Finding GPS Signals from within the Noise Floor with an RTL-SDR
If you were to try to simply spot a GPS signal at 1.575 GHz in the spectrum on a waterfall in a program like SDR# you would probably fail to see anything. This is because GPS signals are very weak, and operate below the thermal noise floor. Only through clever processing algorithms can the actual signal be recovered.
Previously GPS and SDR enthusiast “e.p.” showed us on his blog how to use an RTL-SDR and the GNSS-SDRLIB and RTKLIB software to receive GPS and get a position lock.
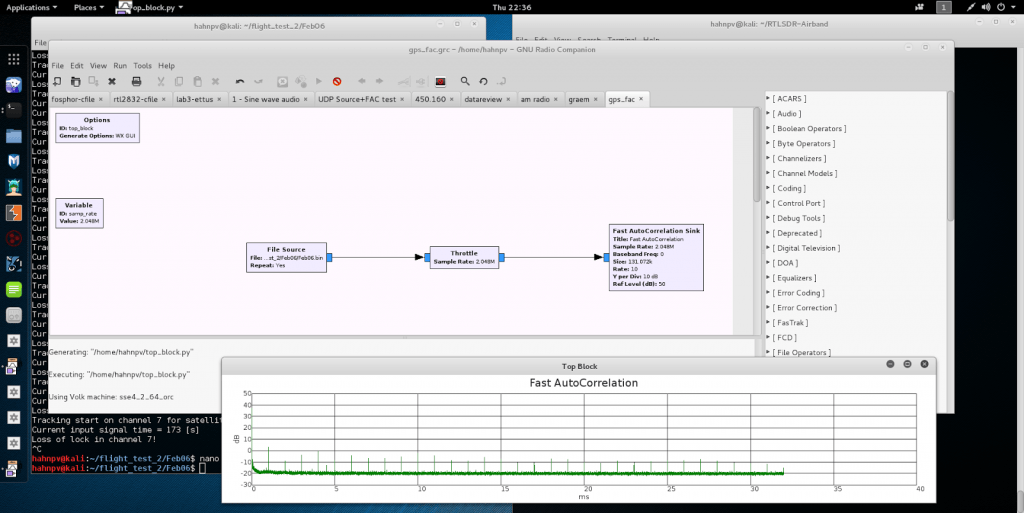
Now more recently e.p. has uploaded a post that explains a bit about how GPS signals are actually detected from below the noise floor. In his post he uses GPS data collected by his RTL-SDR dongle, and a fairly simple GNU Radio program consisting of a Fast AutoCorrelation Sink block.
With real data passed through the fast autocorrelation block he is able to observe GPS signal peaks that occur every millisecond. E.p. explains the reason for this:
Why every millisecond? The coarse/acquisition code for GPS (C/A) has a period of 1023 chips which are transmitted at a rate of 1.023 MBit/s. This results in period of 1 millisecond. BAM!
In a later post e.p. has also uploaded some sample GPS data collected with his RTL-SDR so anyone can play around with GPS decoding.