RTL-SDR Tutorial: Analyzing GSM with Airprobe/GR-GSM and Wireshark
The RTL-SDR software defined radio can be used to analyze cellular phone GSM signals, using Linux based tools GR-GSM (or Airprobe) and Wireshark. This tutorial shows how to set up these tools for use with the RTL-SDR.
Example - Analysing GSM with RTL-SDR Software Defined Radio
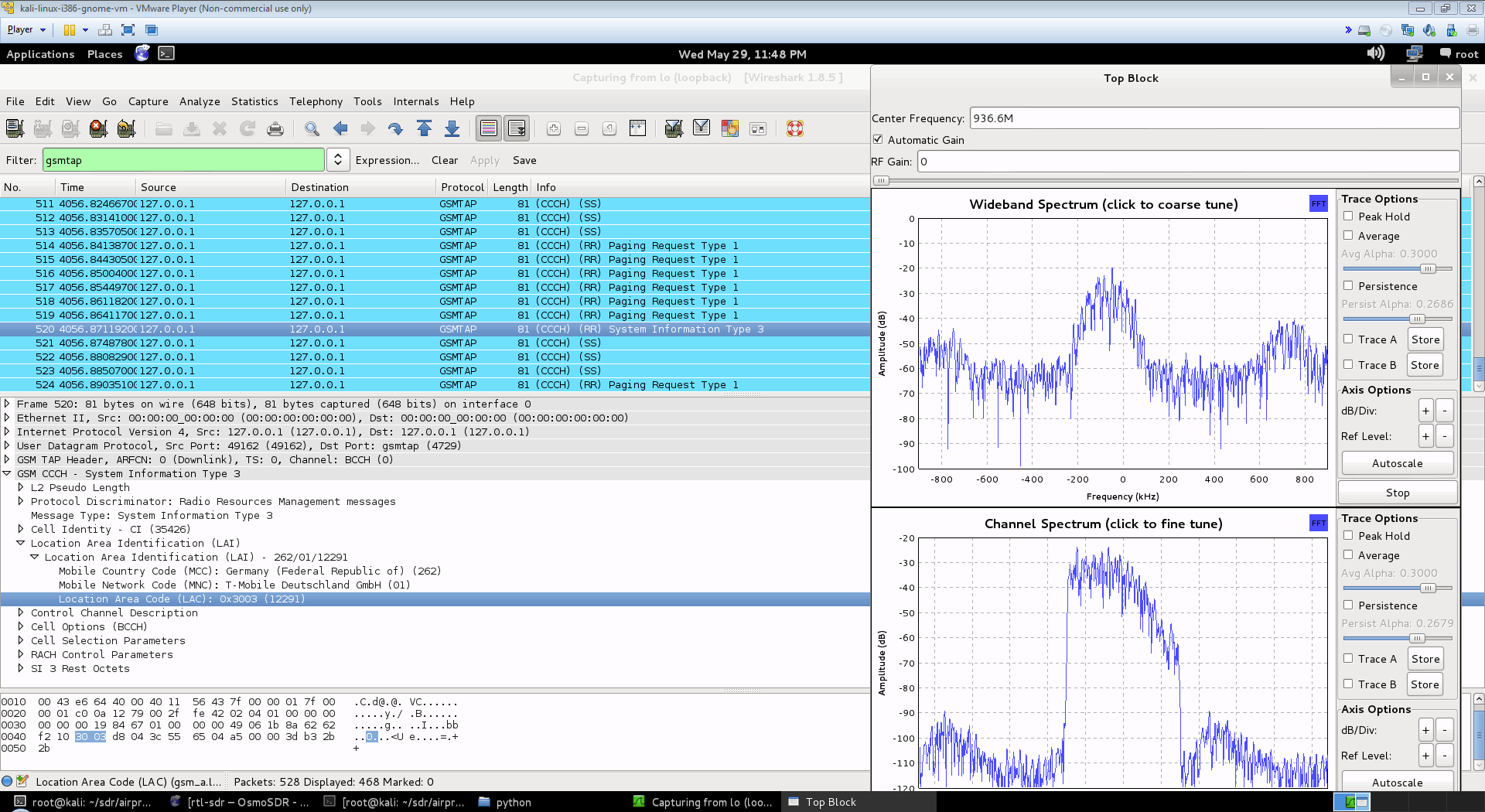
Here is a screenshot and video showing an example of the type of data you can receive. You can see the unencrypted GSM packet information. You will not be able to see any sensitive information like voice or text message data since that part is encrypted. Decryption of messages that are not your own is very difficult, illegal and is not covered in this tutorial.
