DragonOS: KerberosSDR Bearing Server Setup with RDFMapper
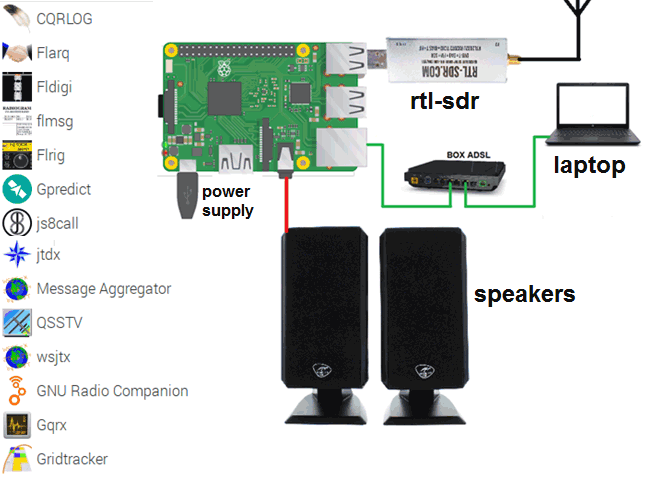
DragonOS is a ready to use Linux OS image that includes many SDR programs preinstalled and ready to use. The creator Aaron also runs a YouTube channel that has multiple tutorial videos demonstrating software built into DragonOS.
In a recent video Aaron has provided a two part tutorial showing how to set up and use KerberosSDR with the RDFMapper software on DragonOS. This allows you to network multiple KerberosSDR units together and display each units radio bearing on the same map. Two or more bearings crossing can be used to determine the location of a transmitter. In the future Aaron will use this setup to have multiple mobile and fixed KerberosSDR units connected together via Zero Tier. Aaron writes:
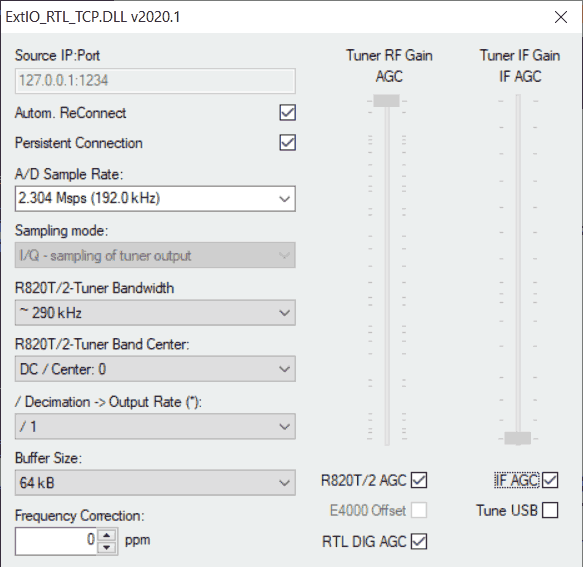
In this first video I show how to install software to control the KerberosSDR – A 4-Channel Phase Coherent RTL-SDR for Passive Radar, Direction Finding and more onto DragonOS Focal (Lubuntu 20.04 based). A fork of the main code is required due to some changes in dependencies and packages. This fork is only meant for or at least tested on Ubuntu, Kubuntu, and Lubuntu 20.04.
I also show some issues you may experience due to poor quality USB cables, insufficient power, and/or issues with USB ports being used to power the KerberosSDR or connect to it.
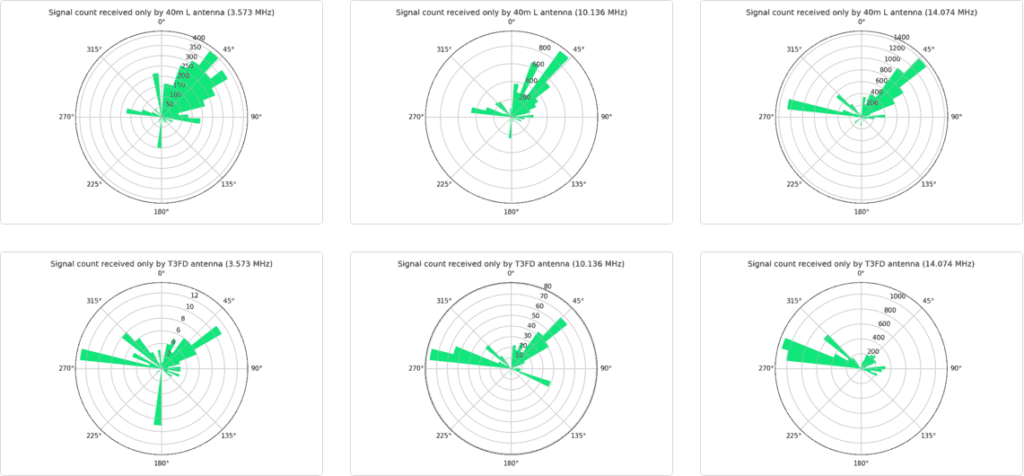
In this second video I show how to install and use RDFMapper with the KerberosSDR software and Android App. I also cover some common problems I've experienced with the current KerberosSDR Android App.
Recommended to watch the first video if you are planning to run the KerberosSDR on a PC or a SBC like the Raspberry Pi. This video and setup procedure can be adapted to use the Raspberry Pi/Android App instead of a PC.
I plan to make a couple more videos on this topic. By the end, it should be possible to have multiple KerberosSDR stations, both mobile and stationary, linked to one instance of RDFMapper over Zero Tier all simultaneously performing direction finding on one frequency.
KerberosSDR is our 4-channel phase coherent capable RTL-SDR unit that we previously successfully crowdfunded back in 2018. With a 4-channel phase coherent RTL-SDR interesting applications like radio direction finding, passive radar and beam forming become possible. It can also be used as 4 separate RTL-SDRs for multichannel monitoring. KerberosSDR is currently in stock and available on the Othernet store.