RSA Conference Talks: IOT Hacking with SDR, Tracking Rogue RF Devices & Wireless Offense and Defense
RSA Conference is an information security event that was recently held on March 4 - 8 in San Francisco. The talks have been uploaded to YouTube and from what we see there are three interesting SDR/RF related talks that may be worth looking at, which we show below. The full list of videos can be found on their YouTube channel.
RF Exploitation: IoT and OT Hacking with Software-Defined Radio
Harshit Agrawal, Security Researcher, MIT Academy of Engineering, SPPU
Himanshu Mehta, Team Lead (Senior Threat Analysis Engineer), Symantec
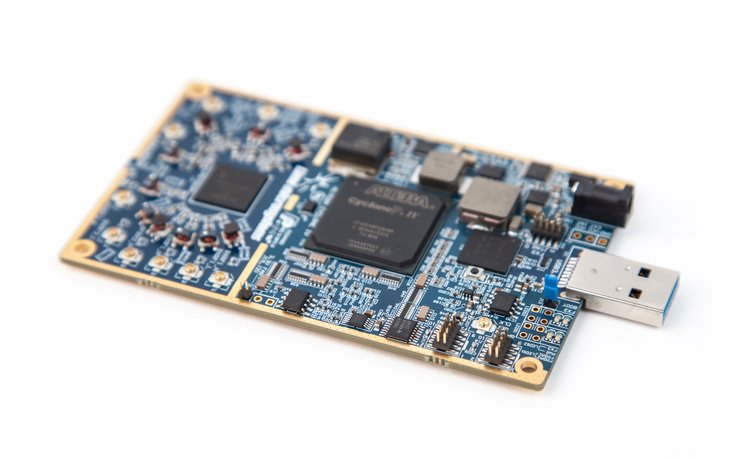
Recent years have seen a flood of novel wireless exploits, from vulnerable medical devices to hacked OT devices, with exploitation moving beyond 802.11 and into more obscure standard and proprietary protocols. While other non-WiFi RF protocols remain a mystery to many security practitioners, exploiting them is easier than one might think. SDR is changing the game for both offense and defense.Learning Objectives:1: Become familiar with common security concerns and attack surfaces in a wireless communication system.2: Understand the ease and prevalence of wireless exploitation, with sophisticated examples.3: Learn to view IoT devices, security and privacy collectively.
Hunting and Tracking Rogue Radio Frequency Devices
Eric Escobar, Principal Security Consultant, SecureWorks
Rogue radio frequencies pose a substantial and often overlooked threat to both organizations and targeted individuals. This talk will explore the dangers of rogue radio frequencies and highlight tactics, techniques and tools which can be used to identify and locate potential threats.Learning Objectives:1: Understand the major ways rogue wireless frequencies can impact an organization.2: Develop a basic understanding of how to locate a rogue wireless signal.3: Gain a conversational knowledge of ways to identify and track a wireless signal.Pre-Requisites:Basic understanding of security principles. Basic understanding of wireless communication. Basic understanding of computer networks.
Wireless Offense and Defense, Explained and Demonstrated!
Rick Farina, Senior Product Manager, WLAN Software Security, Aruba
Rick Mellendick, Chief Security Officer, Process Improvement Achievers LLCThis session will discuss the use of radio frequency, often overlooked for network enumeration and attack. The techniques to be discuss are used to identify authorized and unauthorized signals in an organization. Without understanding the offensive attacks an organization can’t perform effective defense. The talk will explain and demonstrate how to enumerate and gain access to resources through RF signals.Learning Objectives:1: Understand that wireless doesn’t just mean WiFi.2: Understand that the Bluetooth protocol can allow for direct attacks against phones, PCs and other devices.3: Learn that other RF attacks are very difficult to detect, and gain an understanding of what they look like.Pre-Requisites:The biggest prerequisite for our talk is an open mind and the ability to understand risk, and after the talk to better assess risk on your environment.