 First, you will need to find out at what frequencies you have GSM signals in your area. For most of the world, the primary GSM band is 900 MHz, in the USA it starts from 850 MHz. If you have an E4000 RTL-SDR, you may also find GSM signals in the 1800 MHz band for most of the world, and 1900 MHz band for the USA. Open up SDRSharp, and scan around the 900 MHz (or 850 MHz) band for a signal that looks like the waterfall image below. This is a non-hopping GSM downlink signal. Using NFM, it will sound something like the example audio provided below. Note down the strongest GSM frequencies you can find.
First, you will need to find out at what frequencies you have GSM signals in your area. For most of the world, the primary GSM band is 900 MHz, in the USA it starts from 850 MHz. If you have an E4000 RTL-SDR, you may also find GSM signals in the 1800 MHz band for most of the world, and 1900 MHz band for the USA. Open up SDRSharp, and scan around the 900 MHz (or 850 MHz) band for a signal that looks like the waterfall image below. This is a non-hopping GSM downlink signal. Using NFM, it will sound something like the example audio provided below. Note down the strongest GSM frequencies you can find. 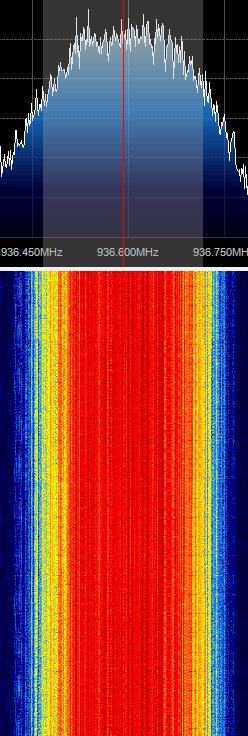
The rest of the tutorial is performed in Linux and we assume that you have basic Linux skills in using the terminal. For this tutorial we used Ubuntu 14.04 in a VMWare session. You can download the various ready to go Ubuntu VMWare images from here, and the free VMWare player from here. Note that virtual box is reported not to work well with the RTL-SDR, as its USB bandwidth capabilities are poor, so VMWare player should be used.
Install GR-GSM
This tutorial is heavily based on the instructions from the gr-gsm GitHub readme at https://github.com/ptrkrysik/gr-gsm.
- The easiest way to install gr-gsm is to use Pybombs. Pybombs will automatically install gr-gsm, and all the required dependencies including GNU Radio.
$ sudo apt-get update $ sudo apt-get install git python-pip $ sudo pip install PyBOMBS $ sudo pybombs prefix init /usr/local -a default_prx $ sudo pybombs config default_prefix default_prx $ sudo pybombs recipes add gr-recipes git+https://github.com/gnuradio/gr-recipes.git $ sudo pybombs recipes add gr-etcetera git+https://github.com/gnuradio/gr-etcetera.git $ sudo pybombs install gr-gsm $ sudo ldconfig
- Plug in your RTL-SDR and connect it to your VM if necessary. Run grgsm_livemon by typing grgsm_livemon at the terminal. A new window should open.
- In the new window tune to a GSM downlink frequency which you determined while browsing in SDR# and set the gain appropriately.
- Start Wireshark by using sudo wireshark -k -Y '!icmp && gsmtap' -i lo which will automatically start wireshark in the loopback mode with the gsmtap filter activated. You may get an error when opening Wireshark but this can be ignored.
- You should now see the GSM data scrolling along in Wireshark.
[expand title = "Old Method using Airprobe (Click to Expand)"]
Install GNU Radio
You will need to install GNU Radio first in order to get RTL-SDR to work. An excellent video tutorial showing how to install GNU Radio in Kali Linux can be found in this video shown below. Note that I had to run apt-get update in terminal first, before running the build script, as I got 404 not found errors otherwise. You can also use March Leech's install script to install the latest version of GNU Radio on any Linux OS. Installation instructions can be found here. I recommend installing from source to get the latest version. http://www.youtube.com/watch?v=B8Acp6_3DA0
Update: The new version 3.7 GNU Radio is not compatible with AirProbe. You will need to install GNU Radio 3.6. However, neeo from the comments section of this post has created a patch which makes AirProbe compatible with GNU Radio 3.7. To run it, place the patch file in your airprobe folder and then run patch -p1 < zmiana3.patch.
Install Airprobe
Airprobe is the tool that will decode the GSM signal. I used multiple tutorials to get airprobe to install. First from this University of Freiberg tutorial, I used their instructions to ensure that the needed dependencies that airprobe requires were installed.
