Creating a wireless RTL-SDR server with a small OpenWRT WiFi Router
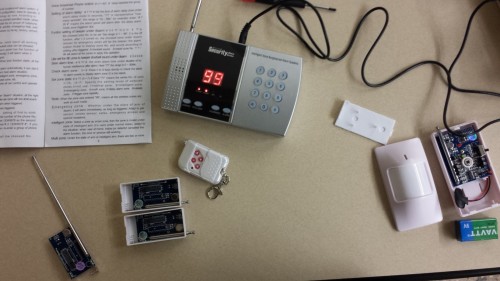
Over on his blog yo2ldk has been experimenting with creating a wireless RTL-SDR server by using a mini OpenWRT based WiFi router (page in Romanian, use Google Translate for English). The router he uses is the GL iNet 802.11n 150Mbps router, which is a mini WiFi router that only costs $27 USD and is about the same size as an RTL-SDR dongle. It is mainly intended for use with IoT devices, but it runs the Linux based OpenWRT firmware and has enough processing power and WiFi bandwidth to run an rtl_tcp server streaming at 2MSPS with no lag.
With an RTL-SDR connected and the router running rtl_tcp, the router can be placed anywhere there is power (yo2ldk uses a portable battery pack) to create a remote radio receiver with absolutely no coax cable losses. It’s WiFi range could be extended over long distances by using a directional Yagi antenna.
Using routers instead of mini computers like the recently released Raspberry Pi 3 may be a good option because they are very small, usually much cheaper, maybe be more power efficient, and may work better at transmitting the large amounts of data rtl_tcp requires.
In the future yo2ldk hopes to install everything into a shielded metal case, add an upconverter and also a solar panel for remote power.

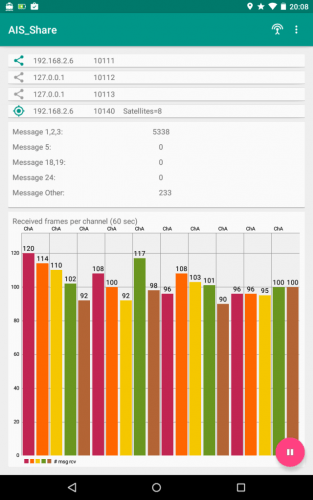
We note that if you have an old Android phone, then this could also potentially be used as a remote RTL-SDR server. To create an android RTL-SDR server simply download the Martin Marinov Android RTL2832U Driver from the Google play store. Find the IP address of your Android phone by going to Settings -> About Device -> Status -> IP Address. Then open the RTL2832U driver app and click on “Enable advanced mode (for debug & stream to PC)”. Initially the rtl_tcp string will have the code “-a 0.0.0.0”, simply change this to the IP address of your Android phone, for example “-a 192.168.1.15” and then click Start stream. Now on a remote PC connected to the same network open SDR# go to RTL-SDR (TCP) and type in the IP address of the phone and use the port number 14423. Click the play button and you should now be streaming your RTL-SDR data over WiFi.