Reverse Engineering and Controlling a Pan-Tilt Camera Servo with an RTL-SDR and Arduino
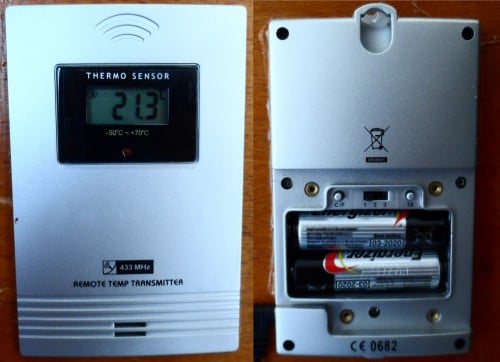
The ZIFON YT-500 is a pan-tilt tripod designed for mounting small cameras and smart phones. It also comes with an RF based 433 MHz wireless remote control that allows you to remotely control the positioning.
However, Konstantin Dorohov wanted to be able to control the camera positioning from his PC rather than through the remote control, so he set out to reverse engineer and clone the 433 MHz wireless control signal.
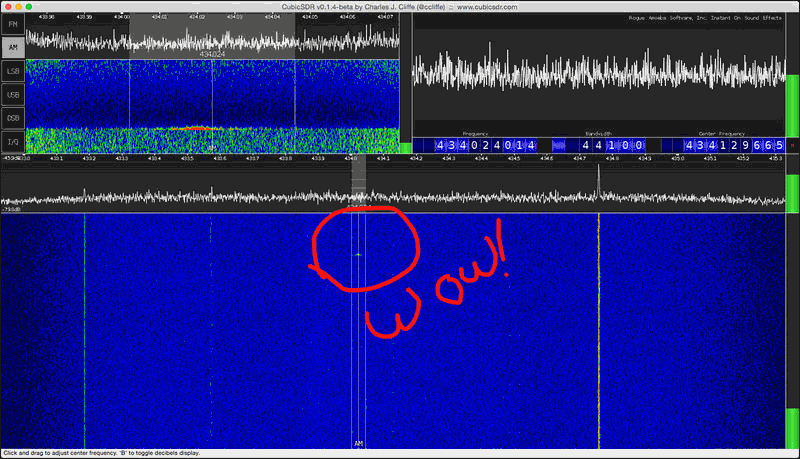
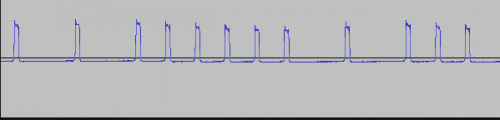
To do this he first used an RTL-SDR and SDR# to record the signals generated by each button press of the remote. He then opens the audio files in Audacity which allows him to inspect the signal's structure and determine some important information such as the preamble + payload timing and ON/OFF pattern.
Knowing this information he was then able to use an Arduino with a 433 MHz transmitter connected to replicate the signal exactly. His post contains the sample code that he used.