Install Basic Dependencies
sudo apt-get –y install git-core autoconf automake libtool g++ python-dev swig libpcap0.8-dev
Update: Thanks to shyam jos from the comments section who has let us know that some extra dependencies are required when using the new Kali Linux (1.0.5) for airprobe to compile. If you've skipped installing GNURadio because you're using the new Kali 1.0.5 with SDR tools preinstalled, use the following command to install the extra required dependencies.
sudo apt-get install gnuradio gnuradio-dev cmake git libboost-all-dev libusb-1.0-0 libusb-1.0-0-dev libfftw3-dev swig python-numpy
Install libosmocore
git clone git://git.osmocom.org/libosmocore.git cd libosmocore autoreconf –i ./configure make sudo make install sudo ldconfig
Clone Airprobe
Now, I discovered that the airprobe git repository used in the University tutorial (berlin.ccc.de) was out of date, and would not compile. From this reddit thread I discovered a more up to date airprobe git repository that does compile. Clone airprobe using the following git command.
git clone git://git.gnumonks.org/airprobe.git
Now install gsmdecode and gsm-receiver.
Install gsmdecode
cd airprobe/gsmdecode ./bootstrap ./configure make
Install gsm-receiver
cd airprobe/gsm-receiver ./bootstrap ./configure make
Testing Airprobe
Now, cd into to the airprobe/gsm-receiver/src/python directory. First we will test Airprobe on a sample GSM cfile. Get the sample cfile which I found from this tutorial by typing into terminal.
cd airprobe/gsm-receiver/src/python wget https://svn.berlin.ccc.de/projects/airprobe/raw-attachment/wiki/DeModulation/capture_941.8M_112.cfile
Note: The tutorial and cfile link is sometimes dead. I have mirrored the cfile on megaupload at this link. Place the cfile in the airprobe/gsm-receiver/src/python folder. Now open wireshark, by typing wireshark into a second terminal window. Wireshark is already installed in Kali Linux, but may not be in other Linux distributions. Since Airprobe dumps data to a UDP port, we must set Wireshark to listen to this. Under Start in Wireshark, first set the capture interface to lo (loopback), and then press Start. Then in the filter box, type in gsmtap. This will ensure only airprobe GSM data is displayed. Back in the first terminal that is in the python directory, type in
./go.sh capture_941.8M_112.cfile
If everything installed correctly, you should now be able to see the sample GSM data in wireshark.
Receive a Live Channel
To decode a live channel using RTL-SDR type in terminal
./gsm_receive_rtl.py -s 1e6
A new window will pop up. Tune to a known non-hopping GSM channel that you found earlier using SDRSharp by entering the Center Frequency. Then, click in the middle of the GSM channel in the Wideband Spectrum window. Within a few seconds some GSM data should begin to show constantly in wireshark. Type ./gsm_receive_rtl.py -h for information on more options. The -s flag is used here to set the sample rate to 1.0 MSPS, which seems to work much better than the default of 1.8 MSPS as it seems that there should be only one GSM peak in the wideband spectrum window. 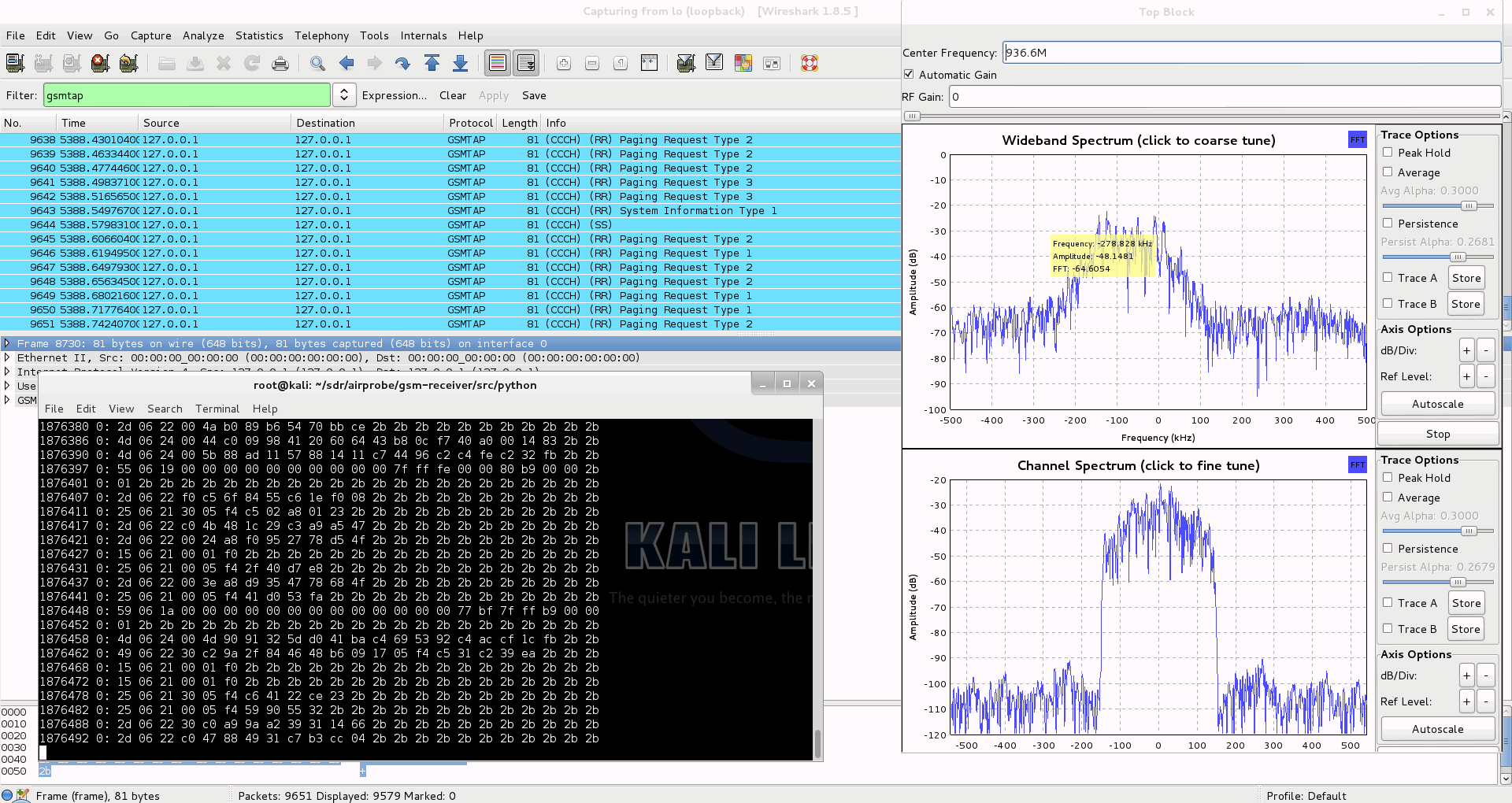
