HackRF Blue: A Lower Cost HackRF
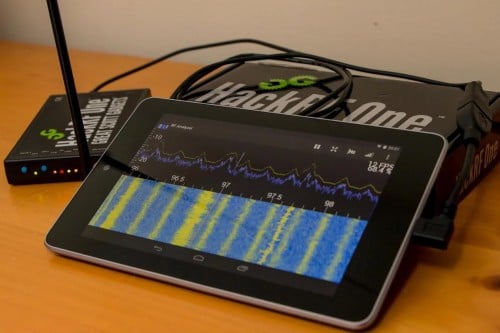
Earlier in the year the HackRF One was released by Micheal Ossmann. It is a transmit and receive capable software defined radio with a 10 MHz to 6 GHz range which currently sells for around $300 USD. Since the HackRF is open source hardware, anyone can make changes to the design and build and sell their own version.
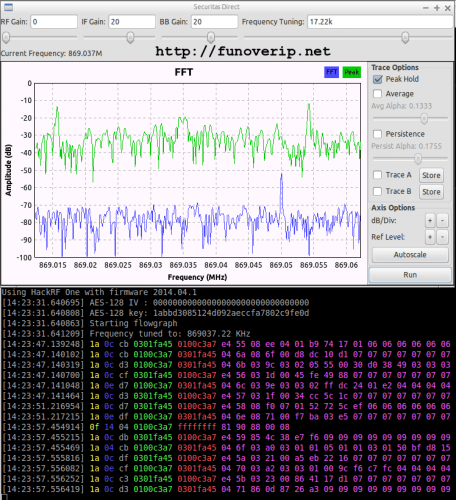
The HackRF Blue is a HackRF clone that aims to sell at a lower cost. By sourcing lower cost parts that still work well in the HackRF circuit, the team behind the HackRF Blue were able to reduce the price of the HackRF down to $200 USD. They claim that the HackRF Blue has the same performance as the HackRF One and is fully compatible with the HackRF software. They are currently seeking funding through an IndieGoGo campaign.
Their main goal through the funding is to help provide underprivileged hackerspaces with a free HackRF.