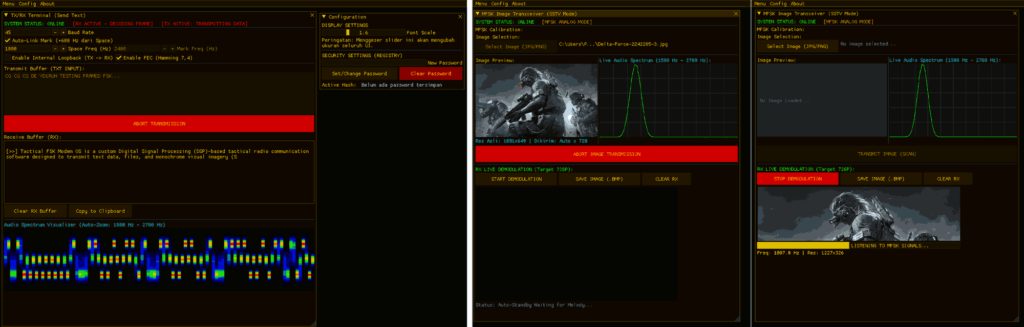
Tactical_FSK_Modem: An Open Software MFSK Image & Text Modem for PC and Android
Thanks to Ibrahim (YD1RUH), who wrote in to share his open-source open-software project Tactical_FSK_Modem, which turns a standard PC or Android device into an audio-based MFSK transceiver for sending images and text over a radio link. Conceptually similar to SSTV or HF FAX, it adds Hamming (7,4) Forward Error Correction that wraps every 4 data bits into a 7-bit block and repairs single-bit errors in real time, significantly lowering BER in low-SNR conditions. The system forces a hardened 720p vertical resolution for noise resistance, and a 1400 Hz → 1000 Hz → 1400 Hz VIS-like "start melody" handles automatic RX canvas reset and sync with no manual alignment.
Pre-built Windows and Android binaries are available in the repo, and the Android port is probably the most interesting part. Operators can connect a smartphone to HT, ham radio, or an SDR to send tactical images directly from the field.
We note that while the code is Apache 2.0 licensed, we don't appear to see any source code in the repo, but the .exe and .apk files are available to download. Ibrahim notes that he is actively looking for feedback and collaboration to further improve the system's robustness for tactical and emergency communication use cases.
Licensing Update: Ibrahim has clarified that he mistakenly referred to the project as open-source, but his intention was to actually refer to it as 'open-software'. The software is free, but the source code is not provided.