Reverse Engineering and Controlling a Wireless Doorbell with an RTL-SDR and Arduino
Thank you to Shreyas Ubale for submitting his blog post about reverse engineering a wireless doorbell, and then performing a replay attack. Shreyas had purchased a wireless doorbell set containing one button transmitter and two bell receivers. However, his situation required two transmitters, one for visitors at the door, and one to be used by family within his house.
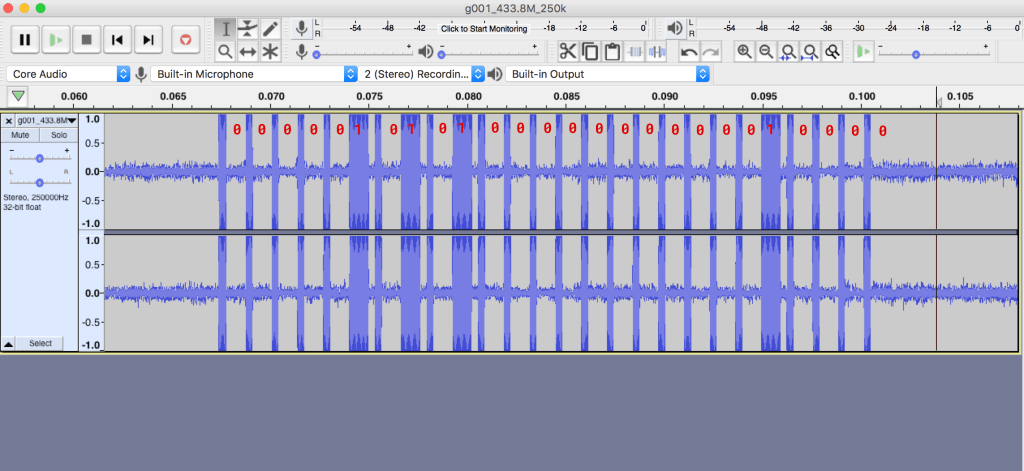
In order to create a second transmitter he decided to reverse engineer the doorbells wireless signal, and use that information to create an Arduino based transmitter. His process involves first using an RTL-SDR to determine the transmission frequency, then using the rtl_433 software to capture the raw waveform which he then analyzes manually using Audacity. Once the binary string, length and pulse width is known he is able to program an Arduino connected to a 433 MHz transmitter to replicate the signal.
In future posts Shreyas hopes to explore other ways to transmit the signal, and eventually design a simple but configurable 433 MHz push button that supports RF, WiFi, and can support the IFTTT web service.
If you're interested, check out some of our previous posts that highlight many other successful reverse engineering experiments with RF devices and SDR.