Sniffing and Decoding NRF24L01+ and Bluetooth LE Packets with the RTL-SDR
Omri Iluz wrote in to us to let us know about his recent project which involves sniffing and decoding wireless packets at 2.4 GHz from NRF24L01+ and Bluetooth Low Energy (BTLE) transceivers. The NRF24L01+ is a popular wireless transceiver which is used in many common devices such as keyboards, mice, remote controls, toys and appliances.
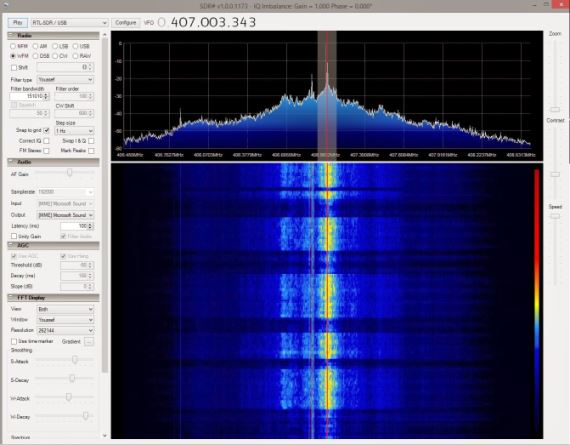
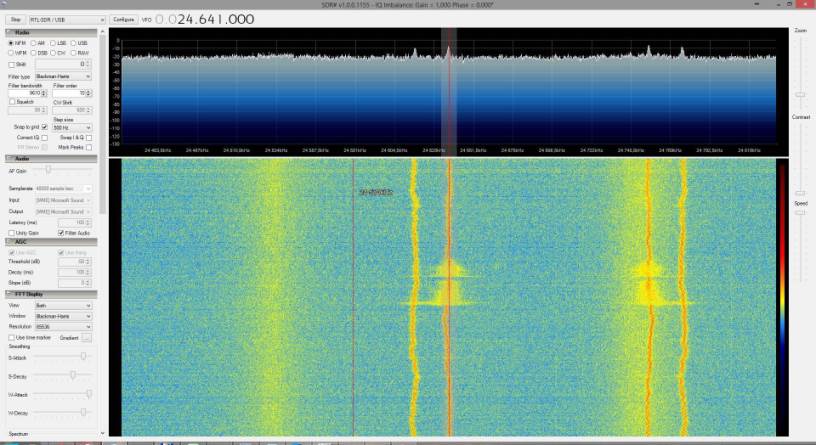
Since 2.4 GHz is out of any of the RTL-SDR’s receivable range, Omri used a cheap downconverter which he was able to buy from China using Aliexpress. The downconverter converts the 2.4 GHz signal into a lower frequency at around 400 MHz which is in the receivable range of the RTL-SDR.
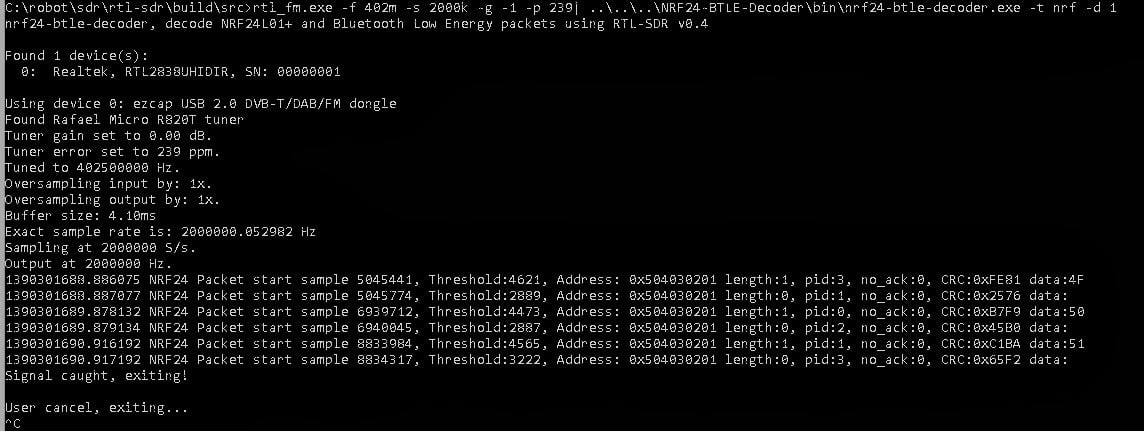
He was then able to use his NRF24-BTLE-Decoder software that he developed to convert the received data from the NRF24L01+ transceiver into a decoded packet by simply piping the output of RTL_FM into his program.
Since the NRF24L01+ uses hardware similar to the Bluetooth Low Energy (BTLE) protocol, Omri was able to modify his code to be able to also decode BTLE packets.