Using a HackRF and JavaScript Browser App to Perform Rolljam Replay Attacks on a Car
Over on her website, Charlie Gerard has uploaded a page showing how she was able to perform a replay attack on a car's wireless entry system using a HackRF and a JavaScript browser app she wrote.
Previously, Charlie had already written a JavaScript browser app for ADS-B tracking with an RTL-SDR. To achieve this she used the WebUSB API, which allows USB devices to connect to JavaScript apps in a web browser.
Having recently purchased a HackRF she wanted to see if something similar was possible with the HackRF. In her post, Charlie shows and explains the JavaScript code required to connect to the HackRF from a Chrome browser, and how settings like gain, frequency and sample rate can be adjusted. She then shows how to use the Canvas API to visualize the received data. Finally, she shows how to use the File System Web API to record data, and ultimately retransmit the recorded data with the HackRF.
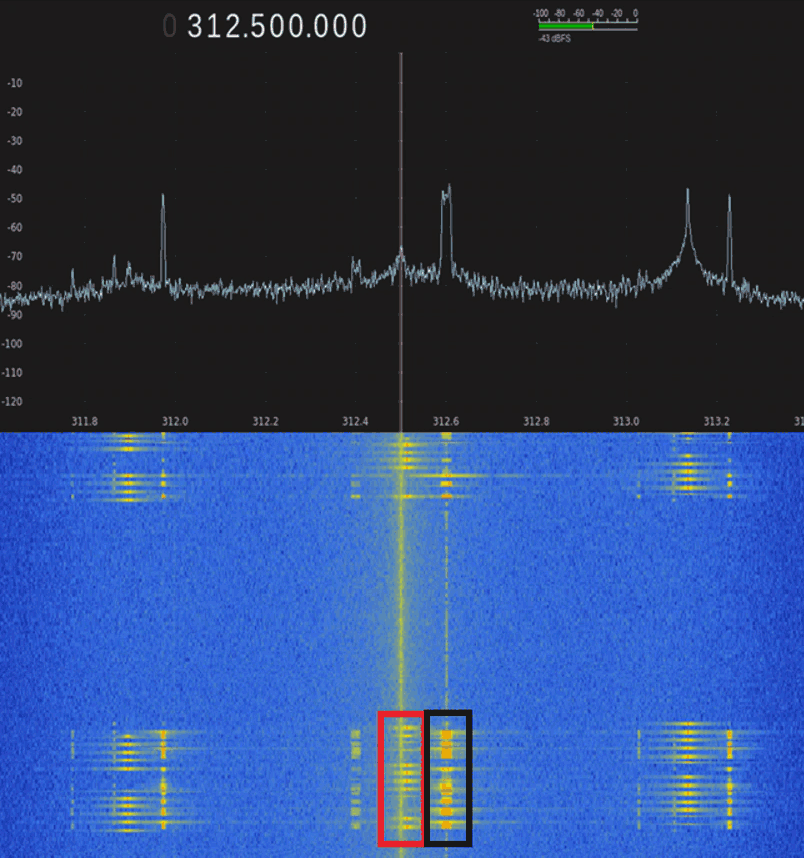
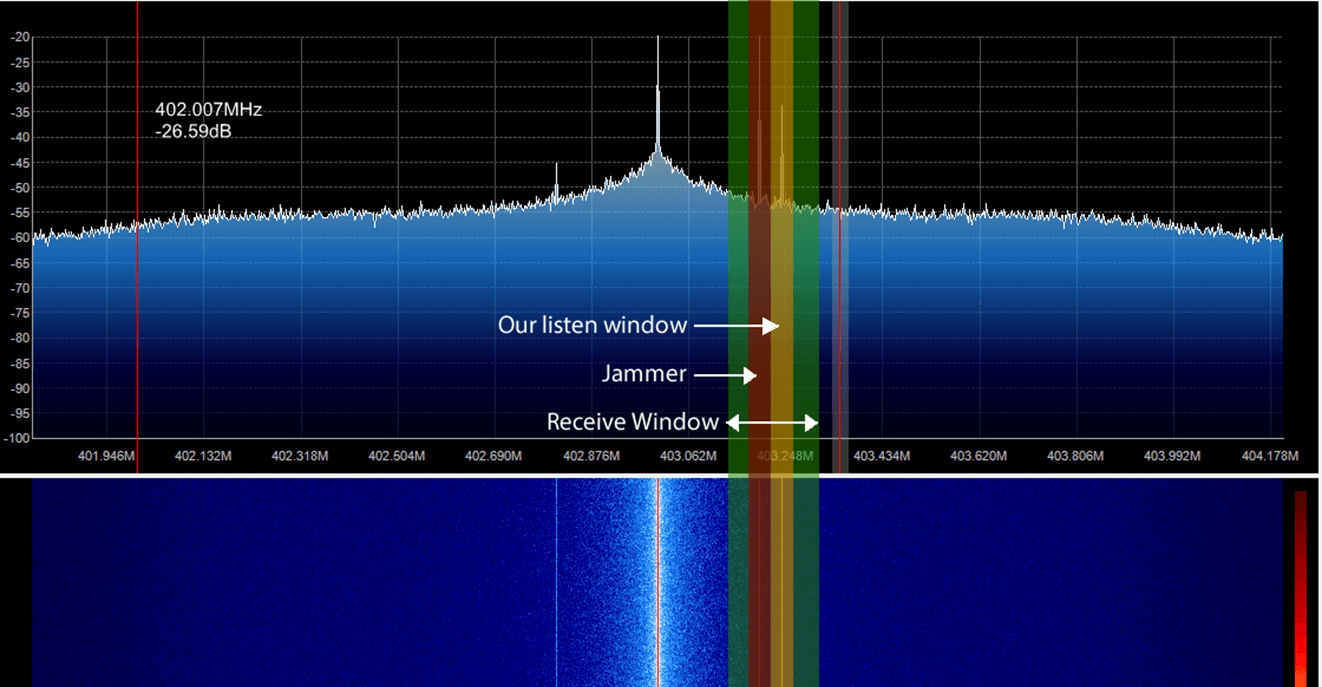
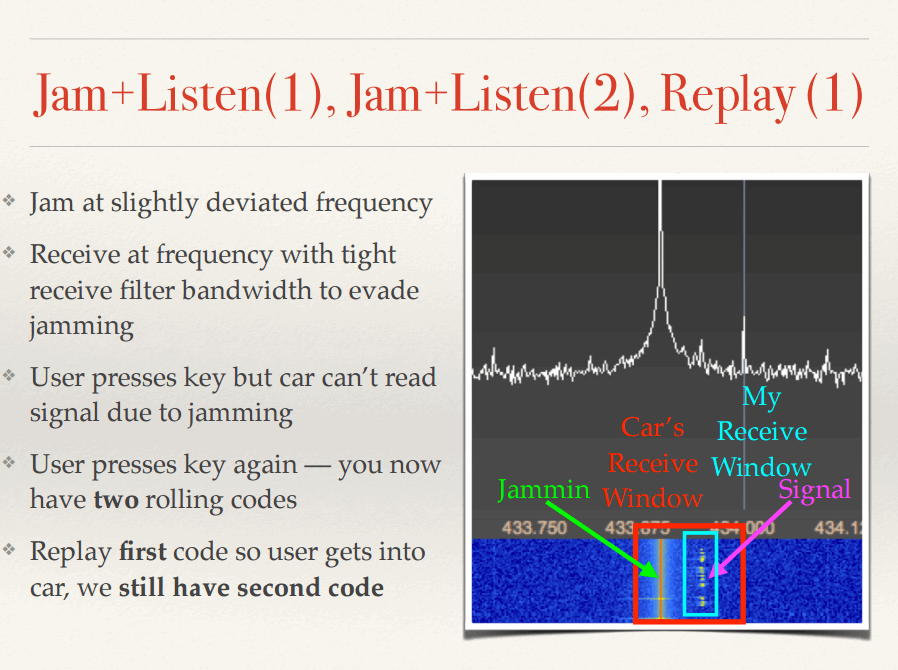
The replay attack itself is based on the rolljam idea. She uses two HackRF's, with one sitting closer to the car's receiver and jamming it, and another recording the car's keyfob. This prevents the car from incrementing the keyfob's rolling code, allowing it to be recorded and used again at a later time.
Charlie has also posted a video of her tests, which we embedded below.