Capturing a cfile with the RTL-SDR (Added: 13/06/13)
I wasn't able to find a way to use airprobe to capture my own cfile. I did find a way to capture one using ./rtl_sdr and GNU Radio however. First save a rtl_sdr .bin data file using where -s is the sample rate, -f is the GSM signal frequency and -g is the gain setting. (rtl_sdr is stored in 'gnuradio-src/rtl-sdr/src')
./rtl_sdr /tmp/rtl_sdr_capture.bin -s 1.0e6 -f 936.6e6 -g 44.5
Next, download this GNU Radio Companion (GRC) flow graph (scroll all the way down for the link), which will convert the rtl_sdr .bin file into a .cfile. Set the file source to the capture.bin file, and set the file output for a file called capture.cfile which should be located in the 'airprobe/gsm-receiver/src/python' folder. Also, make sure that 'Repeat' in the File Source block is set to 'No'. Now execute the GRC flow graph by clicking on the icon that looks like grey cogs. This will create the capture.cfile. The flow chart will not stop by itself when it's done, so once the file has been written press the red X icon in GRC to stop the flow chart running. The capture.cfile can now be used in airprobe. However, to use this cfile, I found that I had to use ./gsm_receive.py, rather than ./go.sh as a custom decimation rate is required. I'm not sure why, but a decimation rate of 64 worked for me, which is set with the -d flag.
./gsm_receive.py -I rtl_sdr_capture.cfile -d 64
[/expand]
Going Further with Decryption
We don't cover how to decode the actual encrypted GSM data here, but this is possible to do with messages going to your own phone once you extract the encryption code for your sim card. But note that if you want to do this you'll need to put in some good study and research into understanding how GSM actually works before you can even think about trying it. Disclaimer: Only decrypt signals that you are legally allowed to (such as from/to your own cell phone) to avoid breaching privacy.
The most complete video guide is probably the YouTube tutorial by Crazy Danish Hacker, and the most complete web guide is the one by Domonkos P. Tomcsanyi available on his blog here.
A reader wrote in to let us know some information on obtaining the TMSI and Kc numbers, which are useful if you wish to go further and actually decode messages coming from your own phone. He writes:
For some reason, most of posts on the Internet concerning GSM sniffing provide very few examples of how to get our own TMSI and Kc numbers. These rely either on the BlackBerry engineering screen or the use of a SIM-card reader (see for example http://domonkos.tomcsanyi.net/?p=369). I know there are other methods like the one you describe in www.rtl-sdr.com/rtl-sdr-cell-phone-imsi-tmsi-key-sniffer/.
