WeatherSense: A Wireless 433 MHz Weather Station with RTL-SDR Receiver
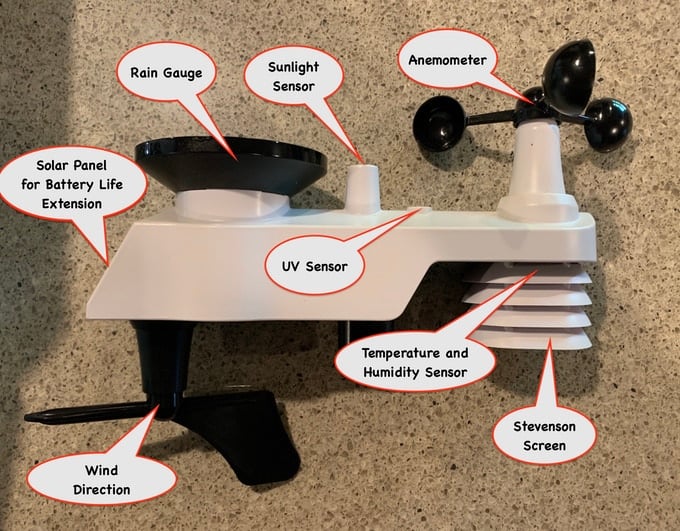
Over on Kickstarter we've recently come across a project called "WeatherSense" which is currently being crowdfunded. WeatherSense is a custom built set of 433 MHz wireless weather sensors made for makers. The outdoor "WeatherRack2" unit includes sensors and features like an anemometer, sunlight sensor, rain gauge, UV sensor, temperature and humidity sensor. wind direction sensor, as well as a solar panel for battery life extension and a Stevenson screen for shielding. They also have indoor units that measure temperature and humidity.
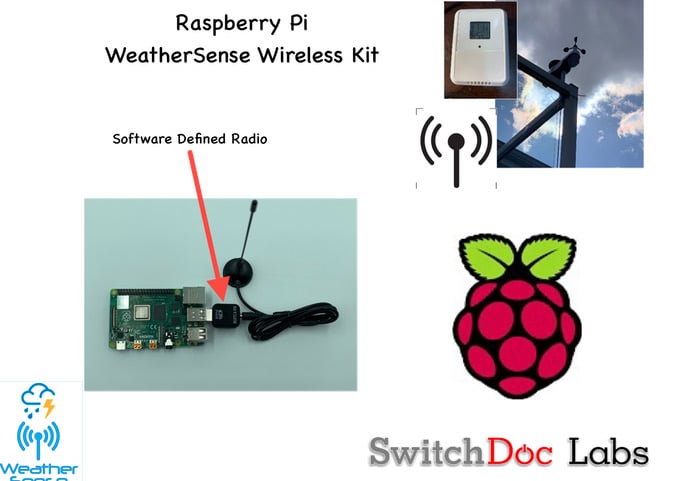
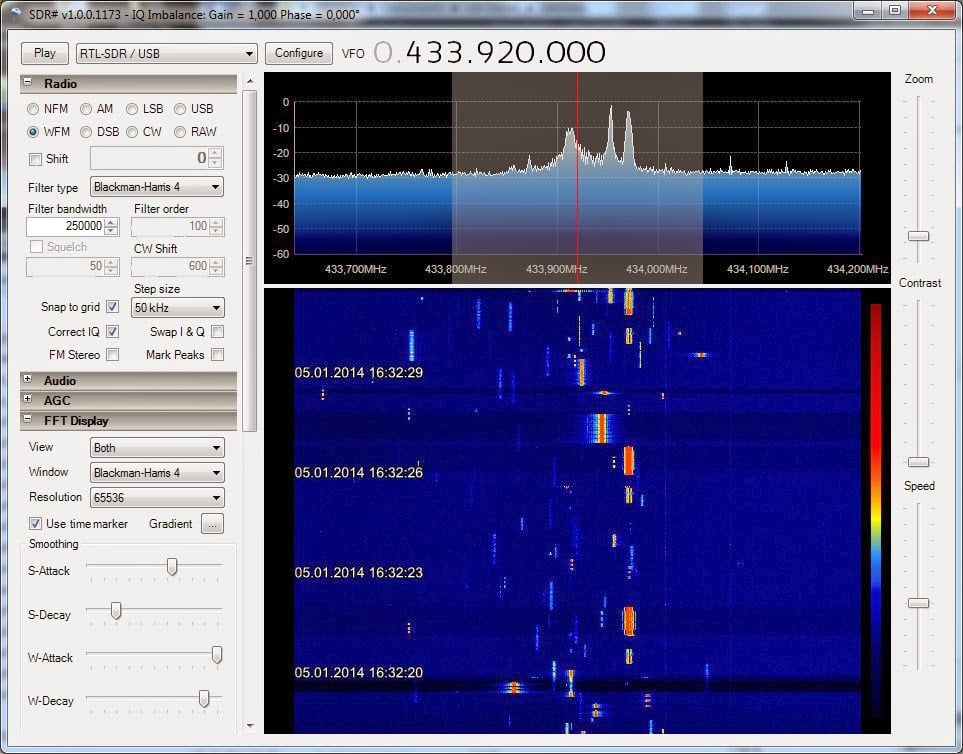
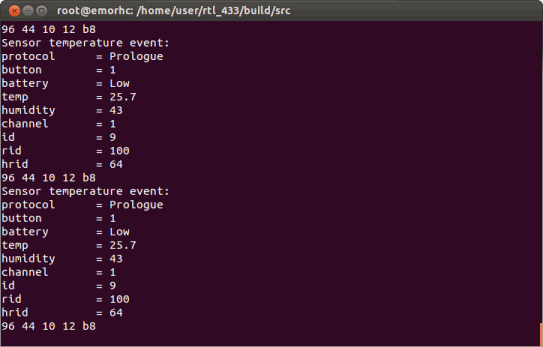
What's interesting to us is that they are using an RTL-SDR + Raspberry Pi as part of their 433 MHz receiver system. Their system includes a Raspberry Pi SD card image with built in Python software that is used with the RTL-SDR for receiving and decoding the weather sensor signals. They also provide an option for a simpler Arduino + 433 MHz receiver kit if you didn't want to use an SDR.
The campaign is currently fully funded, with 6 days left in the campaign. A kit including RTL-SDR and WeatherRack2 currently costs US$126 + shipping.