Crimean Resident Arrested under Accusation of Spying for Ukraine with RTL-SDR Dongles
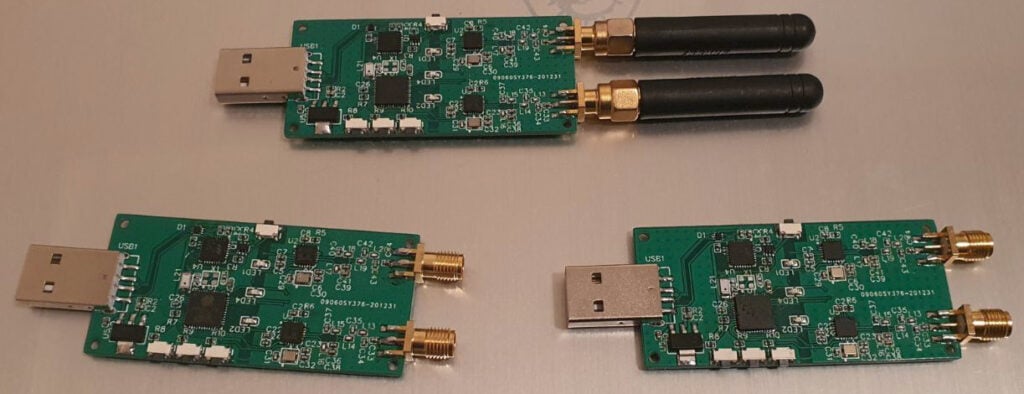
Back in early 2014 Crimea was annexed from the Ukraine by Russian forces. Recently we've heard news that a Crimean resident was arrested by the Russian Federal Security Service under the suspicion of being a Ukrainian informant who was intending to transfer, or was transferring military data abroad using RTL-SDRs.
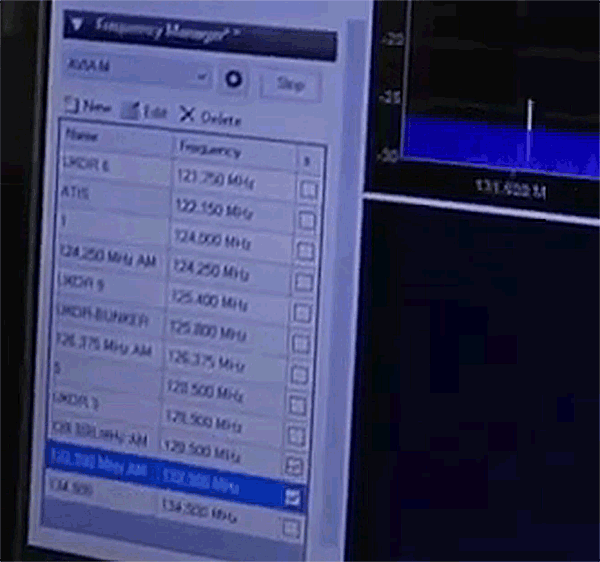
A video of the arrest has been uploaded to YouTube, and RTL-SDR dongles running with the Airspy SDR# software on his laptop can clearly be seen as having been photographed. The photos of the SDR# screen appear to show that he was monitoring the commercial aviation band with a scanner plugin.
The YouTube description is translated below:
Today it was reported about the arrest of a Crimean resident, either intending to transfer, or transferring military data abroad.
The FSB has published footage of the arrest. The time on the laptop caught on the video during the search of housing 07:40 date 06/22/21. The laptop is turned on, the AIRSPY radio frequency scanning program is running, the laptop is in the dust - only traces of pressing some keys are visible, and the touchpad was not used. There are many icons in the room, books on radio engineering, a Ukrainian flag, aircraft models, several pennants "Tavria 1958", an ICOM IC-R6 radio, maps.
The detainee transferred the information received to Ukraine on one basis, collected it on the other and intended to transfer it.
The court sent the man to the pre-trial detention center for 2 months. If his guilt is proven, then high treason "shines" and does not shine to see the will for 25 years.
According to an article on RadioFreeEurope, the man was detained as he was "collecting data on the flights of Russian military planes for Ukrainian intelligence".
It is unclear if the man was knowingly providing intelligence services, or is simply an aviation hobbyist caught up in politics. If anyone has more information about his story, please let us know in the comments.
UPDATE 29 June 2021: More information on the story at this link.

This is a reminder to those in politically dangerous situations to take care when using SDRs. In the past we have seen a Slovenian researcher almost jailed for performing University research with an RTL-SDR, a UN expert arrested for possessing an RTL-SDR in Tunisia, and SDRs come under fire when Trump tweeted a now-debunked conspiracy theory on how an RTL-SDR was being used as a close range scanner by the black lives matter protestor who was shoved to the ground on video by Buffalo police.