Videos from DEFCON 22 Wireless Village Talks
Another security and hacking conference that recently finished is Defcon 2014. During this conference there was a “Wireless Village” were there were talks discussing all things related to radio frequency. During this conference there were many talks related to Software Defined Radio.
A list of all talks at the Defcon Wireless Village 2014 can be found on this page. The most interesting talks that we found related to SDR are shown below.
Hacking the Wireless World with Software Defined Radio
Presented by Balint Seeber, SDR Evangelist as Ettus Research. Balint presented a similar talk at Black Hat and the slides to go along with that can be found here.
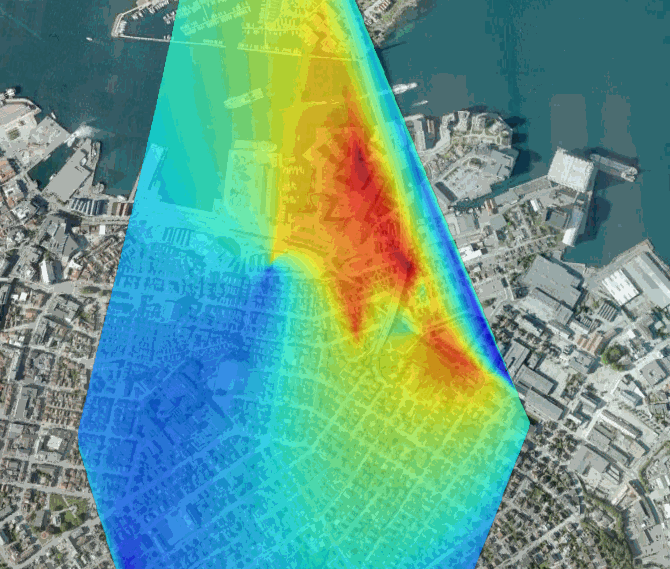
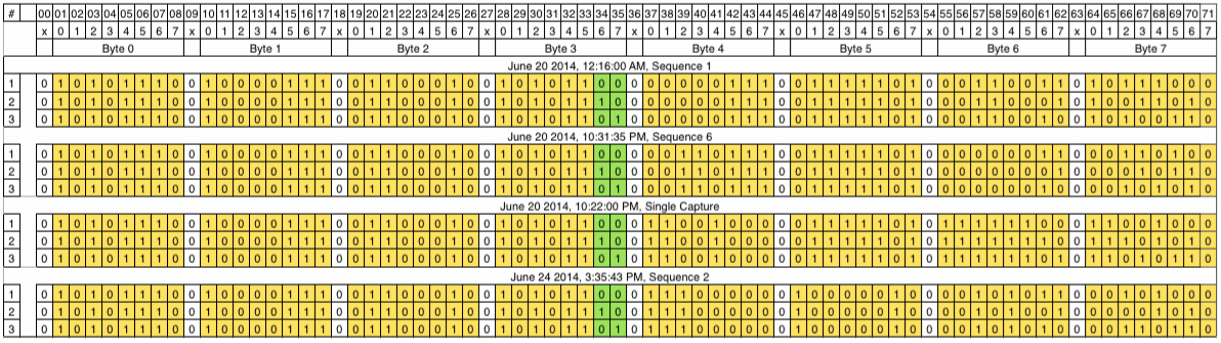
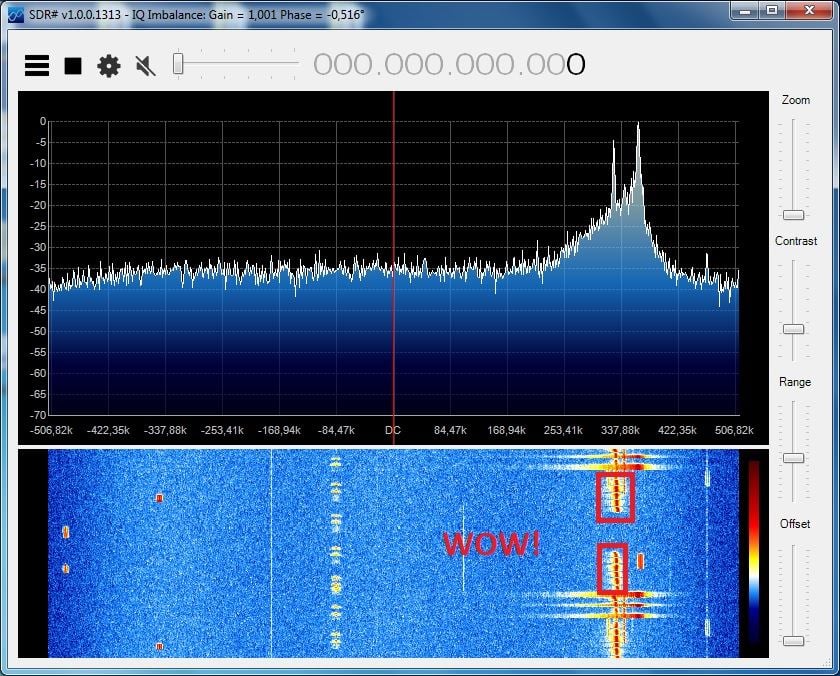
Ever wanted to spoof a restaurant’s pager system? How about use an airport’s Primary Surveillance RADAR to build your own bistatic RADAR system and track moving objects? What sorts of RF transactions take place in RFID systems, such as toll booths, building security and vehicular keyless entry? Then there’s ‘printing’ steganographic images onto the radio spectrum…
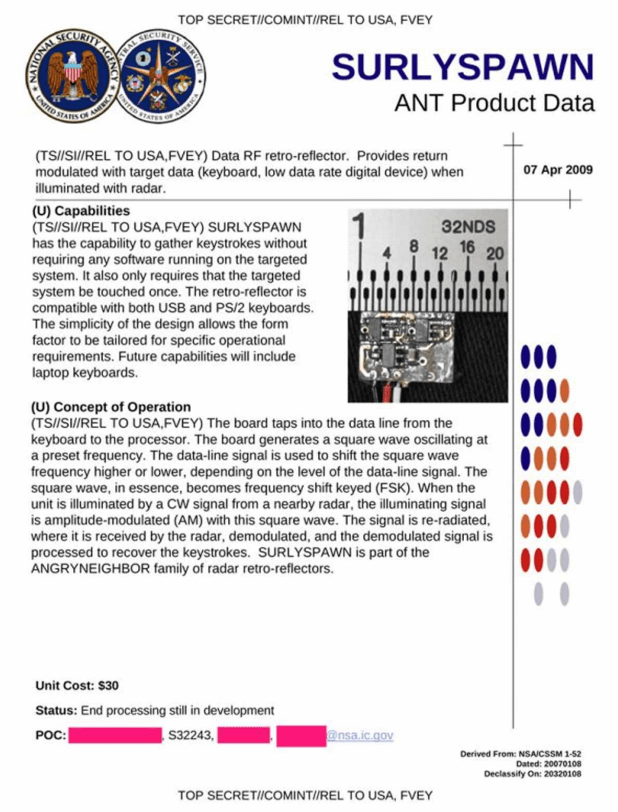
Wireless systems, and their radio signals, are everywhere: consumer, corporate, government, amateur – widely deployed and often vulnerable. If you have ever wondered what sort of information is buzzing around you, this talk will introduce how you can dominate the RF spectrum by ‘blindly’ analysing any signal, and then begin reverse engineering it from the physical layer up. I will demonstrate how these techniques can be applied to dissect and hack RF communications systems, such as those above, using open source software and cheap radio hardware. In addition, I’ll show how long-term radio data gathering can be used to crack poorly-implemented encryption schemes, such as the Radio Data Service’s Traffic Message Channel. If you have any SDR equipment, bring it along!
