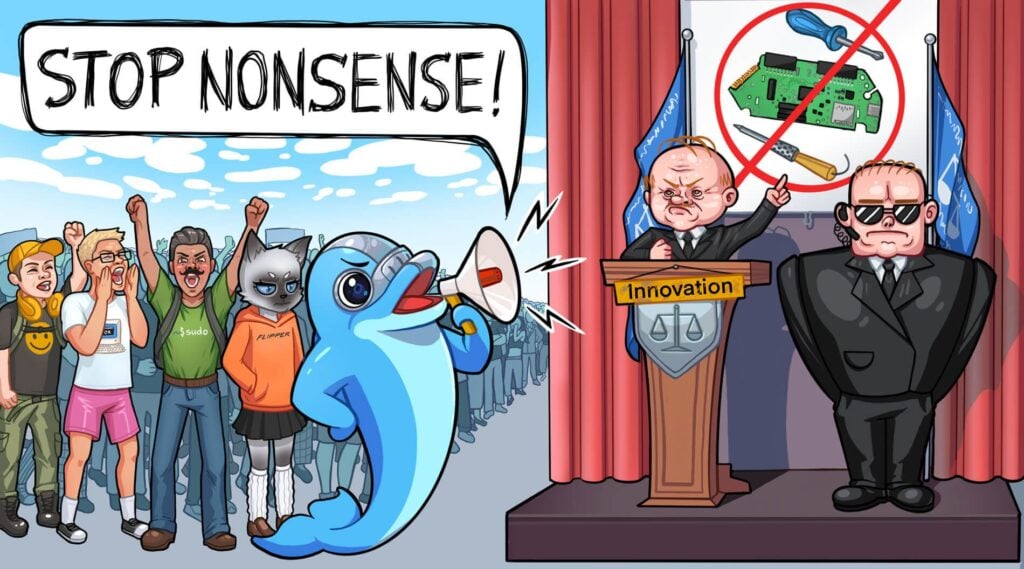
Dominic LeBlanc, Canada's Minister of Public safety has recently declared that they plan to ban devices "used to steal vehicles by copying the wireless signals for remote keyless entry, such as the Flipper Zero". The text specifically calls out the Flipper Zero, however the wording appears to imply that any device that can copy a signal will be banned. This means the ban could extend to RX/TX SDRs like the HackRF and possibly even RX only SDRs like RTL-SDRs.
The Flipper Zero is an affordable handheld RF device for pentesters and hackers. It is not based on SDR technology, however it uses a CC1101 chip, a digitally controlled RX/TX radio that is capable of demodulating and modulating many common digital modulations such as OOK/ASK/FSK/GFSK/MSK at frequencies below 1 GHz. There are many CC1101 devices on the market, but the Flipper Zero has gained huge popularity on social media because of it's excellent software support, as well as its cute marketing tactic. In the past it was even featured on the popular Linus Tech Tips YouTube channel.
Flipper Zero has had a long line of setbacks including PayPal freezing 1.3M of its cash, and US customs temporarily seizing its shipments, then passing a $70,000 bill on to them for storage fees and Amazon banning the product on their marketplace.
In our opinion, we believe that the ban appears to be misguided. The Flipper Zero is a basic device that can only perform a simple replay attack, which is to record a signal, and replay it at a later time. These sorts of attacks do not work on vehicles built after the 90's which now use rolling codes or more sophisticated security measures. To defeat rolling code security, a more sophisticated attack called Rolljam can be used. A Rolljam device can be built for $30 out of an Arduino and two cheap transceiver modules.
However, according to arstechnica the biggest cause for concern in terms of car theft is a different sort of attack called "signal amplification relay".
The most prevalent form of electronics-assisted car theft these days, for instance, uses what are known as signal amplification relay devices against keyless ignition and entry systems. This form of hack works by holding one device near a key fob and a second device near the vehicle the fob works with. In the most typical scenario, the fob is located on a shelf near a locked front door, and the car is several dozen feet away in a driveway. By placing one device near the front door and another one next to the car, the hack beams the radio signals necessary to unlock and start the device.
This sort of attack is a lot less sophisticated in many ways as all you are doing is amplifying a signal, and no clever hardware like the Flipper Zero or a software defined radio is even required. The X video below demonstrates such a hack where a criminal holds up a loop antenna to a house. The loop antenna is connected to a signal amplifier which amplifies the keyfob signal, tricking the car into thinking the keyfob is nearby, and allowing the door to be unlocked by touching the handle, and then turned on with the push to start button.
Flipper zero note that they have not been consulted about the ban, and replied on X stating that they are not aware of the Flipper Zero being used for car theft.