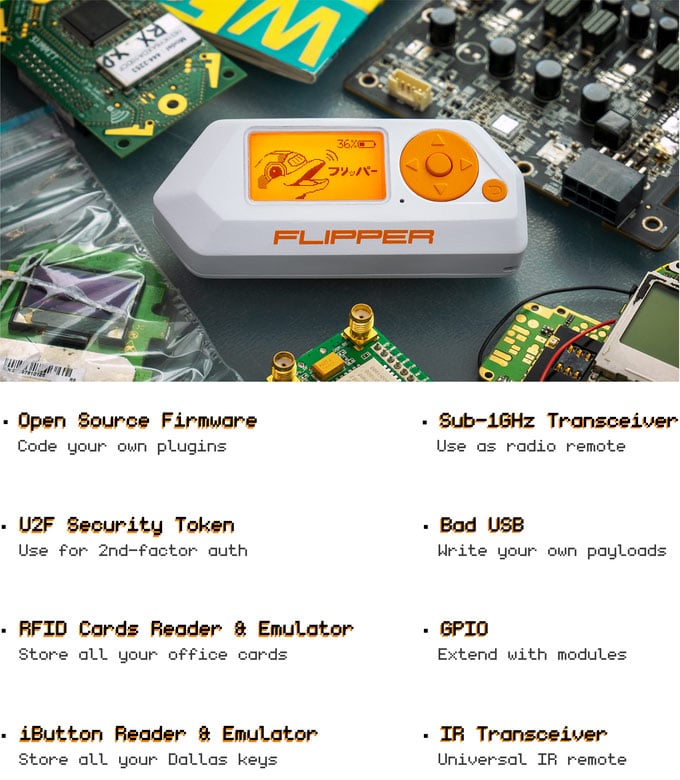
Flipper Zero Crowdfunding: An Open Source RF Pen Testing Tool For Hackers
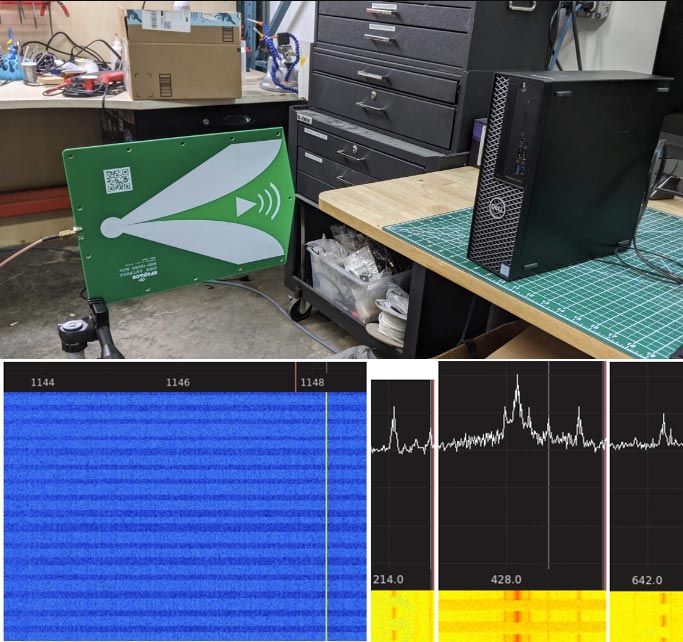
Flipper Zero isn't an SDR, but it is an interesting RF capable pentesting tool that is currently being crowdfunded, and we think it deserves a post. Based on a TI CC1101 transceiver chip, the Flipper Zero has a sub 1-GHz radio capable of doing things like emulating a garage door remote, transmitting digital signals like OOK/ASK/FSK/GFSK/MSK at 315/433/866 MHz, analyzing and decoding popular remote control algorithms like Keeloq, and reading and emulating 125 kHz RFID tags. And as the crowd funding stretch goals have already been reached, the hardware will also include a Bluetooth and NFC module.
In addition to the RF features, it has a 1-wire iButton/TouchMemory/Dallas key reader, can function as a U2F security token, has an infrared transceiver with learning feature for emulating IR remotes and has 12 5V tolerant GPIO pins available for expansion with modules such as interfaces, sensors, wireless modules and cellular modems. It can also emulate a USB slave device like a keyboard allowing you to deploy a keyboard payload.
Flipper Zero currently costs US$119 however it will soon jump to US$129 once the early bird special runs out. At the time of this post they already have 13,000 backers and have raised in excess of 2.5 million dollars. There is still 25 days left in the campaign.