However, I have rarely seen anything related to the Android IMSI-Catcher Detector app. This can be easily installed via the standard repositories and it allows us to send AT commands to the modem provided we root the MS. This procedure works on many devices (I checked it on a Motorola Moto E).
Just a quick reminder of the basic AT+commands:
1. Extraction of IMSI -> AT+CRSM=176,28423,0,0,3.
2. Extraction of Ciphering Key Kc -> AT+CRSM=176,28448,0,0,9 (for SIM),
AT+CRSM=176,20256,0,0,9 (for USIM). First 16 entries.3. Extraction of TMSI -> AT+CRSM=176,28542,0,0,11. First 8 entries.
The Android IMSI-Catcher Detector provides some additional interesting data, like the cell ID the device is connected to, the LAI, etc.
We note that software such as SimSpyII together with a Sim Card reader can also be used to easily acquire the Kc value.
 If you enjoyed this tutorial you may like our book available on Amazon. Available in eBook and paperback formats. If you enjoyed this tutorial you may like our book available on Amazon. Available in eBook and paperback formats.
The Hobbyist's Guide to the RTL-SDR: Really Cheap Software Defined radio. |
https://teknokoodiradio.vuodatus.net/lue/2021/03/installing-gr-gsm-on-oracle-vm-virtualbox-ubuntu-18-04
Hi I was following your guide on debian linux. I would like to request that on this guide to help new users you post a disclaimer before the instructions in bold text to warn people how much software this is going to install and about the very likely possibility that this will not only take hours but also quite likely fail to build completely so that users like me don’t spend hours of wasted time researching things they don’t want to understand only to find out that their distribution of choice already has all the binary packages necessary to complete the job…. I just want to say that I appreciate you and your website and your research, however it would be quite a huge complement to your users if you could at least give them a heads up. And to say that the easaist way to install the gr-gsm program is to use PyBOMBS is a joke considering on debian sid at least it already has a binary install candidate in the repos………..!! BEWARE OTHER USERS!!!!!!
Agreed, it needs an update… Did you just volunteer 🙂
Currently there is one gr-gsm application that should work out of the
box and it is a more reliable replacement of Airprobe. The gr-gsm has
some similarities with it
I was successful Setting up GR-GSM in Ubuntu-20.04 for gnuradio-3.8 folowing the directions in https://pub.nethence.com/radio/gsm-install
For help, go to the gr-gsm google group https://groups.google.com/g/gr-gsm
anyone try these directions on a “skywave” install?
i get a boatload of dependency errors…
python version (2.7.12-1~16.04).
The following packages have unmet dependencies:
libuhd-dev : Depends: libuhd3.14.1 (= 3.14.1.0-0ubuntu1~xenial1) but it is not going to be installed
uhd-host : Depends: libuhd3.14.1 (= 3.14.1.0-0ubuntu1~xenial1) but it is not going to be installed
E: Unmet dependencies. Try ‘apt-get -f install’ with no packages (or specify a solution).
apt-get -f install didn’t fix anything on this install. manually attempting to install libuhd-dev and uhd-host doesn’t work either on this install.
any thoughts ?
update: 09.20.19
skywave 3.1.1 VMware VM, ubuntu 16.04/xenial
i think my repo list in sources.list was a bit off or something. put back the defaults (i think defaults):
deb http://archive.ubuntu.com/ubuntu/ xenial main restricted universe multiverse
deb http://security.ubuntu.com/ubuntu/ xenial-security main restricted universe multiverse
deb http://archive.ubuntu.com/ubuntu/ xenial-updates main restricted universe multiverse
deb http://archive.ubuntu.com/ubuntu/ xenial-proposed restricted multiverse main universe
ran apt-get update and then used the apt-get to install gr-gsm from howto at this link:
https://spz.io/2017/02/18/how-to-set-up-kali-linux-for-sniffing-gsm-traffic/
though written to install on kali it worked on my skywave 3.1.1 vm. at first, since i couldn’t get pybombs to run without errors i thought i’d try to gr-gsm installed on my kali vm but was finally able to get it to install on skywave. also, i read where one simple apt-get command to install gr-gsm works on ubuntu 18.04+ as mentioned on osmocom’s page:
https://osmocom.org/projects/gr-gsm/wiki/Installation
i executed ‘grgsm_livemon’ and it auto detected a RTL2838 dongel just fine on this skywave vm.
glad it installed … now to experiment.
