Breaking into cars wirelessly with a $32 homemade device called RollJam
At this years Def Con conference speaker Samy Kamkar revealed how he built a $32 device called “RollJam” which is able to break into cars and garages wirelessly, by defeating the rolling code protection offered by wireless entry keys. Def Con is a very popular yearly conference that focuses on computer security topics.
A rolling code improves wireless security by using a synchronized pseduo random number generator (PRNG) on the car and key. When the key is pressed the current code is transmitted, and if the code matches what the car is expecting the door opens. The seed for the PRNG in the car and key is then incremented. This prevents replay attacks.
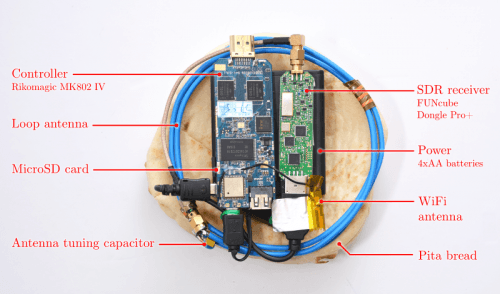
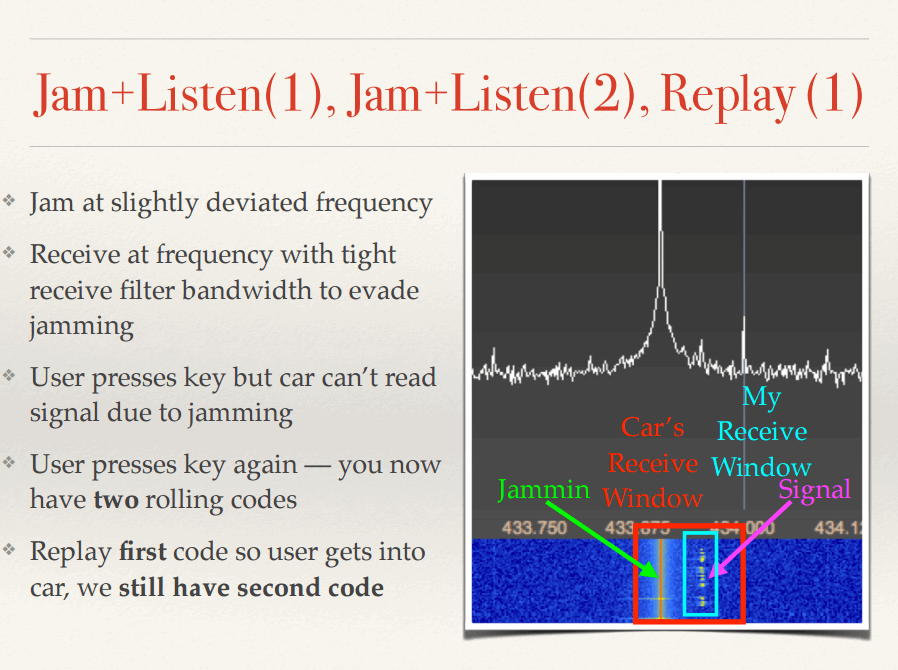
The RollJam hardware currently consists of a Teensy 3.1 microcontroller and two CC1101 433 MHz RF transceiver modules. It works by recording the wireless key signal, but at the same time jamming it so that the car does not receive the signal. When the key is pressed a second time the signal is first jammed and recorded again, but then the first code is replayed by the RollJam device. Now you have an unused code stored in RollJam that can be used to open the car. Samy shows how this works using an SDR and waterfall display graph in the following slide.
Samy’s full set of presentation slides can be downloaded from samy.pl/defcon2015. Also several large publications including networkworld.co, Wired.com and forbes.com have also covered this story with longer more in depth articles that may be of interest to readers.