Defcon 2020 Online Talks: Satellite Eavesdropping & Detecting Fake 4G Base Stations
DEFCON 2020 was held online this year in and the talks were released a few days ago on their website and on YouTube. If you weren't already aware Defcon is a major yearly conference all about information security, and some of the talks deal with wireless and SDR topics. We found two very interesting SDR and wireless related talks that we have highlighted below. The first talk investigates using commercial satellite TV receivers to eavesdrop on satellite internet communications. The second discusses using a bladeRF or USRP to detect fake 4G cellphone basestations. Slides for these talks are available on the Defcon Media server under the presentations folder.
DEF CON Safe Mode - James Pavur - Whispers Among the Stars
Space is changing. The number of satellites in orbit will increase from around 2,000 today to more than 15,000 by 2030. This briefing provides a practical look at the considerations an attacker may take when targeting satellite broadband communications networks. Using $300 of widely available home television equipment I show that it is possible to intercept deeply sensitive data transmitted on satellite links by some of the world's largest organizations.
The talk follows a series of case studies looking at satellite communications affecting three domains: air, land, and sea. From home satellite broadband customers, to wind farms, to oil tankers and aircraft, I show how satellite eavesdroppers can threaten privacy and communications security. Beyond eavesdropping, I also discuss how, under certain conditions, this inexpensive hardware can be used to hijack active sessions over the satellite link.
The talk concludes by presenting new open source tools we have developed to help researchers seeking to improve satellite communications security and individual satellite customers looking to encrypt their traffic.
The talk assumes no background in satellite communications or cryptography but will be most interesting to researchers interested in tackling further unsolved security challenges in outer space.
DEF CON Safe Mode - Cooper Quintin - Detecting Fake 4G Base Stations in Real Time
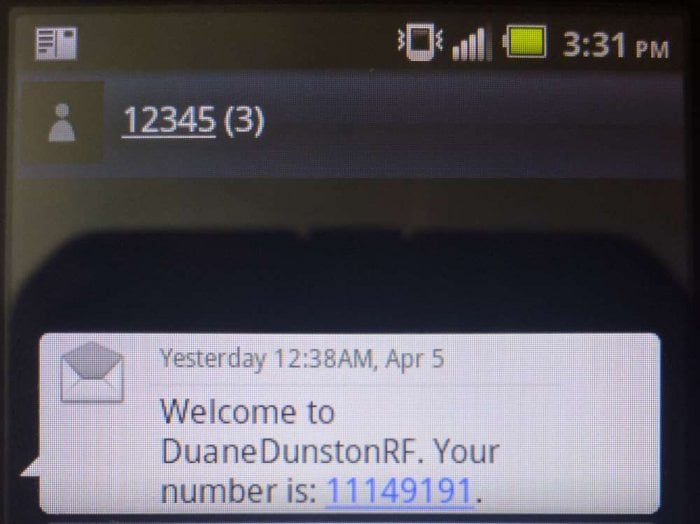
4G based IMSI catchers such as the Hailstorm are becoming more popular with governments and law enforcement around the world, as well as spies, and even criminals. Until now IMSI catcher detection has focused on 2G IMSI catchers such as the Stingray which are quickly falling out of favor.
In this talk we will tell you how 4G IMSI Catchers might work to the best of our knowledge, and what they can and can't do. We demonstrate a brand new software project to detect fake 4G base stations, with open source software and relatively cheap hardware. And finally we will present a comprehensive plan to dramatically limit the capabilities of IMSI catchers (with the long term goal of making them useless once and for all).
GitHub: https://github.com/EFForg/crocodilehunter