Demonstrating How Speakers Can Become an Unintentional RF Transmitter
Over on YouTube channel Privacy & Tech Tips has uploaded a video showing how he used an RTL-SDR to pick up RF emissions coming from some speakers that were unintentionally acting as wireless microphones. He goes on to show how you can clean up the noisy received audio in Audacity using the noise reduction filter.
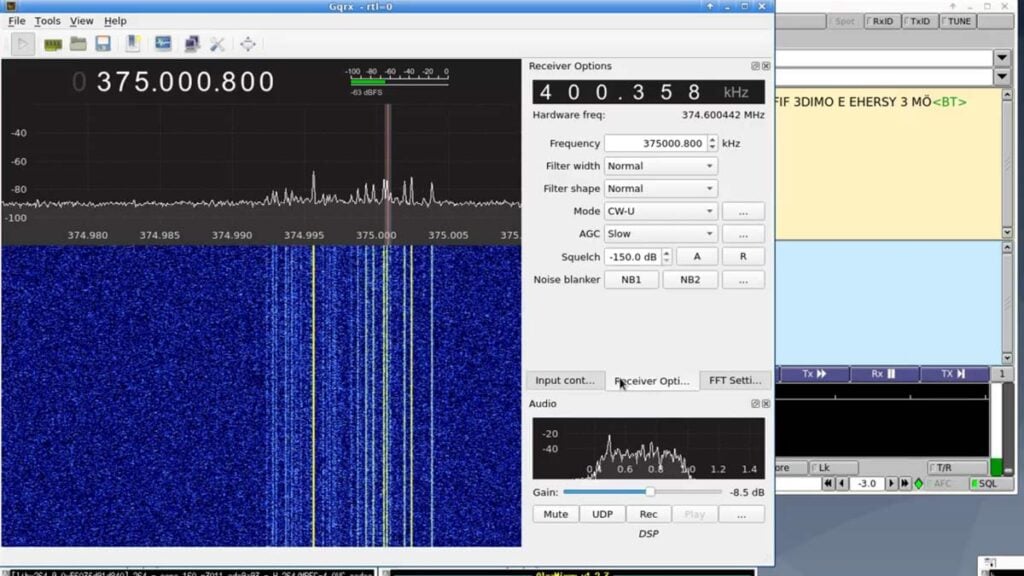
I show how electromagnetic emissions from personal devices many times turn our devices into (potential) remote listening + transmitting devices when active (as demonstrated). I discovered my speakers unintentionally transmitting audio (speaker acting as microphone) to a few different frequencies via GQRX recording (computer/Pinetab microphones completely disabled).
There are a few frequencies you can tune into to listen in remotely. This includes listening in to conversations in the room as the speaker also acts as a microphone when playing sound (***tested only on my own devices***).
When the speaker volume is turned down, the signal goes down and the broadcast goes away. When the speaker volume is down, it no longer functions as a remote microphone + transmitter.
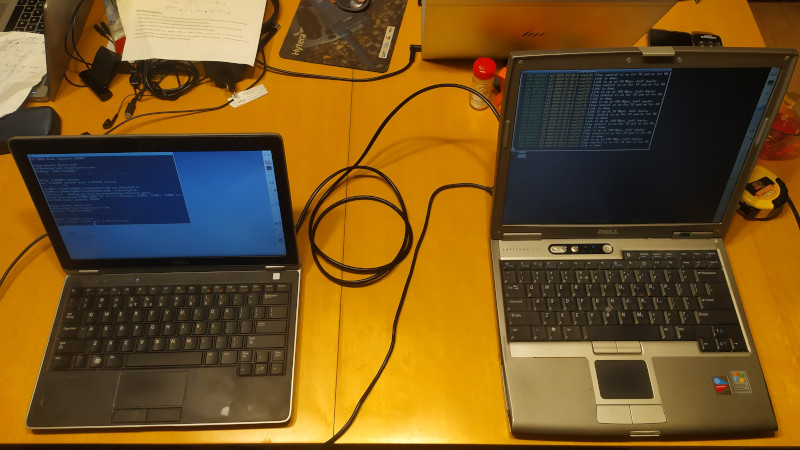
We use Audacity to clean up the audio. GQRX is used to record the signals which are filtered on the Pinetab with internal RTL-SDR. Audio processing/noise reduction done running Parrot Linux using Audacity.
We touch on the fact all electronic devices give off their very own unique electromagnetic emissions which can act as device signatures (strength depends on shielding).
Sometimes speaker wire not properly shielded (as is found in most PC's) can act as a radio transmitter antenna without user knowledge. Here I discovered a few frequencies broadcasting the audio live (.25 second delay for SDR modulation).