I am not able to compile libosmocore, when I execute the following command I receive eror:
autoreconf -i -v
Output:
======
autoreconf: Entering directory `.’
autoreconf: configure.ac: not using Gettext
autoreconf: running: aclocal -I m4 –output=aclocal.m4t
autoreconf: ‘aclocal.m4’ is unchanged
autoreconf: configure.ac: tracing
autoreconf: configure.ac: not using Libtool
autoreconf: running: /usr/bin/autoconf
autoreconf: running: /usr/bin/autoheader
autoreconf: running: automake
syntax error at /usr/local/bin/automake line 986, near “$name (”
syntax error at /usr/local/bin/automake line 1147, near “$subr (”
BEGIN not safe after errors–compilation aborted at /usr/local/bin/automake line 3348.
autoreconf: automake failed with exit status: 255
when i lunch the grgsm_livemon===>>command not found
can you help me?
For anyone on Kali Rolling receiving an error when running
pybombs install gr-gsm
Durring the apache thrift configuration, this is because you specifically need libssl1.0-dev
Execute
apt-get install libssl1.0-dev
Then re-execute pybombs install gr-gsm
You’ll also need to modify one c file to use SSL 2.3 instead of 3.0
https://github.com/ptrkrysik/gr-gsm/issues/155
And you’ll need to install zlib
apt-get install zlib*
Thanks! That definitely helped me resolve all three issues (libssl1.0-dev, SSL 2.3 vs 3.0, and the zlib* issue).
Unfortunately, even after I ran all three of these the “pybombs install gr-gsm” found a new way to fail… Now when it gets to the part where it is trying to install gnuradio, it crashes with an error stating “This file requires compiler and library support for the ISO C++ 2011 standard…” I can do an apt install gnuradio and it works just fine, but I can’t get the pybombs install gr-gsm to run to completion. I’m running Kali 2017 rolling. I’m a total noob so sorry if I’m missing something obvious… Any help would be appreciated.
install zlib
Works installing zlib. Thanks
can we use any rtl-sdr to sniff sms
like this in hakshop https://hakshop.com/products/software-defined-radio-kit-rtl-sdr
Does rtl-sdr first transmit something – in order to receive the GSM packets ?
Do I have control on the power of transmit (for example if I want to have a small lab without receiving other remote mobiles packets) ?
The RTL-SDR is receive only, it cannot transmit. If you need transmit capabilities look into something like the HackRF, bladeRF, LimeSDR or USRP radios.
This actually sounds very interesting. Too bad I have ZERO skills at using Linux. Maybe somebody can tell me some steps I can take to do this in Windows. Would be AWESOME if some Windows software existed to do this same thing.
Is there any possibilities to do the project of Digital beacon receiver using the sdr in windows7 or windows10 using the MATLAB instead of GNU RADIO?
Hi, I am looking for a way to just count the number of cell phones around. No other info. Is there any way?
I too looking for this info. in car how many mobile phone present
if you have solution pls let me know
Me too! Seems you should need to scan across frequencies and capture specific packets to identify unique phones… Not sure how to do that though!
Hello, I have written a letter to the address github (https://github.com/ptrkrysik/gr-gsm/issues/198), but I still have not reseived the answer. Could you help me please to understand with decoding hopping channels! Thank you…
Whats the best budget sdr radio and antenna to use my budget is no more than $75 total cheaper is better?
I was thinking using an E400 chip with ANT500 Telescopic Antenna
anyone scuessfully achieved this and what equimpent have you used?
Just get one of our dongles with the antenna set https://www.rtl-sdr.com/store.
The R820T2 is better than the E4000 in most cases anyway, unless you need the higher frequencies it can provide.
Be sure to get an extrueded aluminum case, as you will be finding yourself with way too much noise otherwise. Also, don’t use a shitty antenna. Make sure your feedline is impedance matched, and well tightened and no loose connections. Keep your antenna away from other metal devices that may interfere with reception patterns, and consider learning to build your own antennas. You can do radio stuff for cheap, but you have to understand what you’re doing. Source: Ham radio operator for years. KF5EGM. Give your radio a proper ground other than your computer too. Your computer is noisy. Yes it’s all extra work but you’ll appreciate it in the end. Oh…and buy a high pass filter. Better yet get a band pass filter. It’s all pretty cheap and you can still probably stay under 75 bucks, especially if you make a few things yourself or shop around.
The issues around Kali Linux have beem resolved as of rolling release 2016.1, our tutorial is up on Kali.org at
https://forums.kali.org/showthread.php?29626-GSM-Capturing-Decoding-with-USRP-and-SDR-in-Kali-Linux-Rolling-Edition
Or directly linked and downloadable in .pdf from our google docs here
https://docs.google.com/document/d/1E_LQZ0xTs697L-0QsANQ7sDzc09QhO_7q4ue_WXezI0/pub
Feel free to contact us with any questions.
When I try to install gr-gsm through pybombs the following problem appears:
“PyBombs.sysutils – WARNING – deb_exists: could not find a downloadable version of libboost1.53-dev
Installing from source: boost”
The installation gets aborted and fails.
