Running GR-GSM and IMSI Catcher on a Raspberry Pi 4 with Dragon OS
DragonOS is a ready to use Ubuntu Linux image that comes preinstalled with multiple SDR software packages. The creator Aaron also runs a YouTube channel showing how to use the various packages installed.
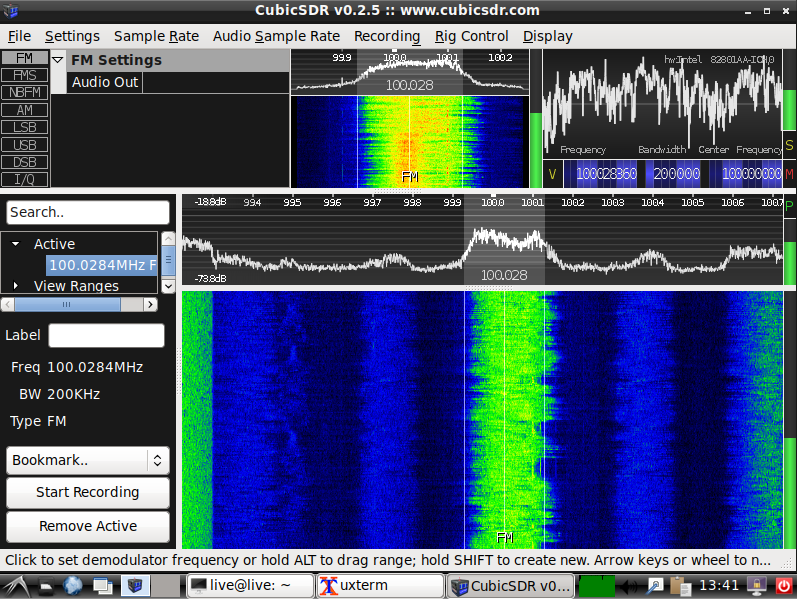
In his latest video Aaron tests his Pi64 image with GR-GSM and IMSI Catcher running with the GNU Radio 3.10 platform on a Raspberry Pi 4. He tests operation with an RTL-SDR and LimeSDR.
GR-GSM is a GNU Radio based program capable of receiving and analyzing mobile GSM data. We note that it cannot decode actual messages without additional information about the encryption key, but it can be interesting to investigate the metadata. GSM is mostly outdated these days, but still used in some areas by some older phones and devices. IMSI Catcher is a script that will record all detected GSM 'IMSI' numbers received by the mobile tower which can be used to uniquely identify devices.
Short video setting up and testing GR-GSM on DragonOS Pi64 w/ GNU Radio 3.10 and the RTL-SDR. The current DragonOS Pi64 build has GNU Radio 3.8 and all the necessary tools to accomplish what's shown in this video. If you'd like to test the build shown in this video, it's temporarily available here until I finish and put it on Source Forge.
https://drive.google.com/drive/u/1/fo...
A LimeSDR and DragonOS Focal's Osmo-NITB-Scripts was used to create the GSM900 lab environment. The RTL-SDR was able to see and decode the GSM900 network and although only briefly shown in the video, the IMSI Catcher script works.
Here's the fork used for this video and for testing. There's also a pull request on the main GR-GSM repo for this code to be added.