So ya wanna get into SDR?
Not explained through erotic interpretive dance, though could be, this presentation will cover the essentials for getting into the software defined radio hobby. Hardware requirements, distributed nodes, architecture designs, tips/tricks, random projects and common mistakes will be explained. This will be a technical talk that will be open for harassment, jokes, interaction and presented in a way that everyone will be able to take something away from it; wait, this is Vegas… but we’re hackers…
SDR Tricks with HackRF
HackRF and some other Software Defined Radio platforms can be used in creative ways. I’ll show methods, including a dirty trick or two, for using HackRF outside the advertised frequency range. I’ll also show how the HackRF design lends itself to use as an oscilloscope or function generator suitable for many hardware hacking tasks.
PortaPack: Is that a HackRF in your Pocket?
The PortaPack H1 transforms the HackRF One software-defined radio into a hand-held radio exploration tool. Spectrum analysis, monitoring and logging, and demodulation and injection of simpler digital modes will be demonstrated by Jared Boone, a HackRF project contributor.
PHYs, MACs, and SDRs
The talk will touch on a variety of topics and projects that have been under development including YateBTS, PHYs, MACs, and GNURadio modules. The talk will deal with GSM/LTE/WiFi protocol stacks.
SDR Unicorns
A panel with SDR Gurus Michael Ossmann, Balint Seeber and Robert Ghilduta.