I’m pretty new to Linux and has hoping someone could help me with this.
If running pybombs config causes ‘NoneType’ object has no attribute ‘rfind’, you’ll need to modify the mod_pybombs/cfg.py to include this fix
hi
I’m trying to capture gsm packets by my rtlsdr dongle , but i only could capture ccch channel and I’m not able to capture any other packets , can any body tell me why is this ?? is that because of frequency hopping ?? or I’m missing something
thanks and sorry for weak english
Whe trying to runairprobe_rtlsdr.py i have this massage:
root@kali:~# airprobe_rtlsdr.pybash: airprobe_rtlsdr.py: command not found
gr-gsm successfully installed
wat does this mean?
I found the reason for the error, Kali Linux has unresolved installation issues and is not supported currently. Sadly …
Hi,
Is it possible to identify public IP’s being used in the area by sniffing these packets?
git clone https://github.com/ksnieck/airprobe.git
is an alternative link that can be used for downloading airprobe as the given link doesn’t work.
libpcsclite-dev
dependency is required for Kali Linux 1.1.0
Hi, can anyone please let me know where can i get gnu radio device which will work with this?
Thanks
Is anybody else getting this error:
I cant install airprobe/gsm-reciever.
When I try to “make” it gives me this error:
g++: error: ./gsm.cc: No such file or directory
g++: fatal error: no input files
compilation terminated.
make[4]: *** [_gsm_la-gsm.lo] Error 1
make[4]: Leaving directory `/root/airprobe/gsm-receiver/src/lib’
make[3]: *** [all-recursive] Error 1
make[3]: Leaving directory `/root/airprobe/gsm-receiver/src/lib’
make[2]: *** [all-recursive] Error 1
make[2]: Leaving directory `/root/airprobe/gsm-receiver/src’
make[1]: *** [all-recursive] Error 1
make[1]: Leaving directory `/root/airprobe/gsm-receiver’
make: *** [all] Error 2
I can’t find this gsm.cc file anywhere?!
I got the same error.
did u already managed to compile it?
I fond another airprobe src, compiling fine…. but there are some other issues.
I had this issue to, and the “no module named _GSM”
Turns out the error was caused by using an out of date/old version of Airprobe, that wasnt compiling correctly. Since gnumonks was gone I had to find another on that would compile correctly – I got it working with this one:
Github
I cloned the same repo on github but still I am getting the same error “ImportError: No module named _gsm” . Please let me know if something else needs to be done.
hi,please help me,thanks.
root@kali:~/airprobe/gsm-receiver/src/python# ./gsm_receive_rtl.py -s 1e6
Traceback (most recent call last):
File “./gsm_receive_rtl.py”, line 22, in
import osmosdr
ImportError: No module named osmosdr
Hi, I followed all the steps and it works nicely until I click in the wideband spectrum window. It just doesn’t do anything, it doesn’t show anything on wirehsark either. I’m using a HackRF, what could be the problem?
Also tried in Kali 1.0.8 vm and get:
linux; GNU C++ version 4.7.2; Boost_104900; UHD_003.005.003-0-unknown
Traceback (most recent call last):
File “./gsm_receive_rtl.py”, line 27, in
import gsm
File “../lib/gsm.py”, line 26, in
_gsm = swig_import_helper()
File “../lib/gsm.py”, line 18, in swig_import_helper
import _gsm
ImportError: libosmocore.so.5: cannot open shared object file: No such file or directory
Anybody any ideas how to make this work in Kali 1.0.8?
Answered my own problem. Run the following if using Kali 1.0.8 before the airproble download and setup:
sudo ln -s /usr/local/include/gruel/swig/gruel_common.i /usr/local/include/gnuradio/swig/ && ldconfig
seems to be working on my VM now 🙂
hi
to day i installed kali linux 1.0.8 with gnuradio preinstalled i follow the totrial how to install airprobe and apply the patch zmiana.patch all thing work fine but when i apply the test of airprobe i go this message:
Traceback (most recent call last):
File “./gsm_receive.py”, line 11, in
import gsm
File “../lib/gsm.py”, line 26, in
_gsm = swig_import_helper()
File “../lib/gsm.py”, line 18, in swig_import_helper
import _gsm
ImportError: No module named _gsm
please help me i have 5 days try
!!IMPORTANT!!
hey,
my name is hans and ive got a simple question (im a newbie in this section):
Is it possible to detect the count of smartphones near me with gsm analyzazion?
and if not, could u imagine some way to do this?
i know its not that easy, but ive several months to do this – i just need to know its possible 😀
regards,
hans
Hi Hans, what area are you in?
