Unlocking Almost Any Vehicle with an SDR or Arduino
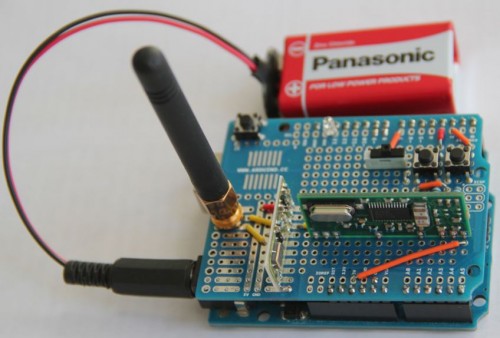
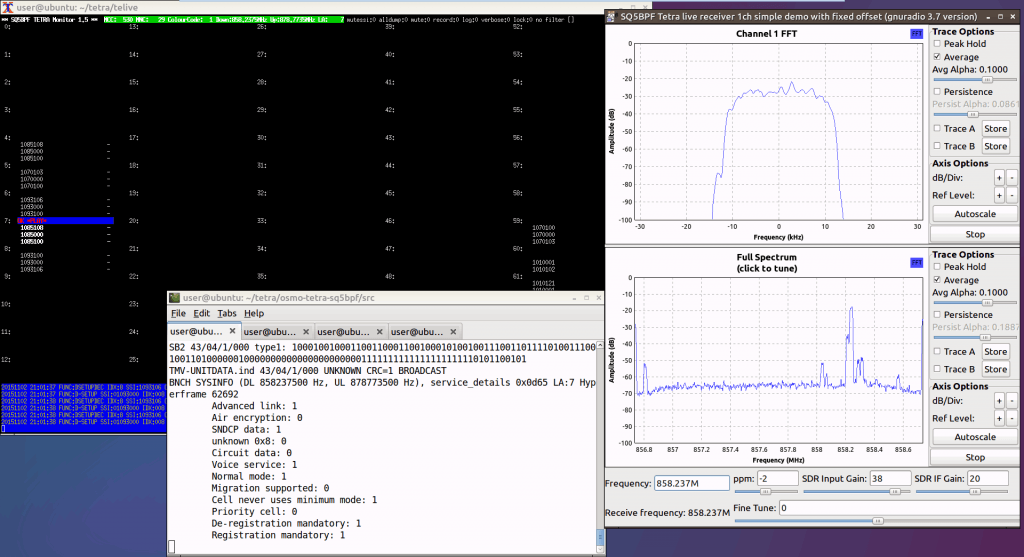
Earlier this week wired.com released a story indicating that researchers from the University of Birmingham have discovered two vulnerabilities that can be used to unlock almost any car. The first vulnerability concerns Volkswagen Group vehicles (VW, Audi, SEAT, Skoda) sold since 1995. Essentially their research found that the keyless entry systems of VW Group vehicles relies only on a few global master keys which they have been able to recover through reverse engineering of an undisclosed component used in a VW car. Then by sniffing the wireless key’s signal with an RF module or SDR like the RTL-SDR or HackRF they are able to recover the cryptographic algorithms used and then using the global key clone the wireless key signal, which can then be re-transmitted with a simple Arduino.
In their second research findings, the researcher’s write how they have been able to crack the Hitag2 rolling code system which is used in many vehicles such as Alfa Romeo, Chevrolet, Citroen, Dacia, Fiat, Ford, Lancia, Mitsubishi, Nissan, Opel, Peugot and Renault. Again, the hack works by sniffing a few wireless keyfob rolling code signals with an SDR or other device. Once the signals have been sniffed a simple laptop computer can reportedly break the encryption within one minute.
Here are some interesting excerpts from the conclusions of the paper:
The results of this paper show that major manufacturers have used insecure schemes over more than 20 years. Due to the widespread use of the analyzed systems, our findings have worldwide impact. Owners of affected vehicles should be aware that unlocking the doors of their car is much simpler than commonly assumed today. Both for the VW Group and the Hitag2 rolling code schemes, it is possible to clone the original remote control and gain unauthorized access to the vehicle after eavesdropping one or a few rolling codes, respectively. The necessary equipment to receive and send rolling codes, for example SDRs like the USRP or HackRF and off-the-shelf RF modules like the TI Chronos smart watch, are widely available at low cost.
A successful attack on the RKE and anti-theft system would also enable or facilitate other crimes:
– theft of the vehicle itself by circumventing the immobilizer system or by programming a new key into the car via the OBD port with a suitable tool
– compromising the board computer of a modern vehicle, which may even affect personal safety, e.g., by deactivating the brakes while switching on the wiping system in a bend
– inconspicuously placing an object or a person inside the car. The car could be locked again after the act
– on-the-road robbery, affecting the personal safety of the driver or passengers if they (incorrectly) assume that the vehicle is securely locked
Note that due to the long range of RKE systems it is technically feasible to eavesdrop the signals of all cars on a parking lot or at a car dealer by placing an eavesdropping device there overnight. Afterwards, all vulnerable cars could be opened by the adversary. Practical experiments suggest that the receiving ranges can be substantially increased: The authors of [18] report eavesdropping of a 433 MHz RFID system, with technology comparable to RKE, from up to 1 km using low-cost equipment.
The findings were presented at the Usenix Advanced Computing Systems Association conference during August 10-12, 2016 in Austin, TX. The white paper is titled “Lock It and Still Lose It—On the (In)Security of Automotive Remote Keyless Entry Systems” and can be downloaded here. Of course they did not publish the actual VW master keys in their paper and they have notified VW and NXP who make the Hitag2 chips in advance, noting that Hitag2 had actually been broken for several years prior.
Back in February we showed how Smay Kamkar was able to bypass rolling codes with his RollJam device, however the findings by these researcher’s is different in that they are actually able to generate new rolling codes, such that a simple Arduino with transmitter can act as a second wireless remote.