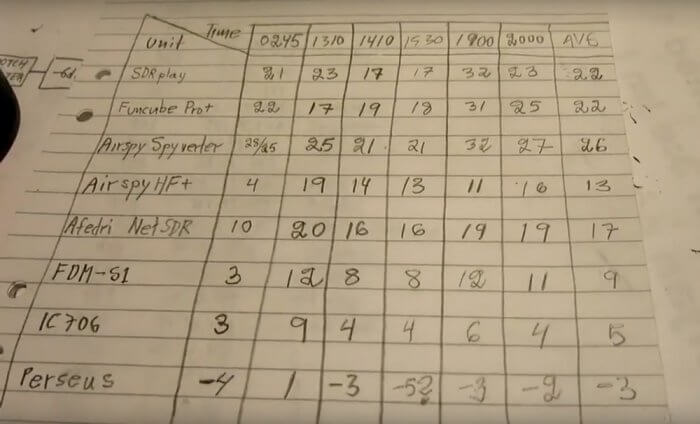
In the RX4 video Leif compares each SDR on dynamic range at 7 MHz. If you want to skip the testing parts, then the discussion of the results in the RX4 tests start at 1:03:00. A screenshot of the results is also shown below. The SDRs are ranked based on their average results over multiple measurements at different times which is shown in the last column. A lower value is better, and the value represents how much attenuation needed to be added to prevent the SDR from overloading and causing interference in his setup.
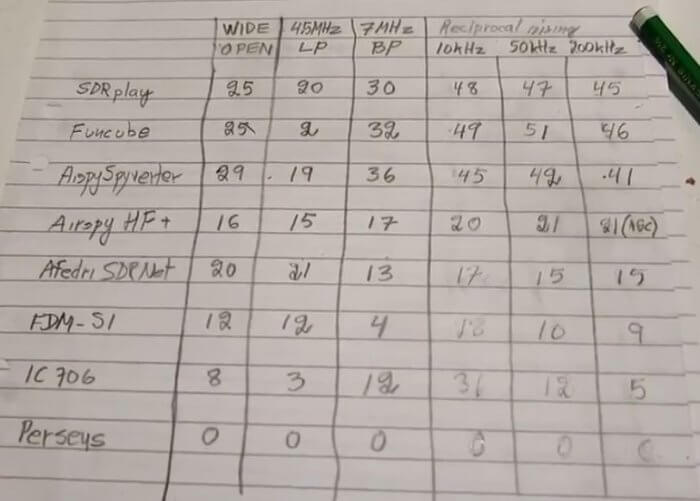
In the RX5 video the results start at 54:20:00. In this video he compares the SDRs with real signals coming in from his antenna at 7 MHz. He tests with the antenna signal wide open, with a 4.5 MHz LPF (to test out of band blocking performance), and with a bandpass filter at 7 MHz. Again lower values are better and the values indicate the amount of attenuation required to prevent overload. The Perseus is used as the reference benchmark. He also tests reciprocal mixing later in the video.