hi,
i’m made cfile with a terratec e4000 usb card, but unfortunately i cant find a way how to decode this. when i write “./go.sh /tmp/capture-rtl-sdr.cfile 64 1S” everything looks fine in console, but in wireshark have nothing. Instead of when write “./go.sh /tmp/capture-rtl-sdr.cfile 64 0C” then wireshark show traffic but not system information 5 or 6
https://mega.co.nz/#!8UtxEAwD!GbUW8vkhPspAUtRuI3RaCuhJR3aWOpmbnj0NnLq8cIM
so im uploaded my cfile, and if somebody can try and eventually find where im in wrong, i will appreciate
Hi
I had been using gsm_receive_rtl.py with version 1 of zmiana patch, and it worked OK. However, I couln’t make go.sh work with any capture file, like capture_941.8M_112.cfile or vf_call6_a725_d174_g5_Kc1EF00BAB3BAC7002.cfile.
Now I read neeo comment about a new patch version and I applyed it, but I got same rerults: gsm_receive_rtl.py working OK but file decoding not working. Neeo, what options should I use to try with vf_call6_a725_d174_g5_Kc1EF00BAB3BAC7002.cfile, which is the file should work, isn’t it? Thanks!
you need to change clock_rate in python code to 100e6, and use decim = 174 for vf_call6_a725_d174_g5_Kc1EF00BAB3BAC7002.cfile
Then I removed “-I”
and get:
configure.ac:16: required file `./config.guess’ not found
configure.ac:16: `automake –add-missing’ can install `config.guess’
configure.ac:16: required file `./config.sub’ not found
configure.ac:16: `automake –add-missing’ can install `config.sub’
configure.ac:5: required file `./install-sh’ not found
configure.ac:5: `automake –add-missing’ can install `install-sh’
configure.ac:16: required file `./ltmain.sh’ not found
configure.ac:5: required file `./missing’ not found
configure.ac:5: `automake –add-missing’ can install `missing’
src/Makefile.am: required file `./depcomp’ not found
src/Makefile.am: `automake –add-missing’ can install `depcomp’
autoreconf: automake failed with exit status: 1
I get this: autoreconf: ‘configure.ac’ or ‘configure.in’ is required
after “autoreconf –i”
hey all ,
excuse me because of reapiting this question !
when i run the ./gsm_receive_rtl.py i take this error :
inux; GNU C++ version 4.7.2; Boost_104900; UHD_003.005.003-0-unknown
gr-osmosdr v0.0.x-xxx-xunknown (0.0.3git) gnuradio 3.6.5.1
built-in source types: file fcd rtl rtl_tcp uhd hackrf
FATAL: Failed to open HackRF device (-5) HACKRF_ERROR_NOT_FOUND
Trying to fill up 1 missing channel(s) with gaussian noise.
This is being done to prevent the application from crashing
due to a gnuradio bug. The maintainers have been informed.
sample rate: 0
Traceback (most recent call last):
File “./gsm_receive_rtl.py”, line 230, in
tb = top_block()
File “./gsm_receive_rtl.py”, line 85, in __init__
taps = gr.firdes.low_pass(1.0, sample_rate, 145e3, 10e3, gr.firdes.WIN_HANN)
File “/usr/lib/python2.7/dist-packages/gnuradio/gr/gnuradio_core_general.py”, line 9493, in low_pass
return _gnuradio_core_general.firdes_low_pass(*args, **kwargs)
IndexError: gr_firdes check failed: sampling_freq > 0
whould you please tell me exactly how could i solve this problem ?
—————————–
and , another question is that when i run patchs , it asks me a File name and i give the file name but it asks for ignoring them ,
—————————————————-
please tell me how to do patchs !
soooo sooorryy and tnxxxx a lot for ans.
———————————————
I have installed this on Kali 1.0.6 in VirtualBox, however when I run ./gsm_receive_rtl.py -s 1e6 after detecting the RTLSDR I have an error thrown;
Traceback (most recent call last):
File “/usr/lib/python2.7/dist-packages/gnuradio/wxgui/plotter/plotter_base.py”, line 203, in _on_paint
for fcn in self._draw_fcns: fcn[1]()
File “/usr/lib/python2.7/dist-packages/gnuradio/wxgui/plotter/plotter_base.py”, line 63, in draw
GL.glCallList(self._grid_compiled_list_id)
File “/usr/lib/python2.7/dist-packages/OpenGL/error.py”, line 208, in glCheckError
baseOperation = baseOperation,
OpenGL.error.GLError: GLError(
err = 1280,
description = ‘invalid enumerant’,
baseOperation = glCallList,
cArguments = (1L,)
)
Thanks in advance for any help.